What is Penetration Testing?
Penetration testing is an authorized simulated cyberattack performed by security professionals to identify and exploit vulnerabilities in your systems before real attackers can. Unlike automated scans that simply flag potential issues, pen tests actively demonstrate how an attacker could breach your defenses. This testing is always conducted with explicit permission and a clearly defined scope, ensuring legal compliance throughout.
The professionals conducting these tests are often called ethical hackers or pen testers. They use the same real-world attacker techniques as malicious hackers, but with a clear purpose: uncover blind spots that automated tools miss.
What separates pen testing from a basic vulnerability scan comes down to depth:
- Pen testers chain multiple weaknesses together, not just flag isolated issues
- They show exactly how far an attacker could move through your environment
- They replicate real attack paths — including lateral movement and privilege escalation
Understanding this distinction matters more now than it used to. Organizations no longer need to be enterprise-sized to become targets — attackers target growing businesses precisely because they assume defenses are weaker. Penetration testing helps level that playing field without requiring a large internal security team.
TLDR
- Penetration testing legally simulates cyberattacks to find and demonstrate real security weaknesses
- Pen testers actively exploit vulnerabilities — automated scanners only flag them
- Tests are categorized by knowledge level (black, white, or gray box) and target scope (web apps, networks, cloud infrastructure)
- The process follows five stages: reconnaissance, scanning, exploitation, maintaining access, and reporting
- Schedule tests after major system changes and to maintain compliance with PCI DSS, HIPAA, and GDPR requirements
Why Penetration Testing Matters for Your Business
Penetration testing goes beyond checking for known vulnerabilities—it simulates how a real attacker would chain multiple weaknesses together to cause material harm. This gives businesses a true picture of their risk exposure, not just a list of theoretical problems.
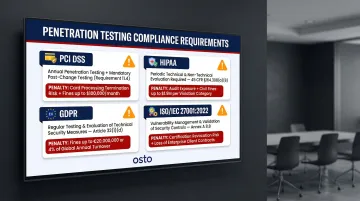
Compliance is mandatory, not optional. Major data security regulations explicitly require or strongly recommend periodic penetration testing:
- PCI DSS v4.0 mandates testing at least annually and after any significant infrastructure or application upgrade
- HIPAA requires periodic technical and nontechnical evaluation of security policies under 45 CFR § 164.308(a)(8)
- GDPR Article 32(1)(d) requires organizations to regularly test and evaluate the effectiveness of technical and organizational measures
- ISO/IEC 27001:2022 Annex A 8.8 requires validating controls and obtaining information about technical vulnerabilities through testing
Non-compliance carries real financial exposure. PCI DSS violations can result in fines and termination of card processing privileges, while GDPR violations carry administrative fines up to €20 million or 4% of total worldwide annual turnover.
The cost argument for proactive testing is equally clear. The IBM 2025 Cost of a Data Breach report found that organizations making extensive use of AI and automation in security achieved $1.9 million in cost savings compared to those that didn't, driven by faster identification and containment. Regular penetration testing enables exactly this kind of proactive posture.
Startups and scaling companies are frequent targets precisely because attackers assume weaker defenses. Penetration testing provides enterprise-grade security validation without requiring a large internal security team — at a fraction of the cost of responding to an actual breach.
Types of Penetration Tests
Penetration tests are categorized by the level of knowledge shared with the testing team before the engagement begins. Each approach serves different security objectives:
| Type | Tester Knowledge | Best Used When |
|---|---|---|
| Black Box | No prior access — tester performs full reconnaissance | You want to simulate how an external attacker with zero inside knowledge would approach your systems |
| White Box | Full access: source code, network diagrams, credentials, architecture docs | You need the deepest possible assessment and want code and configurations validated at every level |
| Gray Box | Partial access — user-level credentials or specific system context | You're modeling an insider threat or an attacker with stolen credentials; balances efficiency with realism |
Gray box is the most common approach in practice because it reflects a realistic compromise scenario without the time overhead of full black box reconnaissance.
