AI Web Vulnerability Scanning
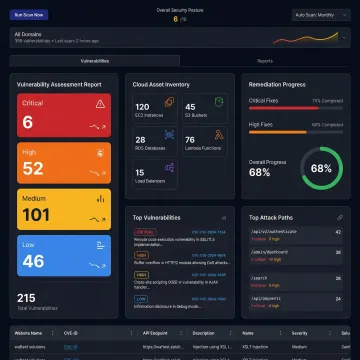
AI-powered scanner that analyzes website security, scores overall protection, categorizes vulnerabilities by severity, and delivers precise remediation guidance with 2x faster scan execution and scheduled reporting.
Discover hidden weaknesses before attackers do. Osto's vulnerability scanning services combine AI-powered detection, multi-cloud posture analysis, and web application scanning to deliver a comprehensive security assessment. From misconfigurations to OWASP Top 10 threats, get actionable insights and step-by-step remediation guidance to strengthen your defenses and stay ahead of evolving cyber risks.

Comprehensive scanning and assessment solutions to identify, prioritize, and remediate security weaknesses across your entire digital infrastructure.
AI-powered scanner that analyzes website security, scores overall protection, categorizes vulnerabilities by severity, and delivers precise remediation guidance with 2x faster scan execution and scheduled reporting.
Automated discovery and security assessment across AWS, Azure, and GCP — covering 35+ resource types with actionable misconfiguration findings, enriched metadata, and real-time posture evaluation in a unified dashboard.
Real-time threat detection for HTTPS traffic using OWASP Top 10 checks, DDoS protection, bot mitigation, and API anomaly detection — all powered by a high-performance Nginx reverse-proxy architecture.
End-to-end Vulnerability Assessment and Penetration Testing delivered as a managed service, combining automated scanning with expert analysis to uncover and validate security gaps across your environment.
Continuously discover, map, and monitor your infrastructure's security posture across cloud environments, surfacing configuration risks and compliance gaps before they become exploitable vulnerabilities.
Integrate security assessments early in the development lifecycle to identify vulnerabilities at the source, reducing remediation costs and preventing security debt from accumulating in production environments.
Modern businesses face a rapidly expanding attack surface — from web applications and APIs to sprawling multi-cloud infrastructure. Osto's vulnerability scanning services use machine learning algorithms and automated discovery to surface misconfigurations, exposure risks, and OWASP-class threats across your entire environment. Each finding comes with precise location details, affected endpoints, and step-by-step remediation guidance — so your team spends less time investigating and more time fixing. Whether you're a startup hardening your first deployment or a scaling enterprise managing Azure, AWS, and GCP simultaneously, Osto delivers enterprise-grade security assessment in a centralized, easy-to-use dashboard.
Osto delivers comprehensive, intelligent security assessment built for businesses that need enterprise-grade protection without the complexity.
Machine learning algorithms categorize vulnerabilities by severity and deliver 2x faster scans with improved detection accuracy.
Unified posture visibility across AWS, Azure, and GCP in a single dashboard — ideal for businesses with distributed cloud infrastructure.
Every finding includes precise affected endpoints and step-by-step fix guidance, so teams act immediately rather than investigate.
One consolidated platform for web scanning, cloud posture, API protection, and audit logs — no large IT department required.
A dedicated team committed to simplifying cybersecurity for modern businesses.
Osto was built with a clear mission: to make enterprise-grade cybersecurity accessible to new age businesses — startups, growing companies, and scaling enterprises that need robust protection without the overhead of a large security team. The platform has grown rapidly through continuous innovation, progressing from core web application protection to a full-spectrum security platform covering AI-powered vulnerability scanning, multi-cloud posture management, Zero Trust Network Access, and endpoint detection. Key milestones include launching multi-cloud CSPM support across Azure, AWS, and GCP within weeks of each other, introducing AI-driven adaptive web protection profiling, and delivering 2x faster scan performance. Osto's philosophy is simple: comprehensive security should be centralized, intelligent, and within reach of every ambitious organization.
Vulnerability scanning services are automated or semi-automated processes that inspect your digital assets — websites, APIs, cloud infrastructure, and endpoints — to identify security weaknesses, misconfigurations, and exposure risks. Tools like Osto's AI-powered scanner analyze your environment, score overall security health, categorize findings by severity, and provide step-by-step remediation guidance to close gaps before attackers can exploit them.
Talk to an Osto security expert for a personalized assessment of your environment.
Scanning aligned to globally recognized web application security standards
Verified integration and posture management across AWS, Azure, and GCP
Recognized for machine learning-driven vulnerability detection and adaptive protection
Submit your details and an Osto security specialist will reach out to discuss a vulnerability assessment tailored to your infrastructure — no obligation, no jargon.
You can also send us a quick email at connect@osto.one.
You can also send us a quick email at connect@osto.one.