Introduction
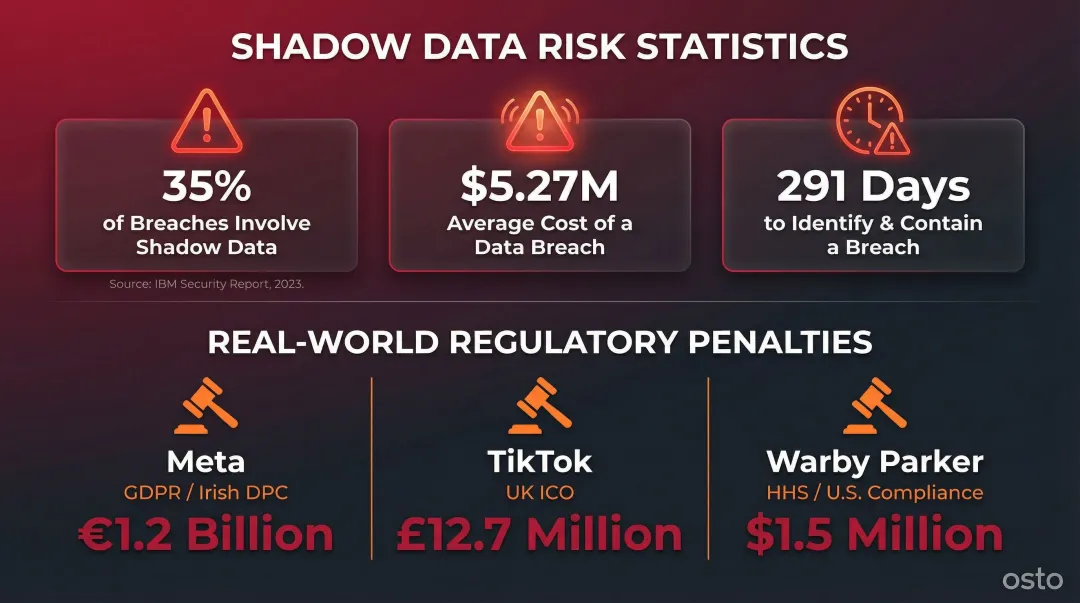
Sensitive data now sprawls across cloud services, developer environments, and SaaS platforms—much of it untracked and unprotected. The problem has a name: shadow data. 35% of data breaches involve shadow data, the unmanaged information sitting in forgotten storage buckets, test environments, and copied datasets. Those breaches cost an average of $5.27 million—16.2% higher than breaches without shadow data—and take 291 days to identify and contain.
Traditional perimeter-based security tools cannot keep pace. NIST acknowledges the "disappearance of the concept of a perimeter" in modern enterprise networks, rendering legacy defenses obsolete. Fast-growing and multi-cloud organizations need a new approach that protects data directly, not just the infrastructure surrounding it.
DSPM (Data Security Posture Management) addresses this gap with a data-first security discipline. It provides continuous visibility, risk assessment, and policy enforcement centered on the data itself, regardless of where it resides. What follows breaks down how DSPM works, what it covers, and the best practices that make it effective in fast-changing cloud environments.
TLDR:
- DSPM discovers and classifies sensitive data across cloud, SaaS, and on-premises environments
- Shadow data drives 35% of breaches at $5.27M average cost; DSPM surfaces these hidden assets
- Continuous monitoring prevents posture drift in fast-changing cloud environments
- DSPM complements CSPM (infrastructure) and DLP (data in motion) for layered defense
- Start with risk assessment, choose agentless discovery, and integrate with existing security tools
What Is Data Security Posture Management (DSPM)?
DSPM is a security discipline and set of technologies that help organizations discover, classify, monitor, and protect sensitive data—regardless of where it resides. Whether data lives in public clouds, private clouds, hybrid environments, or on-premises systems, DSPM provides unified visibility and control. Unlike traditional infrastructure-focused tools, DSPM is data-first, meaning it prioritizes protecting the data directly rather than just the systems around it.
Gartner first named DSPM in its 2022 Hype Cycle for Data Security, defining it as technology that "provides visibility as to where sensitive data is, who has access to that data, how it has been used, and what the security posture of the data stored, or application is." Initially categorized in the "Innovation Trigger" phase, DSPM moved from emerging concept to standard practice within just a few years.
By 2026, Gartner projects that more than 20% of organizations will deploy DSPM technology to identify previously unknown data repositories and mitigate data exposure and compliance risks. The driving forces are hard to ignore: shadow data, multi-cloud complexity, and mounting regulatory pressure have outpaced what traditional security tools can handle.
