Introduction
Growing businesses face a stark reality: attack surfaces are expanding rapidly—more endpoints, more cloud workloads, more entry points for attackers, yet security budgets and team sizes haven't kept pace. The average breakout time for cybercriminals has plummeted to just 29 minutes in 2025, with the fastest recorded lateral movement occurring in a mere 27 seconds. When attackers move this fast, manual security response is no longer viable.
EDR (Endpoint Detection and Response) and XDR (Extended Detection and Response) are the two detection and response solutions at the center of this problem. For organizations building or maturing their security posture, choosing between them is one of the most consequential decisions you'll make.
EDR gives you focused, fast endpoint protection, ideal for lean teams securing employee devices. XDR gives you broader cross-environment visibility, essential when your infrastructure spans endpoints, networks, cloud, and identity systems. With 82% of attacks now entirely malware-free and bypassing traditional defenses, the wrong choice can leave critical gaps or waste resources you can't spare. This guide breaks down how each solution works, where they differ, and how to determine which one fits your environment.
TL;DR
- EDR monitors and responds to threats at the device level using behavioral analysis and real-time alerts
- XDR expands EDR's scope to cover networks, cloud, email, and identity in a unified platform
- EDR focuses on endpoints; XDR correlates signals across multiple security layers for broader visibility
- EDR fits organizations with lean security teams and limited infrastructure — XDR adds value as environments grow
- XDR typically builds on EDR as one of its data sources — the two are complementary, not competing
EDR vs XDR: Quick Comparison
| Feature | EDR | XDR |
|---|---|---|
| Scope/Coverage | Endpoints only (laptops, desktops, servers, mobile devices) | Endpoints + network + cloud + email + identity systems |
| Data Sources | System logs, file activity, process execution, local network traffic | Endpoint data + firewall logs, cloud control planes, identity providers, email gateways |
| Detection Approach | Behavioral analysis and anomaly detection at device level | Cross-domain correlation of signals from multiple security layers |
| Response Capabilities | Isolate endpoint, kill process, quarantine file, rollback changes | Suspend user identity, block network ports, isolate cloud workloads, quarantine emails |
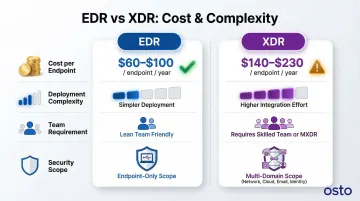
| Complexity and Cost | Lower cost ($60–100 per endpoint annually), simpler deployment | Higher cost ($140–230 per endpoint annually), requires integration effort |
| Best Fit | Small to mid-sized businesses, lean security teams, endpoint-focused threats | Enterprises with multi-cloud infrastructure, complex environments, cross-domain attack risk |
XDR does not make EDR obsolete. Most XDR platforms ingest EDR data as one layer of their broader telemetry — think of EDR as the foundation and XDR as the expanded structure built on top of it. EDR suits lean teams with tighter budgets, while XDR requires either a larger security team or a managed service layer to deliver its full value. Without that support, the added complexity can work against you.
What is EDR?
Endpoint Detection and Response (EDR) is a security solution that continuously monitors endpoint devices—including laptops, desktops, servers, and mobile devices—collecting behavioral and event data to detect, investigate, and respond to threats in real time. EDR evolved from traditional antivirus because signature-based tools couldn't keep up with behavioral and fileless threats that leave no malware signature to detect.
How EDR Works
EDR operates through agents installed on each endpoint that collect telemetry: process activity, file changes, network connections, and system events. This data flows to a centralized console where behavioral analysis, machine learning, and threat intelligence feeds flag anomalies.
When a threat is detected, EDR triggers response actions such as endpoint isolation, process termination, or file quarantine—often automatically.
Core Capabilities of EDR
EDR provides five essential capabilities:
- Continuously monitors device activity to catch threats as they occur
- Proactively hunts for indicators of compromise that automated tools might miss
- Prioritizes alerts based on severity and context to cut through noise
- Performs forensic analysis of security events to trace attack methods
- Automatically contains threats through isolation, process termination, or quarantine
This matters most against threats that bypass preventive tools—ransomware, fileless malware, and insider attacks at the device level. In one verified case, Microsoft Defender for Endpoint detected an Akira ransomware attack via anomalous RDP logons, automatically contained the compromised user account, and prevented encryption across all protected devices.

Key Limitations of EDR
EDR only sees what happens on endpoints. This means lateral movement across a network, cloud-based attacks, or email-delivered threats that don't touch a monitored endpoint can go undetected. Additionally, EDR can generate alert fatigue if not properly tuned—SOC teams receive an average of 4,484 alerts daily, with 67% going uninvestigated due to overwhelming volume.
Use Cases of EDR
Where EDR fits best:
- Organizations in early stages of building detection and response capabilities
- Businesses with a moderate number of endpoints and a small but active security team
- Industries where endpoint attacks are the primary threat vector (professional services, SMBs, early-stage startups)
- Organizations with limited security budgets
- Businesses without multi-cloud or complex network infrastructure
- Teams wanting to establish a security foundation before scaling to broader solutions
For organizations where endpoints are the primary attack surface, EDR delivers focused protection without requiring a full security operations team to run it. When threats expand beyond the device layer—into networks, cloud environments, or email—that's where EDR's visibility ends and XDR becomes relevant.