Penetration Tests by Target
Web Application Pen Tests: Testers probe for OWASP Top 10 vulnerabilities in web apps, APIs, and related systems. This includes authentication failures, injection flaws (SQL injection, XSS), broken access control, security misconfigurations, and software supply chain failures. The 2025 OWASP update specifically highlights supply chain risks and mishandling of exceptional conditions as emerging threats.
Network Pen Tests: These come in two varieties:
- External tests target internet-facing servers, websites, and routers to identify how an outsider could breach your perimeter
- Internal tests simulate a malicious insider or attacker with stolen credentials already inside your network, showing how far lateral movement could extend
Cloud and Infrastructure Pen Tests: Cloud environments require specialized skills due to shared-responsibility models. Testers scrutinize configurations, IAM policies, storage permissions, and API exposures across AWS, Azure, and GCP. Each cloud provider has strict rules of engagement—DoS attacks are universally prohibited, and some activities require pre-approval.
Social Engineering and Personnel Tests: Testers use phishing, vishing (voice phishing), smishing (SMS phishing), or physical tailgating to find weaknesses in employee behavior and access control systems. This is the most overlooked attack surface—and often the easiest entry point for attackers.
The Penetration Testing Process: 5 Key Stages
Stage 1 — Reconnaissance
Pen testers begin by gathering as much information as possible about the target. They use both passive methods (OSINT, public records, social media, DNS lookups) and active methods (network scanning, direct interaction). The quality of this phase directly shapes what follows: thorough intelligence gathering uncovers entry points that superficial scans miss entirely.
Stage 2 — Scanning and Vulnerability Identification
Testers use technical tools to map the target's attack surface:
- Port scanners identify open services and potential entry points
- Vulnerability scanners discover specific exploitable weaknesses
- Packet analyzers examine network traffic for security gaps
This differs from fully automated vulnerability scanning because human analysis and prioritization guide the process. Testers don't just collect data—they interpret it to identify the most promising attack vectors.
Stage 3 — Exploitation
This is the actual attack phase. Testers attempt to exploit discovered vulnerabilities using techniques such as:
- SQL injection to access databases
- Cross-site scripting to compromise user sessions
- Brute force attacks against authentication systems
- Social engineering to trick users into revealing credentials
- Man-in-the-middle attacks to intercept communications
The goal is proof, not theory. A successful exploit shows exactly what an attacker could access — and what it would cost your organization if they did.

Stage 4 — Maintaining Access and Privilege Escalation
Pen testers simulate Advanced Persistent Threats (APTs) by attempting to deepen their foothold — escalating privileges, moving laterally across systems, and accessing sensitive data.
This phase answers a critical question: would your internal controls stop an attacker who has already made it past the perimeter?
Stage 5 — Reporting and Remediation Guidance
The pen test report is the primary deliverable that drives real security improvement. It includes:
- Executive summary for leadership
- Technical breakdown of vulnerabilities found
- Evidence of successful exploits
- Risk severity ratings
- Specific, prioritized remediation recommendations
Testers also clean up at the end — removing any backdoors or tools planted during the engagement to ensure the test itself doesn't leave the environment exposed.
Common Penetration Testing Tools
Professional pen testers select tools based on the scope and target of each engagement. There's no single universal toolkit—a network pen test requires different tools than a web application or social engineering test.
Reconnaissance Tools:
- Nmap for port scanning and network discovery
- Wireshark for packet analysis and protocol inspection
Exploitation & Scanning Tools:
- Metasploit for automating known exploits and testing vulnerabilities
- Nessus for comprehensive vulnerability assessment
- Burp Suite for web application testing and proxy manipulation
- OWASP ZAP for intercepting and inspecting web application messages
Credential-Cracking Tools:
- Hashcat for advanced password recovery
- John the Ripper for password security auditing
Most testers run these tools on Kali Linux, an OS built specifically for security testing that comes preloaded with most of them.
Automated tools speed up scanning and known-exploit detection, but human analysis remains essential for identifying business logic flaws, chaining vulnerabilities, and uncovering what scripted tools miss.
