Introduction
Every device connected to a business network—laptops, phones, servers, remote workstations—represents a potential entry point for attackers. In 2025, 82% of modern cyber detections are entirely "malware-free," relying instead on stolen credentials and legitimate system tools to bypass traditional security. The average cost of a data breach has reached $4.44 million globally, with U.S. organizations averaging an all-time high of $10.22 million.
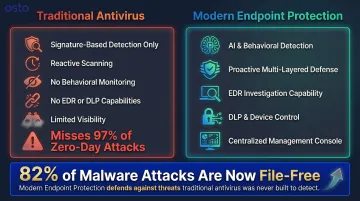
Most businesses know they need "antivirus," but few understand the difference between traditional antivirus and modern endpoint virus protection. That gap leads directly to underprotection. Traditional signature-based antivirus is blind to over four-fifths of current attacks. This guide explains what endpoint virus protection is, how it works, and why the distinction matters for keeping your business secure against today's threats.
TL;DR
- Endpoint virus protection secures individual devices from malware, ransomware, and other threats—going far beyond traditional antivirus
- Works through continuous monitoring, multi-method detection, automated response, and centralized management
- Modern solutions use AI, behavioral analysis, and signature matching—not just virus definition databases
- The right solution depends on your business size, remote work needs, and IT resources available
What Is Endpoint Virus Protection?
Endpoint virus protection is a security solution installed on or applied to endpoint devices—laptops, desktops, mobile phones, servers, IoT devices—that detects, prevents, and responds to malicious software and cyberattacks. An "endpoint" refers to any device that connects to a network and can serve as an attack entry point.
Endpoint virus protection is not simply antivirus software. While antivirus is one layer within it, endpoint protection is a broader, multi-layered platform that includes:
- Threat monitoring across all connected devices
- Behavioral analysis to catch unknown threats
- Response capabilities like quarantine and device isolation
- Centralized management through a unified console
According to Gartner, an Endpoint Protection Platform (EPP) is "security software designed to protect managed endpoints against known and unknown malicious attacks" using a combination of security techniques and attack surface reduction capabilities.
Not all endpoint protection solutions are built the same. Deployment model and management approach vary considerably across three categories:
- Legacy: Traditional on-premises systems requiring physical servers and manual updates
- Hybrid: Older platforms retrofitted with cloud features as a transitional step
- Cloud-native: Built from the ground up for distributed environments and remote workforces
Capabilities and management complexity differ significantly across each — cloud-native solutions offer the simplest deployment and the strongest support for remote workers.
How Does Endpoint Virus Protection Work?
When a threat appears on an endpoint, modern protection doesn't wait for a human to notice. Detection, response, and recovery happen in a continuous automated loop — monitored from a single management console. Understanding each layer explains why today's tools catch what legacy antivirus misses.
Detection: How Threats Are Identified
Modern endpoint protection uses three complementary detection methods:
Signature-Based Detection
The software compares files and processes against a database of known malware signatures. This method is effective against established threats but limited against new or modified variants. With over 450,000 new malicious programs registered daily, signature databases alone can't keep pace with threat evolution.
That limitation is exactly why behavioral analysis exists.
Behavioral Analysis
Instead of matching known signatures, the system monitors how programs behave — flagging unusual actions like:
- Unauthorized file encryption
- Unexpected network connections
- Attempts to access system memory
- Mass file modifications
- Credential dumping or process injection
This catches new and unknown threats that have no signature yet. Microsoft Defender for Endpoint, for example, uses behavioral blocking to identify and stop threats based on their behaviors and process trees, even when the threat has started execution.
