Introduction
Many IT teams struggle with a fundamental security challenge: threats don't just break in—they persist. Research shows that breaches lasting over 200 days cost $1.53 million more than those contained quickly. The problem isn't just detecting intrusions; it's detecting them before attackers establish footholds, move laterally, and exfiltrate data.
Network Security Monitoring (NSM) is the continuous collection, analysis, and interpretation of network data to detect and respond to security threats in real time.
This guide is written for IT managers, security leads, and founders at growing businesses—organizations where dwell time (how long attackers stay undetected) determines damage more than the breach entry point itself. NSM is frequently confused with basic network monitoring or intrusion detection.
Here, you'll find a clear breakdown of how NSM actually works, what separates effective programs from ineffective ones, and where it fits into a broader security strategy.
TL;DR
- NSM continuously collects and analyzes network traffic to identify threats before they cause serious damage
- Unlike performance-focused network monitoring or signature-based IDS, NSM is threat-centric and operates on continuous feedback loops
- Effectiveness depends on data coverage, sensor placement, encrypted traffic visibility, and cloud monitoring capabilities
- Pairing NSM with automated alerting and incident response protocols significantly increases its effectiveness
- Platforms like Osto provide growing businesses with centralized monitoring and real-time threat detection — reducing the need for large dedicated security teams
What Is Network Security Monitoring?
NSM is built on a critical principle: prevention eventually fails. Organizations must assume breaches will occur and maintain continuous visibility to limit damage when they do.
NSM achieves this by collecting and correlating data from packets, flows, logs, and traffic patterns—then surfacing anomalies for analyst review or automated response. The goal is detecting unauthorized or malicious activity across networks before attackers can establish persistence or move laterally.
How NSM Differs From Similar Concepts
| Network Monitoring | IDS | NSM | |
|---|---|---|---|
| Core question | Is the network functioning? | Does this traffic match a known attack? | Is someone attacking the network? |
| Approach | Performance metrics (uptime, latency, bandwidth) | Signature-based, reactive | Behavioral and threat-centric |
| What it misses | Security threats entirely | Zero-days, insider threats, novel patterns | — |
| Improvement over time | Static thresholds | Requires signature updates | Continuously refines behavioral baselines |
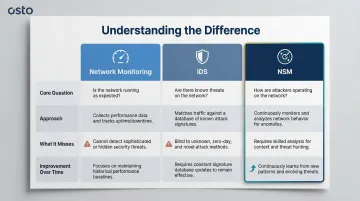
Unlike IDS tools that evaluate each incident in isolation, NSM operates cyclically—each detection feeds back into the behavioral model, improving future accuracy over time.
Why NSM Is Used in Modern Cybersecurity
The core problem NSM addresses is attacker persistence. Global median dwell time dropped to 10 days in 2023, down from 16 days in 2022—but that's still 10 days for attackers to escalate privileges, move laterally, and establish backdoors. Detection speed—not just prevention—determines how much a breach ultimately costs. Organizations need visibility across distributed environments: on-premises infrastructure, remote endpoints, and cloud workloads. Traditional perimeter-based security creates dangerous blind spots across all three.
What Goes Wrong Without NSM
Without continuous monitoring:
- Lateral movement goes undetected as attackers pivot between internal systems
- Encrypted traffic hides malicious payloads (87% of threats now hide in encrypted channels)
- Security teams react to confirmed breaches rather than investigating early-stage indicators of compromise
- Organizations discover breaches months after initial intrusion, when damage is already severe
That operational exposure also creates compliance risk. NSM isn't just operationally preferred—it's increasingly mandated. Major compliance frameworks explicitly require continuous network monitoring:
NSM as Regulatory Requirement
| Framework | Control ID | Requirement |
|---|---|---|
| NIST CSF 2.0 | DE.CM-01 | Networks and network services are monitored to find potentially adverse events |
| ISO 27001:2022 | Annex A 8.16 | Networks, systems, and applications must be monitored for anomalous behavior |
| SOC 2 | CC7.2 | System components must be monitored for anomalies symptomatic of malicious acts |
For growing businesses and scaling enterprises, meeting these controls often starts with deploying an NSM capability—and the monitoring logs it generates become direct audit evidence when assessors come knocking.
