Without knowing where your vulnerabilities are, every security investment is essentially a guess. A cybersecurity assessment transforms this guesswork into a clear, prioritized security strategy based on actual risk. This article covers what a cybersecurity assessment is, why it's non-negotiable for growing businesses, how it works step by step, and how to get started without a large in-house security team.
TL;DR
- A cybersecurity assessment systematically identifies vulnerabilities, threats, and risks across your IT environment
- Skipping one means you're likely protecting the wrong things while leaving critical assets exposed
- The threat landscape evolves faster than most security programs, which is why regular reassessment isn't optional
- Osto automates asset discovery and continuous monitoring, making ongoing assessment practical for teams without a large security department
What Is a Cybersecurity Assessment?
A cybersecurity assessment is a systematic evaluation of your organization's IT environment—including systems, data, applications, and user behavior—to identify vulnerabilities, threats, and the risks they create. The goal is a clear picture of your current security posture and actionable steps to improve it.
Assessments typically involve several activities:
- Vulnerability scanning to identify technical weaknesses
- Penetration testing to simulate real-world attacks
- Configuration reviews to spot misconfigurations
- Access control audits to examine who has access to what
- Compliance gap checks to measure adherence to frameworks
Not every assessment includes all of these—scope depends on your business objectives and maturity level.
Assessment Approaches
Growing businesses typically start with one of four approaches:
| Approach | How It Works | Best For |
|---|---|---|
| Qualitative | Categorizes risk as high, medium, or low using expert judgment | Teams without deep security expertise |
| Quantitative | Models financial impact using metrics like potential loss per incident | Organizations with data maturity to support it |
| Compliance-driven | Maps controls to frameworks like NIST, ISO 27001, or SOC 2 | Businesses facing regulatory or contractual requirements |
| Continuous automated | Monitors infrastructure in real time, surfacing risks as they emerge | Cloud-native teams needing ongoing visibility |

Most growing businesses benefit from starting with a foundational qualitative or compliance-mapped assessment, then evolving toward continuous monitoring as infrastructure scales.
Why Your Business Needs a Cybersecurity Assessment
Most Breaches Exploit Basic Gaps
The majority of breaches at growing businesses aren't caused by sophisticated zero-day exploits—they exploit basic gaps like misconfigurations, overprivileged accounts, unpatched software, or exposed cloud resources. IBM's 2024 Cost of a Data Breach Report found that IT failures and human error caused 49% of all breaches. An assessment surfaces these blind spots before attackers do.
Vulnerability exploitation surged 34% in 2025, largely driven by unpatched edge devices and VPNs, according to the Verizon 2025 Data Breach Investigations Report. These are known, preventable issues—exactly what assessments are designed to catch.
Prioritization Prevents Wasted Resources
Without an assessment, resource-constrained teams often react to headlines or vendor pitches rather than actual risk. You might invest in advanced threat detection while leaving publicly accessible S3 buckets unmonitored. An assessment creates a ranked list of what to fix first based on real business impact, so limited budgets go where they matter most.
Compliance Is a Business Enabler
Industries from SaaS to fintech to healthcare face increasing regulatory requirements. Three frameworks make this explicit:
- GDPR Article 32 requires "a process for regularly testing, assessing and evaluating the effectiveness of technical and organisational measures"
- HIPAA mandates risk analyses under 45 CFR 164.308(a)(1)(ii)(A)
- PCI DSS v4.0.1 requires internal vulnerability scans "after any significant changes" and targeted risk analyses reviewed at least annually
Regular assessments create the audit trail and control evidence these frameworks demand, reducing legal and financial exposure from non-compliance.
The Cost Case Is Clear
The average US data breach now costs $10.22 million, according to IBM's 2025 Cost of a Data Breach Report. Organizations that extensively used security AI and automation saved an average of $1.9 million and reduced breach lifecycles by 80 days. Identifying and patching a vulnerability before exploitation is far cheaper than incident response, legal exposure, and reputation repair combined.
External Stakeholders Demand Proof
Investors, customers, and partners increasingly ask about security posture. Having a current assessment demonstrates that security is managed proactively, which matters when pursuing enterprise contracts, closing funding rounds, or onboarding security-conscious customers.
How a Cybersecurity Assessment Works: Step by Step
A cybersecurity assessment works best as a structured cycle — not a one-time event. Done right, it becomes the backbone of your security improvement program.
Step 1 – Define Scope and Identify Assets
The assessment starts by defining what's in scope: which systems, data, applications, cloud environments, and users will be evaluated. For growing businesses with multi-cloud infrastructure, this includes cloud accounts (AWS, Azure, GCP), SaaS tools, APIs, and remote endpoints.
Skipping thorough asset inventory is the single most common failure point. According to SentinelOne, 32% of cloud infrastructure sits idle and untracked, with each unmonitored asset carrying an average of 115 known vulnerabilities. You cannot protect what you don't know exists.
Step 2 – Identify Threats and Vulnerabilities
This step involves scanning for technical weaknesses — misconfigurations, unpatched software, excessive permissions, weak authentication — and mapping the threat actors most likely to target your environment using frameworks like MITRE ATT&CK as a reference.
Distinguish between vulnerabilities (weaknesses in your environment) and threats (the methods attackers use to exploit them). More than 31% of cloud breaches stem from misconfiguration and manual errors. In cloud and SaaS environments, identity is the primary attack surface: 99% of cloud identities are over-privileged, according to ReliaQuest.
Step 3 – Analyze and Calculate Risk Levels
For each vulnerability-threat combination, the team estimates likelihood of exploitation and potential business impact, combining these into a risk score. The most defensible approach ties risk to real-world consequences — downtime, data loss, regulatory fines, or reputational damage — not just technical severity scores like CVSS alone.