AI and Machine Learning Detection
Algorithms analyze patterns across large volumes of endpoint activity data to identify anomalies that suggest malicious intent. This includes fileless attacks and zero-day exploits that bypass both signature and simple behavioral checks. In 2025, zero-day exploits increased 42% year-over-year as attackers used them to break into systems.
| Threat Type | Legacy AV Effectiveness | Modern EDR Effectiveness | Detection Mechanism |
|---|---|---|---|
| Known Malware | High | High | Signature matching, file hashing |
| Zero-Day Exploits | Low (97% bypass rate) | High | Behavioral AI, anomaly detection |
| Fileless / In-Memory | Low (No file dropped to disk) | High | Memory scanning, script monitoring |
| Living-off-the-Land (LOTL) | Low (Uses legitimate tools) | High | Continuous behavioral monitoring |
Response: What Happens When a Threat Is Found
Automated Response Actions
Once a threat is confirmed, the system can:
- Quarantine infected files to prevent execution
- Block malicious processes or URLs immediately
- Isolate a compromised device from the network to stop lateral spread
All of this happens without waiting for human intervention. The average "breakout time" (time it takes an attacker to move laterally after initial compromise) has plummeted to just 29 minutes, with the fastest recorded at 27 seconds. Automated response is essential for surviving this speed.
Organizations extensively utilizing security AI and automation reduced their breach lifecycles by 80 days and saved an average of $1.9 million per incident compared to those without it.
Rollback and Remediation
Advanced endpoint protection can reverse changes made by malware — such as encrypted or modified files — restoring the endpoint to a clean state. This drastically reduces recovery time, though it cannot undo data theft or exfiltration. Rollback relies on protected backup snapshots, which advanced ransomware actively attempts to delete.
Centralized Management and Continuous Monitoring
A management console — typically cloud-based in modern solutions — gives administrators a unified view of:
- All endpoints and their security status
- Active threats and policy compliance
- Real-time event data from every device
This is what separates endpoint protection platforms from standalone antivirus tools. Continuous monitoring enables both automated responses and deeper investigation by security teams when needed.
Key Components of Endpoint Virus Protection
Next-Generation Antivirus (NGAV)
Traditional antivirus matched files against known threat signatures — and stopped there. NGAV replaces that model with AI, machine learning, and behavioral detection, so it can identify threats that have never been seen before. It's the core detection engine in most modern endpoint protection platforms.
Endpoint Detection and Response (EDR)
NGAV stops threats at the door — EDR handles what gets through. It records endpoint activity continuously, giving security teams the ability to:
- Investigate exactly how an attack unfolded
- Hunt for threats that bypassed initial defenses
- Respond with precision rather than guessing
Basic antivirus has none of this capability. The EDR market is projected to grow from $5.11 billion in 2025 to $18.68 billion by 2031, reflecting its shift from optional add-on to default security layer.
Data Loss Prevention (DLP)
DLP monitors and blocks unauthorized data transfers — through USB drives, email, cloud uploads, or web apps. It protects intellectual property and supports compliance requirements beyond just stopping malware. The annual cost of insider risks has reached $17.4 million, with data exfiltration most often happening through these same endpoint channels.
Device Control and Application Management
This component controls which external devices — such as USB drives — can connect to a machine and which applications are allowed to run. By restricting what can plug in or execute, it shrinks the attack surface before a threat ever launches.
Firewall and Intrusion Prevention at the Endpoint Level
Rather than relying solely on a perimeter firewall, endpoint-level firewalls give each device its own network traffic filter. This matters most for remote workers operating outside the corporate network — where breaches cost nearly $1 million more on average than those that don't involve remote access.
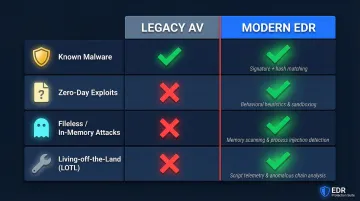
Traditional Antivirus vs. Modern Endpoint Protection
Traditional antivirus is reactive by design. It scans files for known malware patterns and handles common, well-documented threats reasonably well — but it cannot detect polymorphic malware, fileless attacks, or zero-day exploits with no existing signature. Research shows that 97% of zero-day attacks bypass traditional signature-based antivirus entirely.
