Introduction
Remote work, cloud adoption, and distributed teams have permanently shattered the traditional "castle-and-moat" perimeter security model. Today's threats don't just come from outside the network. They originate inside it too.
The 2025 Verizon Data Breach Investigations Report identifies credential abuse as the top initial access vector in 22% of breaches, while IBM X-Force reports that identity-based attacks now make up 30% of total intrusions. Trusting anything on the network by default is no longer just risky — it's a liability.
ZTNA (Zero Trust Network Access) is the security model built for this new reality, operating on the principle of "never trust, always verify." This complete guide covers what ZTNA is, how it works, how it differs from VPNs, its key benefits, and practical steps to get started.
TLDR
- ZTNA grants access to specific applications only after verifying user identity, device health, and context—never the entire network
- Unlike VPNs, ZTNA uses least-privilege access with continuous verification—not just a one-time login check
- Reduces attack surface by keeping infrastructure invisible to unauthorized users and blocking lateral movement
- Essential for businesses with remote teams, cloud infrastructure, or BYOD environments
- Mature ZTNA deployments save organizations an average of $1 million in breach costs compared to those without it
What Is Zero Trust Network Access (ZTNA)?
Zero Trust Network Access is a category of technologies that enables secure remote access to applications and services based on strict, identity-driven access control policies. Trust is never assumed, and access is granted on a need-to-know basis only.
ZTNA operates on the Zero Trust principle: threats exist both inside and outside the network perimeter, so no user or device is automatically trusted regardless of location. Whether someone is sitting in the corporate office or connecting from a coffee shop, they must verify their identity and device posture before accessing any resource.
ZTNA evolved from the Cloud Security Alliance's Software-Defined Perimeter (SDP) specification, which introduced the "dark cloud" concept—an architecture where users cannot see or discover applications they don't have explicit permission to access. This stops attackers from mapping the environment entirely. Network resources stay invisible to unauthorized users, which significantly shrinks the attack surface.
How Does ZTNA Work?
Every ZTNA session follows the same sequence before access is granted:
- A user attempts to connect to an application
- The ZTNA service authenticates the user and evaluates context — identity, device posture, and location
- Only after verification is a secure, encrypted tunnel established directly to that specific application, never to the broader network
This architecture aligns with NIST Special Publication 800-207, which separates the control plane from the data plane and requires discrete authentication and authorization before establishing any session. These requirements map directly to four operating principles that define how ZTNA delivers access.
Core Principles of ZTNA
Application access, not network access
Users connect to specific applications. They are never placed on the network itself. Even if an attacker steals credentials, they can only reach the applications that user was explicitly permitted — every other resource stays out of reach.
Infrastructure that's invisible by design
Outbound-only connections mean corporate IP addresses and application infrastructure are never exposed to the internet. CISA advisories highlight active exploitation of internet-facing VPN gateways, and the 2025 Verizon DBIR notes a near eight-fold increase in edge device and VPN exploitation. ZTNA's "dark cloud" architecture removes the attack surface entirely — there's nothing for threat actors to discover or target.
Least-privilege, one-to-one access
Each authorized user gets access only to the specific apps they need. CrowdStrike's 2025 Global Threat Report puts the average adversary breakout time at just 48 minutes — fastest recorded: 51 seconds. ZTNA's individualized "segments of one" stop lateral movement before it starts, regardless of how fast an attacker moves.
Continuous trust verification
Traditional models authenticate once at login and trust the session from there. ZTNA continuously monitors behavior, device health, and session activity throughout the connection. If anomalies are detected, access is revoked in real time — trust is earned repeatedly, not assumed.

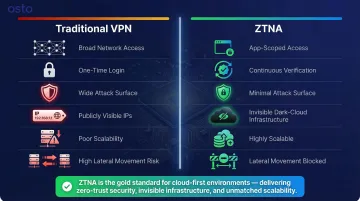
ZTNA vs. VPN: Key Differences
VPNs were originally designed to provide a private, encrypted tunnel to the full corporate LAN. This "all-or-nothing" access model creates significant security gaps in today's hybrid, multi-cloud environments. Once a user is in, they can reach anything on the network. Compromised credentials equal full network exposure.
Gartner predicts that by 2026, 70% of new remote access deployments will rely on ZTNA instead of traditional VPNs, reflecting the market's recognition that VPNs no longer meet modern security requirements.
Here's how the two approaches compare across the dimensions that matter most:
| Feature | Traditional VPN | Zero Trust Network Access (ZTNA) |
|---|---|---|
| Access Scope | Broad network access (flat network) | Application-scoped access (micro-tunnels) |
| Authentication | One-time at login | Continuous throughout session |
| Attack Surface | Broad — entire network exposed once authenticated | Minimal — only specific apps accessible |
| Visibility | Publicly visible IP addresses | Invisible to internet ("dark cloud") |
| Scalability | Poor — backhauling creates bottlenecks | Highly scalable — direct app connections |
| Lateral Movement | High risk if credentials compromised | Effectively neutralized via segmentation |
Three Critical VPN Failure Points
- Cloud migrations force VPN traffic to backhaul through corporate data centers before reaching cloud apps — creating latency and poor performance
- BYOD and unmanaged devices receive the same access as fully managed corporate machines, regardless of security posture
- Security policies cannot apply consistently across SaaS, on-premises, and cloud-native apps, leaving enforcement gaps
VPNs were built for a time when the corporate network had a clear boundary. In distributed, cloud-first environments, that boundary no longer exists — and ZTNA was designed specifically for that reality.