CVSS v4.0 measures technical severity, not business risk. The NIST National Vulnerability Database is explicit: "CVSS is not a measure of risk." CISA recommends pairing CVSS with contextual frameworks like Stakeholder-Specific Vulnerability Categorization (SSVC), which prioritizes patching based on actual exploitation evidence and business impact.
Step 4 – Develop a Prioritized Remediation Plan
The team organizes findings into a risk register, ranking them by business impact and exploitability — not technical severity alone. The output is a prioritized action plan: which vulnerabilities to fix first, which to accept or transfer through cyber insurance, and which require new controls.
A cost-benefit lens should apply—a $2M fix for a $500K risk exposure may not be the right call. This step ensures limited resources address the highest-impact risks first.
Step 5 – Implement Controls and Measure Results
This is the tactical phase: deploying patches, hardening configurations, enabling MFA, updating access controls, or onboarding security tooling. Each remediation should be tied to a measurable outcome — reduced attack surface, mean time to detect, or compliance coverage — so progress can be demonstrated to leadership and boards.
Step 6 – Establish a Continuous Assessment Cycle
Threats evolve, infrastructure changes, and new vulnerabilities emerge constantly — making periodic reassessment essential. At minimum, dynamic environments require quarterly reviews. PCI DSS v4.0.1 requires vulnerability scans "after any significant change," and SANS Institute recommends moving from annual penetration tests toward continuous testing.
Automated tools can cut the manual effort of continuous assessment. Osto's cloud security posture management provides automated discovery and real-time posture monitoring across Azure, AWS, and GCP, keeping assessments current without requiring a large security team.

Cybersecurity Assessment in Action: A Practical Walkthrough
Consider a 60-person SaaS startup with infrastructure spread across AWS and Azure, a remote workforce, and a handful of web applications—no dedicated CISO, just a small IT team. This example shows how the six-step assessment process maps to a real situation.
During asset discovery, the team uncovers three untracked S3 buckets with public read access and an overprivileged admin account no one deprovisioned after an employee left. The risk calculation flags the public storage buckets as high-likelihood, high-impact exposure—customer PII is at risk.
Those findings jump to the top of the remediation plan ahead of low-probability theoretical risks—because they're immediately exploitable, not just hypothetically concerning.
That prioritization reflects real consequences. In late August 2025, UpGuard researchers discovered a publicly accessible Amazon S3 bucket containing over 273,000 PDF documents detailing bank transfers for Indian customers, including unredacted account numbers and email addresses. The cause: a configuration gap in an S3 bucket that no assessment had caught.
Within two weeks, the startup closes the critical gaps, implements a quarterly reassessment schedule, and builds a live risk register the CTO can reference in investor due diligence conversations. What made this work wasn't headcount or budget. It was having a structured process, the right tooling, and the discipline to act on what the assessment surfaced.
How Osto Simplifies Cybersecurity Assessments for Growing Businesses
Osto is a cybersecurity platform built for startups, scaling teams, and growing enterprises that need enterprise-grade security without the overhead of a large IT department. Its centralized dashboard and automated capabilities mean growing teams can run continuous assessments without a dedicated security hire.
What Osto Covers in an Assessment
Osto's capabilities map directly to the assessment lifecycle:
- AI-powered web scanning that categorizes vulnerabilities by severity and delivers step-by-step remediation guidance
- Cloud security posture management with automated discovery across Azure, AWS, and GCP — 35+ resource types per provider, with metadata covering configuration, networking, identity, and encryption
- WAF protection with AI-driven adaptive profiling that intelligently monitors traffic patterns and blocks attacks before they reach origin servers
- Zero Trust Network Access (ZTNA) for securing remote work environments with verified authentication workflows
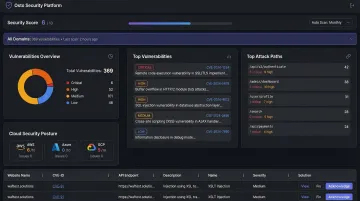
Together, these modules support both the initial assessment and the ongoing monitoring cycle — giving your team the visibility and posture analysis needed to act on findings, not just surface them.
Explore Osto or reach out at connect@osto.one to learn how it fits your specific security needs.
Frequently Asked Questions
What is a cyber security assessment?
A cybersecurity assessment is a structured evaluation of an organization's IT systems, data, and practices to identify vulnerabilities, threats, and risks. The goal is understanding current security posture and creating an actionable improvement plan.
How often should a cybersecurity assessment be performed?
Most security frameworks recommend at minimum an annual formal assessment, with quarterly reviews for dynamic environments. Many organizations add continuous automated monitoring to keep posture current between formal assessments.
What is the difference between a vulnerability assessment and a cybersecurity risk assessment?
A vulnerability assessment focuses on identifying and cataloging technical weaknesses. A cybersecurity risk assessment goes further: it analyzes the likelihood and business impact of those weaknesses being exploited, then produces a prioritized remediation plan.
How long does a cybersecurity assessment take?
Scope and organizational complexity drive timeline. A focused assessment for a small business might take days, while a comprehensive enterprise assessment can take weeks. Automated tooling can compress the discovery and monitoring phases considerably.
What are the most common findings in a cybersecurity assessment?
Common findings include cloud misconfigurations, overprivileged user accounts, unpatched software, weak or missing MFA, and exposed APIs—issues that are highly prevalent but also among the most straightforward to remediate.
Can a small business or startup benefit from a cybersecurity assessment?
Yes — and arguably more than larger ones. Growing businesses are frequent targets precisely because their defenses are often underdeveloped. A focused assessment helps small teams identify and fix the highest-impact risks first, no large security department required.