Modern endpoint protection takes a different approach: proactive and multi-layered. It combines NGAV, behavioral monitoring, EDR, DLP, and centralized management into a single platform. A threat doesn't need to match a known signature to be caught, and security teams gain the visibility and response capability that antivirus alone can't provide.
When Is Each Appropriate?
- Antivirus alone may work for individual personal devices with low risk exposure
- Full endpoint protection is necessary for any business managing multiple devices
- Remote workforces, sensitive customer data, or compliance requirements all push the need toward endpoint protection
- Organizations using cloud infrastructure or SaaS tools face threat surfaces antivirus wasn't built to cover
The shift from file-based malware to identity-driven attacks and Living-off-the-Land techniques — where attackers abuse legitimate tools already on your system — has made signature-based detection no longer reliable enough for business environments.
What to Look for in an Endpoint Protection Solution
Scalability and Ease of Management
For growing businesses without large IT teams, the solution should offer a centralized dashboard that doesn't require deep technical expertise to operate. Cloud-native platforms are better suited here than legacy on-premises solutions. According to the 2024 IBM report, 53% of organizations face a high-level skills shortage, which corresponded to an average $1.76 million more in breach costs.
Platforms like Osto, built specifically for scaling businesses, offer an advantage by combining real-time threat detection with a streamlined management interface that doesn't require a large security team. The Guardz 2025 SMB Cybersecurity Report found that 52% of SMBs rely on untrained internal staff or business owners to manage security functions, and only 41% have endpoint protection deployed.
Detection Capability and AI Integration
Prioritize solutions that go beyond signatures—look for:
- Behavioral analysis that monitors process execution
- AI/ML-driven anomaly detection
- EDR capabilities for investigation and threat hunting
Ask vendors whether their solution handles fileless attacks and zero-day threats, not just known malware.
Deployment Model and Remote Workforce Support
Once you've confirmed a solution's detection depth, consider where it actually needs to operate. The solution must protect devices regardless of whether they're on the corporate network — cloud-native endpoint protection and Zero Trust Network Access (ZTNA) are both worth evaluating carefully here.
NIST SP 800-207 (Zero Trust Architecture) mandates that "The enterprise monitors and measures the integrity and security posture of all owned and associated assets," with access decisions evaluating the security posture of the asset. A 2024 Gartner survey revealed that 63% of organizations worldwide have fully or partially implemented a zero-trust strategy — and for good reason: 46% of compromised devices with corporate logins were unmanaged or BYOD systems, underscoring why coverage can't stop at managed endpoints.

Frequently Asked Questions
What is meant by endpoint protection?
Endpoint protection refers to securing individual devices—laptops, phones, servers—that connect to a network, using a combination of threat detection, behavioral monitoring, and automated response to prevent malware and unauthorized access. It protects each device as an independent security perimeter.
What are the three main types of endpoint security?
The three main types are legacy (on-premises, locally managed systems requiring physical infrastructure), hybrid (cloud-adapted legacy systems with some cloud features), and cloud-native (built specifically for modern distributed environments with remote management and automatic updates).
What is EPP vs EDR vs XDR?
EPP (Endpoint Protection Platform) focuses on prevention through antivirus, firewall, and attack surface reduction. EDR (Endpoint Detection and Response) adds continuous monitoring, forensic investigation, and active response capabilities. XDR goes further, unifying detection and response across endpoints, networks, and cloud environments into a single system.
Is EDR better than antivirus?
EDR is more capable than antivirus for modern threats because it monitors behavior in real time, enables forensic investigation, and supports active threat hunting—while antivirus only detects known malware signatures. For businesses, EDR is the stronger choice given that 82% of modern attacks are malware-free.
What is an endpoint security agent?
An endpoint security agent is a lightweight software component installed on each device that continuously monitors activity, enforces security policies, and communicates with the central management console to report threats and receive updates.
Why is endpoint protection on my PC?
Endpoint protection is installed to guard against viruses, ransomware, spyware, and other malware that can compromise data or system integrity. It runs in the background continuously and is a baseline security requirement for any device connected to a business or personal network.