Penetration Testing vs. Vulnerability Assessment
The key functional difference: a vulnerability assessment identifies and flags known weaknesses, while penetration testing actively exploits them to demonstrate real impact. One maps your exposure; the other proves whether that exposure can be turned against you.
The PCI Security Standards Council explicitly clarifies: "A vulnerability assessment simply identifies and reports noted vulnerabilities, whereas a penetration test attempts to exploit the vulnerabilities to determine whether unauthorized access or other malicious activity is possible."
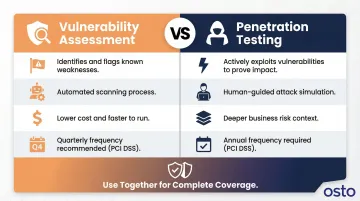
Organizations benefit from using both together rather than treating them as alternatives:
- Faster and more frequent: Vulnerability assessments cost less to run and support ongoing monitoring — PCI DSS requires quarterly scans
- Deeper and context-rich: Pen tests validate actual business risk in ways automated scans can't — required at least annually under PCI DSS
Osto's AI-powered web scanner provides continuous automated vulnerability detection that complements periodic pen tests. It runs continuously between scheduled pen testing engagements, so gaps in coverage don't become gaps in security. The scanner uses machine learning algorithms to categorize vulnerabilities by severity and provides specific remediation guidance—giving growing businesses actionable next steps rather than a raw list of findings.
What Happens After a Penetration Test
Once the report lands, the security team sorts findings by severity and exploitability, then builds a prioritized remediation plan. Not everything needs fixing at once — risk-based prioritization is standard practice. Start with critical and high-severity vulnerabilities that could lead to unauthorized access or data exposure.
Typical remediation responses by finding type:
- Web application findings → new WAF rules, stricter input validation, or rate limiting
- Network findings → firewall reconfiguration or Zero Trust adoption
- Social engineering findings → employee security training and access control tightening
- Cloud misconfigurations → IAM policy updates, storage permission reviews, and security group hardening
Re-testing is a required step in any responsible pen testing cycle. Follow-up verification confirms that identified vulnerabilities are properly fixed and haven't introduced new issues in the process. PCI DSS explicitly mandates retesting to verify that corrections were successfully implemented.
The work doesn't stop after remediation. Between annual pen tests, continuous posture management helps organizations catch new misconfigurations before they become exploitable gaps. Osto's Cloud Security Posture Management covers Azure, AWS, and GCP in a single consolidated view, with built-in security checks and step-by-step remediation guidance — so your security posture doesn't drift between testing cycles.
Frequently Asked Questions
What are the 5 stages of penetration testing?
The five stages are: reconnaissance (gathering target information), scanning/vulnerability identification (mapping the attack surface), exploitation (actively attacking vulnerabilities), maintaining access/privilege escalation (simulating persistent threats), and reporting (documenting findings with remediation guidance).
What are the three types of penetration tests?
The three knowledge-level types are: black box (no prior information, simulates an external attacker), white box (full system access and documentation provided for comprehensive analysis), and gray box (partial knowledge, most commonly used in practice to simulate insider threats).
What is penetration testing in information security?
Penetration testing is an authorized simulated attack conducted by ethical hackers to find and exploit vulnerabilities before real attackers can. The goal is to evaluate and improve an organization's security posture by demonstrating real-world impact, not just identifying theoretical risks.
How is penetration testing different from a vulnerability assessment?
Vulnerability assessments use automated scanning to identify and flag known weaknesses, while pen testing actively exploits those weaknesses to prove real-world impact. Pen testing provides deeper insight but is typically performed less frequently—annually versus quarterly for vulnerability scans.
How often should penetration testing be performed?
Most security frameworks, including PCI DSS, require pen tests at least once per year and after any significant change—such as new systems, major code releases, or infrastructure updates.
Who performs penetration testing?
Pen tests are best performed by third-party ethical hackers or certified security professionals holding credentials such as OSCP, CEH, or GPEN. Outside expertise uncovers blind spots internal teams often miss, and most compliance frameworks require testers to be independent from the systems they assess.