At its most practical level, DSPM gives security teams answers to four questions they've historically struggled to answer:
- Where sensitive data lives across all environments
- Who can access that data and what permissions they hold
- How data moves between systems, users, and third parties
- Whether data is adequately protected with encryption and access controls
How DSPM Works: The Core Process
Step 1 — Data Discovery
DSPM continuously scans across all environments—cloud storage, databases, SaaS applications, and on-premises file systems—to locate and catalog data assets. This includes both known repositories and shadow data: information copied, backed up, or moved outside official IT oversight without proper security controls.
The discovery process is typically agentless and automated, requiring no manual connector configuration for each asset — which means data stores security teams never knew existed finally come into view.
Step 2 — Data Classification
Once data is located, DSPM classifies it by sensitivity using intelligent techniques beyond simple pattern matching. Classification categories include:
- PII (Personally Identifiable Information): Names, addresses, Social Security numbers
- PHI (Protected Health Information): Medical records, health insurance data
- Financial data: Payment card numbers, bank account details, transaction records
- Intellectual property: Source code, trade secrets, proprietary algorithms
DSPM maps classified data to regulatory requirements such as GDPR, HIPAA, and PCI DSS, determining how much protection each dataset requires.
Step 3 — Data Flow Mapping and Risk Assessment
Knowing where data lives is only half the picture. Tracing how it moves between systems, databases, and users creates a data flow map that reveals:
- Potential attack paths where data could be exposed
- Misconfigured access controls allowing unauthorized access
- Over-permissioned users with broader access than their role requires
- Unencrypted data in transit or at rest
This risk assessment identifies which data assets face the greatest exposure and require immediate remediation.
Step 4 — Policy Enforcement
With risk ranked and mapped, DSPM enforces security policies such as:
- Encryption requirements for data at rest and in transit
- Access restrictions based on the principle of least privilege
- Data residency rules to comply with regional regulations
- Retention policies to minimize data sprawl
DSPM solutions automate this enforcement rather than relying on manual remediation, reducing the burden on security teams.
Step 5 — Continuous Monitoring and Incident Response
Unlike a point-in-time audit, DSPM runs continuously, monitoring for:
- Posture drift—configuration changes that weaken security
- New data assets created by developers or analytics teams
- Anomalous access patterns indicating potential breaches
- Emerging threats targeting sensitive data
When issues arise, DSPM alerts security teams and, in some tools, triggers automated remediation or guided incident response playbooks.

Why Organizations Need DSPM
The Shadow Data Problem
Cloud transformation and the spread of self-serve data access have created a sprawling, hard-to-track attack surface. Developers spin up new data stores, AI teams copy datasets for training, and analytics teams duplicate production data—all faster than security teams can track. According to the IBM Cost of a Data Breach Report 2024, 35% of breaches involved shadow data, with these incidents costing $5.27 million on average and taking 291 days to resolve.
Misconfigurations or forgotten data stores become easy targets. A 2023 Cloud Security Alliance report found that 93% of security professionals are concerned about shadow data, which can "proliferate in just a few clicks" from test environments, misplaced storage buckets, or legacy data left behind after cloud migrations.
Multi-Cloud Complexity
Most growing organizations operate across AWS, Azure, GCP, and multiple SaaS platforms—each with its own configurations, permission models, and compliance controls. Without a unified DSPM layer, data security becomes inconsistent, creating blind spots that attackers exploit.
The IBM 2024 report reveals that 40% of breaches involved data distributed across multiple environments (public clouds, private clouds, and on-premises). These breaches took the longest to identify and contain, averaging 283 days.
For scaling businesses without large, dedicated security teams, managing separate tools for each cloud provider isn't just inefficient—it's a gap attackers actively look for.
Compliance Pressure and Financial Risk
The global average cost of a data breach reached $4.88 million in 2024—a 10% increase from 2023—and regulators under GDPR, HIPAA, and CCPA are adding their own penalties on top. Recent enforcement actions show how steep that exposure gets:
- European Data Protection Board fined Meta 1.2 billion euros for systematic data transfer violations
- UK ICO fined TikTok £12.7 million for failing to protect children's data
- US HHS fined Warby Parker $1.5 million for inadequate ePHI security measures
Each of these cases involved data that organizations didn't fully know they had—or didn't know was exposed. DSPM addresses that root cause directly, giving security teams the visibility needed to find and fix risks before regulators or attackers do.