What is XDR?
Extended Detection and Response (XDR) is an evolution of EDR that unifies threat detection and response across multiple security layers—endpoints, networks, cloud workloads, email systems, and identity providers—into a single, correlated view. XDR was designed to break down the security silos created when organizations run multiple separate tools that don't share data with each other.
How XDR Works
XDR ingests telemetry from across the security stack: EDR data, network traffic, cloud logs, email security events, and identity data. It applies advanced analytics and machine learning to correlate signals across these sources, surfacing high-confidence alerts with full attack chain context. This cross-domain correlation means XDR can detect sophisticated attacks—like lateral movement after an initial endpoint compromise—that EDR alone would miss.
For example, in a 2025 campaign, the threat group Scattered Spider used help-desk voice phishing to compromise Microsoft Entra ID and single sign-on accounts. From there, they pivoted into integrated SaaS applications and targeted VMware vCenter environments for ransomware deployment.
Because the attack unfolded entirely within cloud identity and virtualization planes, endpoint-only EDR tools had no telemetry to detect it—ransomware was already deployed before any alert fired.
Key Capabilities of XDR
XDR provides comprehensive security capabilities:
- Ingests telemetry from endpoints, networks, cloud, email, and identity systems into one data stream
- Connects related events across security layers to build complete attack narratives
- Automatically stitches related alerts together, cutting manual correlation work
- Groups thousands of noisy alerts into a handful of actionable incidents
- Coordinates response actions across multiple tools and layers simultaneously
XDR can replace the need for separate SIEM, UEBA, and NDR tools, consolidating detection and response into a single workflow.
XDR's Trade-offs
XDR requires more initial setup and integration effort, demands skilled personnel or a managed service layer to operate effectively, and typically carries higher cost than standalone EDR. Organizations report that XDR platforms range from $140–230 per endpoint annually, compared to $60–100 for EDR. The complexity is justified when the environment's attack surface spans multiple domains—but for smaller organizations with simpler infrastructure, this complexity can become a burden rather than a benefit.
Use Cases of XDR
Where XDR fits best:
- Growing organizations with multi-cloud infrastructure (AWS, Azure, GCP)
- Businesses adopting remote work at scale
- Enterprises suffering from alert fatigue across disconnected security tools
- Security teams looking to accelerate threat investigation by consolidating visibility into one console
- Organizations where attackers routinely exploit multiple attack surfaces—a pattern seen in 87% of incidents
A Forrester Total Economic Impact study found that organizations transitioning to XDR reported 244% ROI, an 85% reduction in Mean Time to Remediate (MTTR), and a 70% drop in investigation caseloads—numbers that reflect just how much overhead fragmented tooling creates.
Key Differences Between EDR and XDR
Coverage and Scope
EDR's visibility ends at the endpoint boundary—it cannot see network traffic, cloud-layer activity, email threats, or identity-based attacks that don't manifest on a monitored device. XDR's scope is enterprise-wide, correlating data from every layer of the security stack into a unified view. Think of EDR as security cameras covering only the front door; XDR is a full building surveillance system.
Detection Methodology
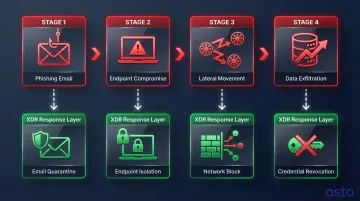
EDR detects threats using behavioral analysis, anomaly detection, and threat intelligence applied to endpoint-level data. XDR does the same, but enriches detection by correlating signals across multiple sources simultaneously.
This cross-domain view is what exposes complex, multi-stage attacks that look harmless in isolation—for example: phishing email → endpoint compromise → lateral movement → data exfiltration. Each step might clear a single-layer check; only cross-layer correlation connects them.
Data Aggregation and Correlation
EDR correlates data only within a single endpoint's activity stream. XDR aggregates data across endpoints, networks, cloud workloads, identities, and email, then applies cross-domain correlation to build complete attack narratives. This is the core architectural difference—XDR's detections are richer in context and generate fewer isolated, hard-to-interpret alerts.
That richer context directly reduces alert fatigue. By grouping related signals into enriched incidents, XDR cuts the noise considerably—one organization dropped from 25,000 manual alert reviews per quarter to just 4,500, an 80% improvement driven by better correlation alone.
Response and Automation
EDR automates response actions at the endpoint level—isolating devices, terminating processes, quarantining files. XDR coordinates response across multiple layers: it can simultaneously isolate an endpoint, block a network segment, revoke cloud access credentials, and flag a suspicious email sender as part of a single incident response workflow.
That coordinated response compresses timelines dramatically. A Forrester study on Palo Alto Networks Cortex XSIAM found automated correlation reduced Mean Time to Remediate by 85%—dropping detection and remediation from over six hours to just 40–50 minutes.
