Introduction
Cybercriminals don't wait for permission. They scan the internet constantly, probing for exploitable weaknesses — and they often find them before defenders do, turning every unpatched flaw into a potential breach.
As businesses scale, adding cloud infrastructure, remote access, web applications, and third-party integrations, their attack surface expands fast. The challenge isn't just identifying weaknesses: it's maintaining visibility across all of them without a large IT department.
The stakes are higher than ever. IBM's 2024 Cost of a Data Breach report reveals that the global average cost of a data breach has reached a record $4.88 million, representing a 10% increase from the previous year. Meanwhile, Verizon's 2024 Data Breach Investigations Report documented a 180% surge in vulnerability exploitation, which now accounts for 14% of all breaches. Most alarming: approximately 60% of data breaches stem from known, unpatched vulnerabilities — patches existed but weren't deployed in time.
This guide breaks down what vulnerability assessment is, how the process works, which tools to use, and the best practices that keep your defenses ahead of attackers.
TL;DR
- Vulnerability assessment systematically identifies, classifies, and prioritizes security weaknesses before attackers exploit them
- Covers networks, hosts, applications, databases, and cloud infrastructure using automated scanning tools
- Different from penetration testing—VA discovers and reports flaws; pen testing actively exploits them
- Regular assessments are compliance mandates under PCI DSS, GDPR, HIPAA, and NIST frameworks
- Effective programs prioritize based on exploitability, business impact, and threat intelligence, not severity scores alone
What Is a Vulnerability Assessment?
A vulnerability assessment is the systematic process of identifying, evaluating, classifying, and reporting on security weaknesses across an organization's IT environment. NIST defines it as the "systematic examination of an information system or product to determine the adequacy of security measures, identify security deficiencies, provide data from which to predict the effectiveness of proposed security measures, and confirm the adequacy of such measures after implementation."
In this context, a vulnerability is any weakness in software, hardware, configurations, or processes that a threat actor could exploit for unauthorized access or data exfiltration. These flaws span your entire technology stack: misconfigured cloud storage buckets, outdated application libraries, weak authentication mechanisms, and unpatched operating systems.
Most assessments rely on automated scanning tools that compare your environment against databases like the Common Vulnerabilities and Exposures (CVE) catalog (MITRE) and the National Vulnerability Database (NVD) (NIST). Threat intelligence feeds add real-time data on actively exploited vulnerabilities, making thorough assessments practical even for lean security teams.
Types of Vulnerability Assessments
Different environments require different scan types. A comprehensive assessment typically combines multiple approaches rather than relying on a single method:
- Network-Based Scans: Target wired and wireless infrastructure to identify open ports, unsecured protocols, and rogue hosts across your network perimeter and internal segments
- Host-Based Scans: Examine servers, workstations, and endpoints for missing OS patches, weak local configurations, and file integrity issues using authenticated (credentialed) access
- Application Scans: Test web applications, APIs, and source code for injection flaws, authentication bypasses, session management exploits, and other OWASP Top 10 vulnerabilities
- Database Scans: Assess database management systems for misconfigurations, missing patches, weak access controls, and SQL injection risks
- Wireless Network Assessments: Detect rogue access points, weak encryption protocols, and unauthorized wireless devices
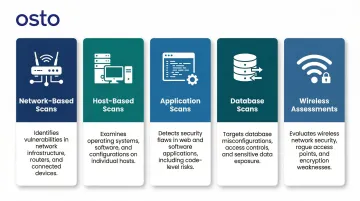
Because web applications are a dominant entry point for attackers, organizations must ensure their assessment scope explicitly includes application-layer testing, not just underlying network infrastructure.