How Network Security Monitoring Works
NSM operates through a continuous cycle: data collection, normalization and analysis, detection and response, and baseline refinement. It's not a one-way alert system—each detection feeds back into the model, improving future accuracy over time.

Step 1: Data Collection and Sensor Placement
NSM sensors are strategically placed at network ingress/egress points, between internal segments, and within cloud environments to capture:
- North-south traffic: External communications entering or leaving the network
- East-west traffic: Internal lateral movement between systems and segments
⚠️ Missing sensor coverage is one of the most common deployment failures. Gaps in cloud traffic monitoring, unmanaged devices, and remote endpoints create blind spots that attackers exploit.
Data inputs include:
- Full packet captures (PCAP) for forensic analysis
- NetFlow/IPFIX data showing connection metadata
- Firewall and endpoint logs
- DNS query records
- Application-level traffic metadata
Step 2: Normalization, Baselining, and Analysis
Raw collected data is normalized into consistent formats. NSM systems then establish behavioral baselines of "normal" network activity—typical data transfer volumes, common protocol usage, expected connection patterns.
Analytical models (increasingly AI/ML-driven) evaluate current traffic against these baselines to surface anomalies:
- Unusual data transfer volumes suggesting exfiltration
- Unexpected protocol usage indicating tunneling or covert channels
- Connections to known malicious IP addresses
- Abnormal authentication patterns suggesting credential compromise
Machine learning-based detection reduces false positives to under 5%, compared to 12-15% for traditional signature-based systems like Snort. That accuracy gap directly affects how quickly teams can move from alert to response.
Step 3: Detection, Alerting, and Response
Detected anomalies trigger prioritized alerts that security analysts investigate. Mature NSM deployments integrate with SIEM, SOAR, or endpoint tools to enable coordinated response.
For growing businesses without dedicated security teams, Osto's centralized monitoring dashboard covers this response loop directly—combining real-time threat detection, automated alerting, and unified visibility across web, network, and cloud layers in a single platform.
Key Factors That Affect NSM Effectiveness
Coverage and Blind Spots
NSM is only as effective as the visibility it has. Common weak points include:
- Encrypted traffic: Only 3.5% of organizations decrypt and inspect TLS/SSL traffic, largely because decryption reduces firewall performance by up to 92%
- Cloud environments: Public cloud traffic, internal wireless, and multi-cloud deployments frequently lack monitoring
- Remote endpoints: Distributed workforces create visibility gaps when endpoints operate outside traditional network perimeters
- Unmanaged devices: IoT devices, contractor systems, and shadow IT often escape monitoring

Data Volume vs. Strategic Collection
Organizations often generate more network data than they can meaningfully analyze. Effective NSM requires strategic sensor deployment and behavioral modeling rather than indiscriminate data collection.
73% of SOCs cite false positives as their top detection challenge, with 59% of teams reporting "too many alerts". Alert fatigue causes 42% of alerts to go entirely uninvestigated.
The fix is prioritizing high-fidelity anomaly detection over volume-based alerting — focusing on behavioral deviations rather than flagging every potential indicator.
Team Collaboration
That alert overload problem is often compounded by organizational friction. NSM depends on SecOps and NetOps working in alignment — network teams control visibility infrastructure (sensor placement, traffic mirroring, cloud logging), while security teams define what to look for (threat models, detection rules, response protocols).
Siloed operations undermine detection quality—network changes that break sensor coverage or security policies that conflict with network architecture create gaps attackers exploit.