Key DSPM Capabilities
Comprehensive Data Discovery and Shadow Data Detection
Agentless, cloud-native scanning is central to how DSPM works — no manual connector configuration required for each asset. This approach uncovers shadow data: stores that IT and security teams don't know exist. By continuously discovering new assets, DSPM ensures security coverage expands as fast as the business creates new data.
Sensitive Data Classification
Classification goes beyond simple regex matching, using multi-step techniques to identify PII, PHI, financial records, and proprietary information. Accurate classification enables proportional protection — the most sensitive assets get the strictest controls, while low-risk data isn't over-secured at the expense of budget and speed.
Access Governance and Least-Privilege Enforcement
DSPM provides visibility into who has access to what data and flags over-permissioned users, orphaned accounts, and excessive access rights. The 2025 Verizon DBIR found that Privilege Misuse accounted for 825 incidents, with 90% driven by internal actors using company-granted access to steal data. DSPM supports consistent enforcement of the principle of least privilege across all environments, reducing this insider threat vector.
Misconfiguration and Vulnerability Detection
The Verizon 2024 DBIR found misconfiguration present in approximately 10% of breaches — and those failures are rarely exotic. Common culprits include:
- Unsecured cloud storage buckets left publicly accessible
- Missing encryption on data at rest or in transit
- Unapplied patches on cloud-hosted workloads
- Exposed APIs without proper authentication controls
DSPM provides risk-scored alerts with guided remediation steps, so teams resolve the highest-priority issues first rather than drowning in unprioritized noise.
Compliance Reporting and Audit Support
Automated mapping against regulatory frameworks — GDPR, HIPAA, PCI DSS, NIST — means DSPM generates audit-ready reports without manual evidence collection. For teams building toward compliance, that's significant time reclaimed from documentation work.
For organizations running multi-cloud infrastructure, a platform that consolidates these capabilities matters. Osto's Cloud Security Posture Management covers Azure, AWS, and GCP in a single inventory — automatically discovering 35+ resource types per provider, with enriched metadata across configuration, networking, identity, and encryption. Security checks for misconfigurations run without requiring separate tools for each environment or a large IT team to manage them.
DSPM Best Practices
Best Practice 1: Discover and Classify All Data First
You cannot protect what you cannot see. The first step is establishing full visibility across all environments—structured databases, unstructured files, and shadow data—before layering on controls.
Autonomous, continuous discovery is essential here. Elite DevOps teams deploy code multiple times per day, creating new data stores with every release. Manual discovery falls behind instantly in that environment.
Action steps:
- Deploy DSPM with agentless discovery that automatically scans all cloud environments
- Prioritize tools that detect shadow data without requiring pre-configured connectors
- Schedule continuous discovery, not periodic audits
Once you can see all your data, the next question is: who can reach it?
Best Practice 2: Enforce Least-Privilege Access Consistently
Controlling who can access sensitive data is one of the most impactful risk reduction measures. DSPM surfaces over-permissions and stale access rights, addressing both insider threats and accidental exposure risks.
NIST SP 800-207 mandates that "least privilege principles are applied to restrict both visibility and accessibility." Over-permissioned users are a leading attack vector — industry data consistently shows internal actors drive the majority of privilege misuse incidents.
Action steps:
- Use DSPM to audit access controls regularly and revoke permissions that are no longer needed
- Implement role-based access control (RBAC) aligned with job functions
- Automate access reviews rather than relying on manual quarterly audits
Best Practice 3: Implement Continuous Risk Monitoring — Not Periodic Audits
Static, point-in-time assessments leave organizations blind between scans. In agile cloud environments, developers alter settings via management consoles or APIs constantly — meaning posture drift isn't occasional, it's the default state. NIST SP 800-128 warns that without continuous monitoring, organizations remain blind to undiscovered components, misconfigurations, and unauthorized changes.
To address this:
- Deploy DSPM that monitors environments in real-time, not on weekly or monthly schedules
- Set up alerts for configuration changes that weaken security posture
- Track posture drift trends to identify high-risk teams or environments
Best Practice 4: Prioritize Risk Remediation Based on Data Sensitivity
Not all risks are equal. Use DSPM's risk-scoring capabilities to prioritize remediation—focusing first on exposed sensitive data (e.g., unprotected PII or publicly accessible storage with financial records), then working down to lower-severity findings.
Alert fatigue is real — unprioritized tools bury critical findings in noise. With limited team bandwidth, focusing on the highest-impact fixes first isn't optional; it's the only approach that holds up under pressure.