Vulnerability Assessment vs. Penetration Testing vs. Vulnerability Management
These three terms are often confused, but they serve distinct purposes:
| Approach | Primary Question | Method |
|---|---|---|
| Vulnerability Assessment | What weaknesses exist? | Automated scanning and classification across your environment |
| Penetration Testing | Can this actually be exploited? | Manual and automated attack simulation to test real-world impact |
| Vulnerability Management | Are we continuously reducing risk? | Full lifecycle program: assess, prioritize, remediate, monitor |
Vulnerability assessment is the critical first step in a vulnerability management program. Without it, you can't prioritize remediation or track progress — you're essentially patching blind.
Why Vulnerability Assessments Are Critical for Modern Businesses
As businesses scale, their attack surface expands fast. Every new cloud instance, remote access endpoint, web application, API, and third-party integration creates additional entry points for attackers. The challenge is maintaining visibility across all of them without a large IT department dedicated to security operations.
The window between vulnerability disclosure and active exploitation is shrinking. The 2024 Verizon DBIR reveals that attackers begin mass scanning for vulnerabilities in the CISA Known Exploited Vulnerabilities catalog within just five days of disclosure.
Meanwhile, organizations take an average of 55 days to remediate 50% of critical vulnerabilities once patches become available. That 55-day gap creates a wide-open window for ransomware operators.
Vulnerability assessments link directly to business outcomes:
- Avoiding data breaches: The $4.88 million average breach cost represents not just direct expenses but lost customer trust and competitive advantage
- Reducing downtime: Exploited vulnerabilities often lead to system outages that impact revenue and operations
- Maintaining customer trust: Demonstrating proactive security measures reassures customers and partners
- Avoiding regulatory penalties: Non-compliance with security standards can result in significant fines and legal consequences
Beyond risk reduction, vulnerability assessments are a legal requirement. Standards including PCI DSS, GDPR, HIPAA, and NIST SP 800-53 all mandate regular scanning and documentation.
PCI DSS v4.0, for instance, requires internal vulnerability scans at least quarterly, with high-risk findings resolved and rescans confirming remediation. GDPR Article 32(1)(d) requires data controllers to implement "a process for regularly testing, assessing and evaluating the effectiveness of technical and organisational measures."
Regulators enforce these requirements with real consequences. The Icelandic Data Protection Authority fined InfoMentor ISK 3,500,000, explicitly citing "insufficient follow-up and testing of security measures" as the cause of the breach. HHS OCR settled with MMG Fusion for $10,000 following a breach affecting 15 million individuals, with a primary violation being "failing to conduct an accurate and thorough risk analysis." For growing businesses without dedicated security teams, a structured vulnerability assessment program is often the most direct path to both compliance and defensibility.
How to Conduct a Vulnerability Assessment: Step-by-Step
The assessment process should be repeatable, documented, and treated as an ongoing program rather than a one-time exercise. The most common failure points include skipping proper scoping, ignoring low-severity findings that chain together, and lacking clear ownership of remediation efforts.
Step 1 – Define Scope and Inventory Assets
Identify all assets in scope: servers, endpoints, applications, databases, cloud resources, and network components. Document what software, operating systems, and configurations are deployed on each. Without a clear understanding of your internet-accessible footprint, it's impossible to defend against threats.
Determine the business impact of each asset to calibrate prioritization later. Key context factors include:
- Whether the asset stores PII or financial data
- Whether it's customer-facing or processes transactions
- How its compromise would affect operations or compliance
These factors become critical when deciding which vulnerabilities to remediate first.
Step 2 – Run Vulnerability Scans
Use automated scanning tools to search for known vulnerabilities across the defined scope. Scanners match findings against vulnerability databases such as CVE and use behavioral analysis to flag misconfigurations. The NVD enriches CVE entries with critical metadata including Common Vulnerability Scoring System (CVSS) scores, Common Weakness Enumeration (CWE) types, and applicability statements.
Scans should be scheduled regularly and, for maximum coverage, run both internally (behind the firewall) and externally (from an attacker's perspective). Authenticated scans that use credentials to view local configurations, registry keys, and installed software versions sharply reduce false positives and uncover deeper flaws that unauthenticated scans miss.
