This guide covers what cybersecurity compliance means, the major standards and frameworks, which industries face the strictest regulations, and the practical steps growing businesses can take to achieve and maintain compliance without needing a large IT department.
TLDR
- Cybersecurity compliance means adhering to laws and frameworks that protect data and digital systems from unauthorized access and breaches
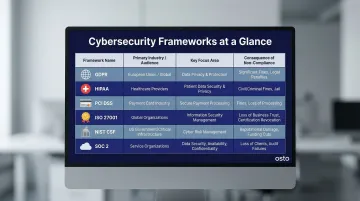
- Key frameworks include GDPR, HIPAA, PCI DSS, ISO 27001, NIST CSF, and SOC 2—each targeting different industries and data types
- Non-compliance carries steep costs: GDPR fines alone can reach 4% of global revenue, plus legal exposure and reputational damage
- Building a sustainable compliance program follows five steps: assess, plan, implement, document, and monitor
- Unified security platforms help growing businesses streamline compliance through centralized monitoring and real-time visibility
What Is Cybersecurity Compliance?
Cybersecurity compliance is the practice of adhering to laws, industry regulations, and security standards designed to protect sensitive data and digital systems from unauthorized access, breaches, and misuse. For growing businesses, it's both a legal obligation and the baseline that determines whether your security posture can withstand scrutiny.
Compliance vs. General Cybersecurity
Compliance sets the minimum bar — required controls defined by external bodies — while cybersecurity is the broader practice of defending systems against evolving threats. A business can be compliant but still vulnerable if it only meets baseline requirements. An organization can also be highly secure but not formally compliant if it hasn't completed required documentation or audits.
Every compliance program is built on the same foundational components, working together rather than in isolation:
- Identify, assess, and mitigate security risks to data and systems
- Restrict access to sensitive data through authentication and authorization controls
- Encrypt data in transit and at rest with secure storage practices
- Document procedures for detecting, responding to, and reporting security incidents
- Train staff on security policies and their specific compliance responsibilities
- Maintain audit trails, conduct regular reviews, and keep records audit-ready

Major Cybersecurity Compliance Frameworks and Standards
Different frameworks exist for different industries, geographies, and data types. Businesses often need to comply with multiple standards simultaneously, so understanding each framework's scope helps prioritize effort and resources.
GDPR (General Data Protection Regulation)
GDPR applies to any organization handling personal data of EU citizens, regardless of where the business is headquartered. Core requirements include:
- Lawful data collection with explicit consent
- Right to erasure (the "right to be forgotten")
- Breach notification within 72 hours of discovery
- Data minimization and purpose limitation
- Cross-border transfer safeguards
Fines can reach €20 million or 4% of global annual revenue, whichever is higher. Notable recent penalties include a €1.2 billion fine against Meta in 2023 for unlawful data transfers.
HIPAA (Health Insurance Portability and Accountability Act)
HIPAA is the US healthcare standard governing how providers, insurers, and their partners handle Protected Health Information (PHI). Its three core rules require:
- Privacy Rule — Sets limits on PHI uses and disclosures without patient authorization
- Security Rule — Requires administrative, physical, and technical safeguards for electronic PHI
- Breach Notification Rule — Mandates notification following breaches of unsecured PHI
Business Associates (third-party vendors) are directly liable for Security Rule compliance. Healthcare breaches cost an industry-leading $7.42 million on average.
PCI DSS (Payment Card Industry Data Security Standard)
PCI DSS applies to any organization that stores, processes, or transmits payment card data. Key requirements include:
- Network segmentation to isolate cardholder data environments
- Encryption of cardholder data in transit and at rest
- Regular vulnerability scanning and penetration testing
- Strong access controls with unique IDs for each user
- Continuous monitoring and logging of network access
Failure affects the ability to accept card payments and can result in steep contractual fines from payment brands and acquiring banks. Non-compliance can lead to loss of card processing privileges.
ISO/IEC 27001
ISO 27001 is a globally recognized standard requiring organizations to establish an Information Security Management System (ISMS). The 2022 revision streamlined Annex A to 93 controls across four categories:
- Organizational (37 controls)
- People (8 controls)
- Physical (14 controls)
- Technological (34 controls)
Over 70,000 certificates have been issued globally, making ISO 27001 certification a recognized requirement for enterprise and government procurement.
NIST Cybersecurity Framework (CSF)
NIST CSF is widely used in the US, especially by federal agencies and contractors. Released in version 2.0 in February 2024, it organizes security around six functions: Govern (new in v2.0), Identify, Protect, Detect, Respond, and Recover.
The Govern function signals a key shift — cybersecurity is now framed as a major enterprise risk requiring direct senior leadership oversight, not just an IT department concern.
SOC 2
SOC 2 is a trust-based framework developed by the AICPA, particularly important for SaaS companies and cloud service providers. It evaluates controls across five criteria:
- Security
- Availability
- Processing integrity
- Confidentiality
- Privacy
SOC 2 Type II certification is increasingly a procurement requirement. 85% of enterprise buyers now require SOC 2 reports before signing contracts. Unlike a Type I report (a point-in-time snapshot), Type II proves that security controls operated reliably over a 3–12 month period.
Each of these frameworks addresses a distinct risk surface — and for most businesses, two or more will apply at once. Knowing which overlap and which conflict is where compliance planning starts.