Action steps:
- Configure DSPM to score risks based on data classification (PII, PHI, financial) and exposure level
- Address critical and high-severity findings within 24-48 hours
- Automate remediation for common misconfigurations (e.g., publicly accessible S3 buckets)
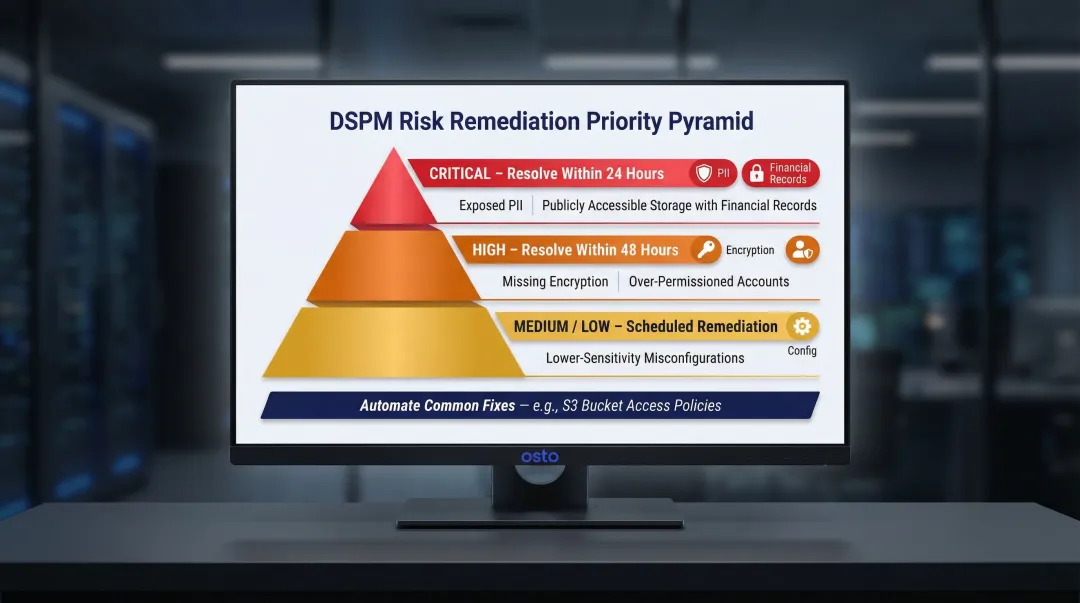
Knowing what to fix first is only half the equation — your policies also need to reflect the specific rules your organization must follow.
Best Practice 5: Align DSPM Policies with Regulatory and Business Requirements
Security policies in DSPM should reflect both external compliance requirements (GDPR, HIPAA, CCPA, PCI DSS) and internal data governance standards. Custom policies matter because every organization handles different data types.
Generic policies don't account for industry-specific risks or regulatory requirements. Automated policy enforcement reduces manual effort and eliminates the human error that manual compliance reviews inevitably introduce.
Action steps:
- Map DSPM policies to specific regulatory frameworks your organization must comply with
- Integrate DSPM findings with SIEM for centralized threat detection
- Connect DSPM classification data to DLP tools to enforce data movement policies
- Use DSPM access insights to inform IAM policy adjustments
DSPM vs. Related Technologies
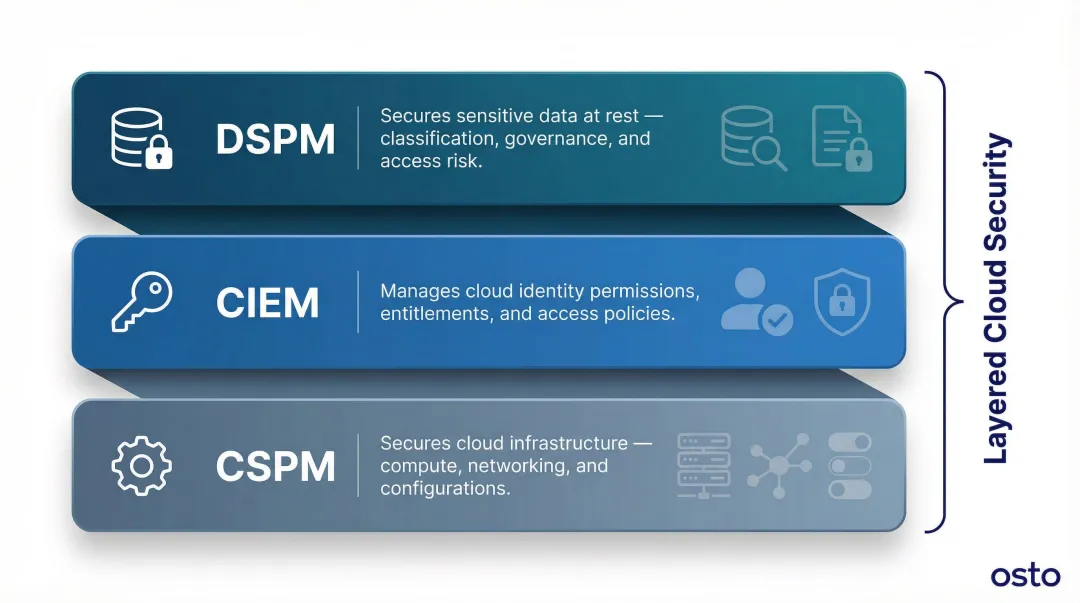
DSPM vs. CSPM
CSPM (Cloud Security Posture Management) secures the cloud infrastructure—compute, networking, configurations. DSPM secures the sensitive data within that infrastructure. CSPM locks the building; DSPM secures the filing cabinets inside.