Step 3 – Analyze and Prioritize Vulnerabilities
Analyze findings for root cause, exploitability, and business impact. CVSS provides a numerical score ranging from 0.0 to 10.0 based on intrinsic vulnerability characteristics. However, the NVD explicitly warns that "CVSS is not a measure of risk" and only assesses Base metrics. Base scores assume the reasonable worst-case impact in an unmitigated environment.
To prioritize effectively, enrich Base scores with environmental context:
- CVSS score: Intrinsic severity of the vulnerability
- Active exploitation: Whether exploits exist in the wild (check CISA's KEV catalog)
- Asset sensitivity: Criticality of the affected system and data it handles
- Ease of exploitation: Complexity required to exploit the flaw
- Patch availability: Whether a fix exists and can be deployed
A vulnerability on an isolated internal server with compensating controls poses far less risk than the same vulnerability on a public-facing web server, even if their Base scores are identical.
Step 4 – Remediate and Mitigate
Once vulnerabilities are prioritized, the response falls into three approaches depending on risk level and operational feasibility:
Full Remediation: Patching or fixing the root cause eliminates the vulnerability entirely. This is the preferred approach when patches are available and can be deployed without disrupting operations.
Mitigation: When immediate patching isn't possible, reduce exploitability through compensating controls such as firewall rules, network isolation, web application firewall (WAF) policies, or disabling vulnerable services.
Risk Acceptance: For low-risk findings where remediation cost outweighs impact, document a formal decision to accept the risk. NIST SP 800-39 defines risk acceptance as appropriate when identified risk is within organizational risk tolerance, requiring explicit understanding and approval by senior leaders.
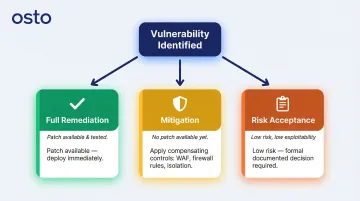
Remediation is a cross-team effort involving security, IT operations, and development. Operational silos are one of the most common reasons vulnerabilities persist. CISA recommends remediating Critical vulnerabilities within 15 calendar days of initial detection and High vulnerabilities within 30 calendar days.
Step 5 – Report and Continuously Improve
A useful vulnerability assessment report should contain:
- List of findings with severity scores and CVSS metrics
- Affected assets and their business context
- Remediation recommendations with specific steps
- Proof of concept details where appropriate
- Tracking of previously identified issues to monitor progress
Assessments must be repeated on a regular cycle—not just annually. CISA recommends at least weekly scanning for internet-accessible systems. Build scanning into CI/CD pipelines and cloud deployment processes to catch vulnerabilities before they reach production. According to GitLab's 2024 Global DevSecOps Report, 55% of security professionals discover vulnerabilities only after code is merged into a test environment, which is far too late in the development lifecycle.
Vulnerability Assessment Tools and Best Practices
Organizations rely on several core tooling categories:
Vulnerability Scanners: Automated scanning against CVE databases (examples include OpenVAS/Greenbone for network scanning and OWASP ZAP for web applications)
Application Testing Frameworks: Simulate attacks like SQL injection, XSS, and broken authentication. Two primary approaches exist:
- SAST (Static Application Security Testing): Analyzes source code before deployment to find syntax violations and security vulnerabilities early in development
- DAST (Dynamic Application Security Testing): Tests running applications from the outside by injecting malicious payloads, simulating real-world attack scenarios
Patch Management Tools: Automate remediation across distributed systems, tracking which patches have been deployed and which systems remain vulnerable
Threat Intelligence Platforms: Contextualize findings with real-time exploit data, helping teams understand which vulnerabilities are actively being weaponized
Attack Surface Management Tools: Provide continuous visibility into external-facing assets, discovering shadow IT and forgotten systems
Open-source tools offer flexibility and cost-effectiveness but require more manual maintenance. Enterprise platforms provide integrated, automated workflows better suited for scaling teams without large security staff. Choose tools that integrate with your existing workflows rather than forcing teams to adopt new processes.