Cost and Resource Requirements
EDR is more accessible for organizations with limited budgets and small security teams—deployment is simpler and management overhead is lower. XDR's broader capabilities come with higher licensing costs and operational complexity. For organizations without a large in-house security team, managed XDR (MXDR) services can bridge this gap, but at added cost.
Typical pricing looks like this:
| Tier | Solution | Annual Cost Per Endpoint |
|---|---|---|
| Entry-level EDR | Basic packages | $60–$100 |
| Mid-tier EDR | Standard solutions | $80–$100 |
| Enterprise XDR | Full suites | $140–$230 + storage fees |
However, the long-term ROI of XDR can be strong for organizations dealing with tool sprawl and alert fatigue. Manual alert triage costs U.S. enterprises an estimated $2.6 billion annually, and organizations with fragmented SOCs spend 40% more on operational labor than those with consolidated tooling. XDR addresses both: Microsoft Defender XDR customers reported $9.6 million saved over three years by decommissioning legacy agents and cutting SIEM data ingestion costs by 20%.
Which Solution Should You Choose?
The right choice depends on four factors: the complexity and breadth of your environment, the size and maturity of your security team, your budget, and your current pain point.
Decision Framework
Choose EDR if:
- You're a startup or small business primarily focused on securing employee devices
- You have a lean team and limited budget
- Your infrastructure is primarily endpoints without complex multi-cloud architecture
- Your primary threats are localized malware and ransomware
- You need to establish a security foundation before scaling
Choose XDR if:
- You're a scaling business with multi-cloud infrastructure (AWS, Azure, GCP)
- You have remote workforces requiring secure access across multiple systems
- You're suffering from alert fatigue across disconnected security tools
- Your security team spends excessive time manually correlating events
- You need to eliminate security silos and gain unified visibility
Real-World Transition Scenario
Consider a fast-growing SaaS company that starts with 50 employees and deploys EDR to protect laptops and desktops. At this stage, EDR provides robust protection against endpoint threats—ransomware, phishing-delivered malware, and insider threats.
As the company scales to 200 employees and migrates workloads to AWS and Azure, the attack surface expands dramatically. Employees access applications through SSO, data lives in cloud storage, and microservices run in Kubernetes clusters.
An attacker who compromises a single endpoint can now pivot into cloud identity systems and move laterally through cloud infrastructure — activity that EDR has no visibility into.
At this stage, transitioning to XDR makes strategic sense. XDR correlates endpoint activity with cloud access logs, identity provider events, and network traffic.
When an attacker compromises an endpoint and attempts to escalate privileges in AWS, XDR detects the anomalous cloud activity and ties it back to the endpoint compromise. The coordinated response isolates the endpoint, suspends the user's cloud credentials, and blocks lateral movement before it spreads.

Concrete takeaway: If you're still primarily managing endpoints, EDR is your foundation. If your infrastructure has grown beyond endpoints, XDR gives you the visibility to match.
Closing the Cloud Security Gap
For growing businesses, endpoint and network-level detection is only part of the picture. Cloud infrastructure introduces a separate layer of exposure — misconfigurations, over-permissioned identities, and unmonitored resources — that neither EDR nor XDR fully addresses on its own.
Platforms like Osto can fill this gap. Osto provides unified posture management and real-time threat monitoring across AWS, Azure, and GCP, automatically surfacing misconfigurations and exposure risks with remediation guidance. Whether you've deployed EDR or XDR, Osto ensures your cloud layer doesn't become a blind spot.
Decision Clarity
There is no universal winner between EDR and XDR — the right choice depends on where you are in your security maturity journey. EDR is the essential foundation. XDR is the logical next step when your environment and threat surface outgrow what endpoint-level visibility alone can address. Pick the tool that matches your actual risk, not the one that sounds more advanced.
Frequently Asked Questions
What is the difference between XDR and EDR?
EDR focuses exclusively on endpoint-level detection and response, monitoring devices like laptops and servers. XDR extends this coverage to include networks, cloud environments, email, and identity data—correlating signals across all these layers into a unified security view.
Can XDR replace EDR?
XDR can functionally replace standalone EDR because most XDR platforms include endpoint telemetry as a core data source. However, the transition requires more resources and budget, and for smaller organizations with simpler infrastructure, EDR alone is often the better starting point.
What is XDR in cyber security?
XDR is an integrated security platform that collects and correlates threat data from multiple security layers—endpoints, networks, cloud, email, and identity. It detects advanced threats that no single security tool would catch on its own.
Is EDR the same as a firewall?
No. A firewall controls network traffic at the perimeter, blocking or allowing connections based on rules. EDR monitors activity on endpoint devices to detect and respond to threats that have already bypassed perimeter defenses.
Which is better for small businesses, EDR or XDR?
Most small businesses should start with EDR as a cost-effective, manageable foundation for endpoint security. Consider XDR as you grow and adopt multi-cloud infrastructure, remote workforces, or more complex security tool stacks.
What is the difference between EDR, XDR, and MDR?
EDR is the technology for endpoint detection and response. XDR extends that coverage across multiple security domains. MDR (Managed Detection and Response) is a service model where a third-party team operates your EDR or XDR for you, making it a practical option for organizations without a dedicated security team.