Key distinctions:
- CSPM focuses on vulnerabilities at the cloud infrastructure level (virtual machines, containers, network configurations)
- DSPM focuses on vulnerabilities at the data level (who can access sensitive data, where it's stored, whether it's encrypted)
- These are complementary, not competing—organizations benefit most from both working in tandem
For example, Osto's Cloud Security Posture Management discovers 35+ resource types across Azure, AWS, and GCP, identifying infrastructure misconfigurations. A DSPM layer would then classify which of those resources contain sensitive data and assess data-specific risks like over-permissioned access or unencrypted storage.
DSPM vs. DLP
DLP (Data Loss Prevention) focuses on preventing data from leaving the organization by monitoring data in motion—blocking uploads, emails, or transfers of sensitive content. DSPM is broader and more foundational: it discovers and classifies all data at rest, maps access risk, and monitors posture continuously.
Key distinctions:
- DLP monitors and blocks data in motion (preventing unauthorized transfers)
- DSPM discovers, classifies, and continuously assesses all data at rest across environments
- Integrating DSPM with DLP creates a more complete data protection strategy—DSPM informs and strengthens what DLP monitors and enforces
That gap in visibility matters most when managing cloud-scale environments—which is where identity and access risk becomes the next layer to address.
DSPM + CIEM: How They Work Together
CIEM (Cloud Infrastructure Entitlement Management) focuses specifically on managing permissions and entitlements within cloud infrastructure. It addresses the "who can access what" question at the identity layer.
How they work together:
- CIEM guards initial access to the architecture, ensuring unauthorized entities cannot reach sensitive resources
- DSPM secures the data itself, ensuring that even authorized users only access what they need
- CSPM secures the underlying infrastructure
- Together, DSPM, CSPM, and CIEM form a layered approach—each addressing a different dimension of cloud security risk
Frequently Asked Questions
Frequently Asked Questions
Is data security posture management (DSPM) worth it?
For organizations handling sensitive data across cloud environments, DSPM reduces breach risk, streamlines compliance, and replaces error-prone manual audits with continuous automated monitoring. With shadow data breaches averaging $5.27 million, DSPM is a high-ROI investment for any data-heavy organization.
What is the difference between DSPM and DLP?
DLP monitors and blocks data in motion, preventing unauthorized transfers via email, uploads, or file sharing. DSPM focuses on discovering, classifying, and continuously assessing all data at rest across environments. The two are complementary: DSPM surfaces the data landscape and risk profile, while DLP enforces movement controls based on that intelligence.
What is the difference between DSPM and CSPM?
CSPM secures cloud infrastructure by finding misconfigurations and vulnerabilities in the cloud environment itself (compute, networking, storage configurations). DSPM focuses on the sensitive data stored within that infrastructure—who can access it, where it's located, and whether it's protected. Both are needed for comprehensive cloud security.
Can DSPM detect shadow data?
Yes. DSPM's agentless, continuous discovery automatically identifies shadow data—unmanaged stores from developers, analytics teams, or migrations—that traditional security tools miss entirely, without requiring manual configuration.
What types of data does DSPM protect?
DSPM protects structured data (databases, PII records, financial data), unstructured data (documents, emails, source code), and cloud object storage across all major cloud providers (AWS, Azure, GCP) and SaaS applications. It classifies and monitors sensitive information regardless of format or location.
How do I get started with DSPM?
Start with a risk assessment to map your data landscape and compliance obligations. Choose a solution with agentless discovery across your cloud environments—Osto, for example, provides unified visibility across Azure, AWS, and GCP with automated asset discovery and built-in security checks. From day one, prioritize integration with your existing IAM, SIEM, and DLP tools.