For web application scanning specifically, Osto's AI-powered scanner uses machine learning algorithms to achieve 2x faster scan execution with improved detection accuracy, reducing the manual effort required for application security testing. It automatically categorizes findings by severity and provides remediation guidance for each discovered issue.
Best Practices for Effective Vulnerability Assessments
Scan continuously, not annually: Critical systems need continuous or weekly scanning — not just a once-a-year review. Include new assets the moment they are deployed. PCI DSS requires quarterly scans at minimum, but a risk-based approach typically demands more.
Embed security into CI/CD pipelines: Build vulnerability assessment into your development workflow so issues are caught before code reaches production. A DevSecOps culture makes security a shared responsibility across development, operations, and security teams. The OWASP Top 10 — the standard reference for critical web application risks — should anchor your development security practices.
Prioritize findings, don't chase every flag: Refine scan configurations to reduce false positives, then apply risk-based prioritization instead of treating all findings equally. Fix these first:
- Vulnerabilities actively being exploited in the wild
- Issues affecting critical or customer-facing assets
- Findings with available patches or documented mitigations
How Osto Can Help
Osto is a unified cybersecurity platform built specifically for growing businesses, startups, and scaling enterprises that need comprehensive security coverage without a large IT department. The platform brings together web application scanning, cloud security posture management, and real-time threat protection in one centralized dashboard.
Osto's Cloud Security Posture Management (CSPM) is directly relevant to vulnerability assessment for cloud environments. It provides automated discovery and posture analysis across Azure, AWS, and GCP in a single consolidated inventory — covering 35+ resource types including VMs, storage buckets, databases, IAM roles, security groups, and container services.
Built-in security checks identify misconfigurations and exposure risks that traditional network-based scans often miss, generating findings with step-by-step remediation guidance.
The operational benefits for teams conducting regular assessments include:
- AI-driven adaptive profiling that learns your traffic patterns and reduces false positives over time
- 2x faster scan execution with improved detection accuracy, so assessments run more often without extending scan windows
- Real-time visibility through a centralized dashboard showing vulnerability counts, severity breakdowns, and attack paths
- Audit logs that track all administrative activities and changes for compliance documentation and oversight

The result is enterprise-grade vulnerability management that security-lean teams can actually operate — without hiring a dedicated in-house analyst to make sense of the findings.
Frequently Asked Questions
What are the four steps in vulnerability assessment?
The four core steps are: vulnerability identification (scanning for weaknesses), vulnerability analysis (verifying findings and removing false positives), risk assessment and prioritization (ranking by severity and business impact), and remediation (fixing or mitigating confirmed issues). Some frameworks include reporting as a fifth step.
What is the vulnerability assessment?
Vulnerability assessment is the systematic process of identifying and reporting on security weaknesses across an organization's IT environment. It uses automated scanning tools that compare systems against vulnerability databases to discover flaws before attackers can exploit them.
What are the five types of vulnerability assessment?
The five main types are:
- Network-based scans — target network infrastructure and services
- Host-based scans — examine operating systems and endpoints
- Application scans — test web apps and APIs for coding flaws
- Database scans — assess configurations and access controls
- Wireless assessments — detect rogue access points and weak encryption
What is application vulnerability assessment?
Application vulnerability assessment focuses on identifying security weaknesses in web applications, APIs, and software. It detects issues like SQL injection, cross-site scripting (XSS), broken authentication, insecure session management, and misconfigurations.
Which is better, SAST or DAST?
Neither is strictly better—they complement each other. SAST analyzes source code before deployment for early detection, while DAST tests running applications to simulate real-world attacks. Most organizations use both: SAST during development, DAST before and after release.
What does OWASP stand for?
OWASP stands for Open Worldwide Application Security Project—a nonprofit best known for the OWASP Top 10, a ranked list of the most critical web application vulnerabilities. It serves as a standard benchmark in vulnerability assessments and secure development practices.