Key Benefits of ZTNA for Growing Businesses
Reduced Attack Surface
ZTNA never exposes the corporate network to users. Only the specific applications a user is authorized to access are reachable, giving attackers far less infrastructure to discover, probe, or exploit. This matters most for startups and scaling companies that lack large security teams to monitor a broad perimeter. Hiding resources from the public internet makes pre-attack reconnaissance significantly harder.
Stopping Lateral Movement
Even if a user's credentials are stolen, a ZTNA environment restricts the attacker to only the applications that user was permitted to access. They cannot scan the network or pivot to other systems. Given that identity-based attacks now make up 30% of total intrusions, this containment capability is critical. ZTNA limits the blast radius to a single user's access scope — stopping a credential breach from becoming a full network compromise.
Improved Visibility and Control
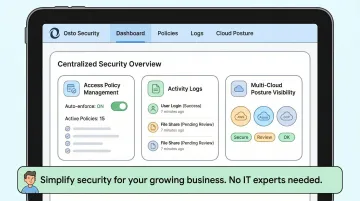
Centralized policy management gives security teams real-time visibility into who is accessing what, from which device and location. This enables faster detection and response to suspicious behavior. Platforms like Osto provide this centralized monitoring through dashboards designed for growing businesses, with audit logs and activity tracking built in for teams without dedicated IT staff.
Support for Remote and Hybrid Workforces
ZTNA enables secure access from any device, anywhere, without compromising on security. This makes it the right foundation for businesses with distributed teams or BYOD policies. Users connect directly to applications without backhauling traffic through corporate VPNs, improving performance and user experience while maintaining strict security controls.
Simpler Compliance Posture
Strict access controls, audit logs, and continuous monitoring make it easier to demonstrate compliance with data protection and privacy regulations. ZTNA's core principles directly support major frameworks:
| Regulatory Framework | How ZTNA Achieves Compliance |
|---|---|
| GDPR Article 32 | Implements technical measures ensuring ongoing confidentiality, integrity, and resilience of processing systems |
| HIPAA 45 CFR 164.312 | Enforces unique user identification, automatic logoff, and audit controls that record and examine activity |
| SOC 2 CC6 | Authorizes, modifies, or removes access based on roles with consideration to least privilege |
The financial case for compliance investment is clear: organizations with mature Zero Trust deployments average $4.15 million in breach costs, compared to $5.1 million for those without — a $1 million difference that compounds across regulatory fines, remediation, and reputational damage.

How to Implement ZTNA: A Practical Guide
Phase 1 — Start with Remote Access
Identify all remote users currently on VPN and map which private applications they actually need access to. Replace broad VPN access with ZTNA policies that grant access only to those specific apps. This maintains productivity levels during the transition while immediately reducing attack surface. Focus on high-risk user groups first—executives, finance teams, and third-party contractors.
Phase 2 — Introduce Microsegmentation and Expand Coverage
Define granular access policies for user groups based on roles. Prioritize segmenting high-value infrastructure and management systems first—databases, admin panels, and financial applications. Then expand ZTNA access to on-site users as well, applying the same identity-based policies universally across the organization. This creates consistency and eliminates the false trust granted to users simply because they're on the corporate network.
Phase 3 — Choose the Right ZTNA Solution
Solution selection can happen in parallel with your planning phases — waiting until deployment to evaluate vendors adds unnecessary delays. Evaluate solutions based on these criteria:
- Agent-based and agentless access: Supports BYOD and third-party users, not just managed corporate devices
- Cloud-native deployment: Fast setup without hardware investments or lengthy implementation cycles
- Identity provider integration: Connects with existing tools like Azure AD, Okta, or Google Workspace
- Device posture assessment: Continuously checks device health before and during access, not just at login
- Scalability without hardware: Grows with headcount and infrastructure without requiring new appliances
For growing businesses that want ZTNA as part of a broader security stack, Osto bundles it alongside web application protection, multi-cloud posture management, and threat detection in one platform. That means one dashboard, one vendor, and no separate integrations to maintain across tools.
Frequently Asked Questions
What is zero-trust network access?
ZTNA is a security framework that enforces strict, identity-based access control where no user or device is trusted by default. Access to specific applications is granted only after continuous verification of identity, device posture, and context throughout the session.
How is zero-trust network access different from a VPN?
VPNs grant broad network access once authenticated; ZTNA grants access only to specific applications on a least-privilege basis. Unlike VPNs, ZTNA continuously verifies trust throughout the session—not just at login—significantly reducing the attack surface.
How does a zero-trust approach impact network access?
Zero trust removes implicit trust entirely — every user and device must be verified before accessing any resource. The network becomes invisible to unauthorized users, and app-level segmentation actively blocks lateral movement between resources.
What are the core components of a ZTNA solution?
A complete ZTNA solution typically includes:
- Identity and access management (IAM) for user verification
- Device posture assessment for continuous security evaluation
- Application-level microsegmentation to isolate workloads
- Behavioral analytics for anomaly detection
- Policy enforcement engine that grants or revokes access based on real-time policy rules
Is ZTNA suitable for small businesses and startups, not just enterprises?
Yes—ZTNA is increasingly accessible and critical for smaller organizations, especially those with remote teams, cloud infrastructure, or limited IT staff. Cloud-native ZTNA solutions deploy quickly without requiring hardware and scale as the business grows, making enterprise-grade security achievable for startups and growing businesses.