Common Issues and Misconceptions About NSM
Misconception: NSM Equals IDS
Many teams treat their intrusion detection system as their NSM capability. IDS is signature-dependent and reactive—it won't catch zero-day exploits, insider threats, or novel attack patterns that NSM's behavioral analysis is designed to surface.
The distinction matters: IDS alerts on known threats; NSM detects anomalous behavior that may indicate unknown threats.
Oversimplification: Full Visibility Once Sensors Deploy
Teams assume full-network visibility once sensors are deployed, but encrypted traffic (TLS/SSL) is often not decrypted or analyzed. With 87% of threats delivered over encrypted channels, this leaves a significant portion of network activity effectively invisible.
Organizations must implement dedicated TLS decryption architectures or deep observability pipelines to inspect traffic without degrading network performance.
Confusion: Process vs. Outcome
Closing the visibility gap on your infrastructure is only half the equation. NSM generates alerts, not automatic security. A common operational failure is deploying NSM tools without defined incident response protocols—leaving teams that can detect threats but can't act on them before damage occurs.
Without those protocols in place:
- Alerts pile up without triage or prioritization
- Response timelines stretch, giving attackers room to move
- Detection data goes unused because no one owns the follow-through
When NSM May Not Be Enough
NSM alone does not stop threats—it detects them. Without integration into a broader security stack (endpoint protection, access control, identity verification, incident response processes), NSM visibility cannot translate into effective remediation.
NSM effectiveness degrades in environments with:
- Poor network segmentation allowing unrestricted lateral movement
- Heavy reliance on encrypted traffic without decryption capabilities
- Multi-cloud deployments without unified visibility
- Inadequate logging or retention policies limiting forensic investigation
For organizations lacking dedicated security operations resources:
NSM tools can generate alert volumes that overwhelm small teams. 84% of SMB owners manage cybersecurity internally amidst severe staffing shortages, with ISC2 reporting a global workforce gap of 4.76 million professionals.
For teams without a dedicated SOC, a unified platform reduces the complexity of managing disparate tools. Osto's security platform brings together real-time threat detection, Web Application Firewall (WAF), and Zero Trust Network Access (ZTNA) in a single dashboard, giving growing businesses comprehensive coverage without requiring a large security team.

Cross-environment complexity:
Breaches spanning multiple environments take 276 days to resolve and cost $5.05 million on average. Organizations must activate cloud-native telemetry (AWS VPC Flow Logs, Azure Network Watcher, GCP VPC Flow Logs) and integrate them into centralized NSM workflows to eliminate blind spots.
Frequently Asked Questions
What is network security monitoring?
NSM is the continuous process of collecting and analyzing network data—including traffic flows, logs, and packet captures—to detect and respond to unauthorized activity or security threats in real time. It operates on the assumption that some threats will bypass preventive controls, making detection and response equally critical.
What are the five types of network security?
The main categories are firewall security, intrusion detection/prevention, access control, VPN/network segmentation, and monitoring/analytics. NSM spans several of these by providing the visibility layer that makes other controls more effective.
What is the difference between NSM and IDS?
IDS uses predefined signatures to detect known attack patterns, while NSM takes a broader, behavioral approach—establishing traffic baselines and detecting anomalies that signature-based tools miss, including zero-day threats and insider activity.
What data does network security monitoring collect?
NSM collects full packet captures, NetFlow/traffic flow data, DNS query logs, application metadata, and firewall/endpoint logs. Together, these sources give security teams the context needed to detect deviations from normal network behavior.
How does NSM work in cloud environments?
Cloud NSM requires deploying virtual sensors or using cloud-native flow logging (VPC flow logs, NSG flow logs). Visibility challenges are higher due to encrypted east-west traffic and dynamic resource scaling—which is why consolidating Azure, AWS, and GCP data into a single monitoring view matters for consistent coverage.
What are the biggest challenges of network security monitoring?
Top challenges include encrypted traffic limiting visibility, alert fatigue from high data volumes, gaps in cloud and remote endpoint coverage, and baseline drift as networks change and scale over time.