Cybersecurity Compliance Requirements by Industry
Which compliance frameworks apply to your business depends on your industry, the data you handle, and where you operate. Getting that mapping wrong — missing a required framework or underestimating its scope — is one of the most common ways organizations land in enforcement trouble.
Healthcare
HIPAA applies to US healthcare organizations and any third-party vendors that handle patient data. Core requirements are non-negotiable:
- Conduct documented risk assessments
- Enforce access controls limiting data to authorized personnel
- Maintain breach notification procedures with defined timelines
In 2025, HHS OCR issued 21 settlements, heavily targeting organizations that skipped or inadequately performed risk analyses. Penalties can reach $2,190,294 per violation per year.
Financial Services
The financial sector faces multiple overlapping requirements:
- SOC 2 for service organizations and cloud vendors
- FFIEC IT Handbook requirements for supervised financial institutions
- GLBA (Gramm-Leach-Bliley Act) obligations for customer data notification, with the 2023 update requiring breach reporting within 30 days for non-banks affecting 500+ consumers
- SEC cybersecurity disclosure rules introduced in 2023, mandating material breach disclosure within 4 business days
Retail and E-Commerce
Any business accepting card payments must comply with PCI DSS regardless of size or transaction volume. Consumer-facing businesses are also subject to data privacy laws such as GDPR, CCPA (California Consumer Privacy Act), and similar state-level regulations. CCPA applies to businesses with gross annual revenue over $25 million or those handling personal data of 100,000+ California consumers.
Government and Defense Contractors
Organizations doing business with US federal agencies must comply with FISMA and NIST 800-53 guidelines. Defense contractors specifically must also meet DFARS requirements and obtain Cybersecurity Maturity Model Certification (CMMC).
CMMC 2.0 took effect November 10, 2025, launching a three-year rollout. It requires third-party assessments of security posture measured against NIST SP 800-171 — meaning self-attestation is no longer sufficient for most contracts.
5 Steps to Achieve Cybersecurity Compliance
Most businesses don't fail compliance audits because of missing technology — they fail because of gaps in process, documentation, and ongoing oversight. These five steps help build a posture that holds up under scrutiny.
Step 1: Identify Applicable Regulations and Frameworks
Map your business's industry, geography, data types handled, and customer base to determine which frameworks apply. A company serving EU customers that also processes payments must navigate both GDPR and PCI DSS simultaneously. Consider:
- Industry sector — Healthcare, finance, retail, government
- Data types — Personal data, health records, payment information
- Geographic reach — EU, California, Virginia, other jurisdictions
- Customer requirements — Enterprise buyers often mandate SOC 2 Type II
Step 2: Conduct a Risk Assessment and Gap Analysis
A risk assessment identifies current vulnerabilities, security gaps, and areas where controls fall short of regulatory requirements. A gap analysis then compares your current state to framework requirements and produces a prioritized list of remediation actions.
According to NIST SP 800-30, risk assessments should not be "simply one-time activities" but employed on an ongoing basis. Conduct assessments at least annually and after major organizational or infrastructure changes.
Step 3: Implement Required Controls and Policies
Most frameworks require these key control categories:
- Access controls and multi-factor authentication — Restrict system access to authorized users only
- Data encryption in transit and at rest — Protect sensitive information through cryptographic controls
- Network segmentation — Isolate sensitive systems and data from general networks
- Patch management — Apply security updates promptly to address vulnerabilities
- Written security policies — Document procedures, responsibilities, and standards
Controls must be formally documented, not just implemented, to satisfy auditors. According to the Verizon 2025 DBIR, exploited vulnerabilities caused 20% of breaches (a 34% year-over-year increase), while stolen credentials accounted for 31%—making access controls and patch management critical priorities.
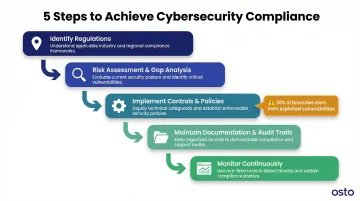
Step 4: Maintain Documentation and Audit Trails
The compliance maxim is clear: "if it isn't documented, it didn't happen." Auditors typically expect:
- Risk assessment reports and gap analysis findings
- Security policy records and version history
- Access logs showing who accessed what and when
- Incident response records and breach notifications
- Vendor assessments and third-party security reviews
- Training attendance and acknowledgment records
Osto's Audit Logs feature automatically captures administrative activities and authentication events, making it easier for growing teams to maintain these records without a dedicated compliance function.
Step 5: Monitor Continuously and Review Regularly
Regulations update, infrastructure changes, and new threats emerge — any of which can quietly erode a previously compliant posture. Continuous monitoring catches misconfigurations, unauthorized access, and policy drift before they become audit failures.
Build a review cadence that matches your risk exposure:
- Schedule formal compliance reviews annually at minimum, or quarterly in heavily regulated industries
- Track regulatory updates such as CMMC 2.0 rollout timelines and SEC disclosure rule changes
- Trigger additional reviews after new product launches, cloud infrastructure changes, or security incidents
Common Compliance Challenges for Growing Businesses
Growing businesses and startups typically lack dedicated compliance personnel or large IT budgets, yet face the same regulatory requirements as large enterprises. The gap between what's required and what's resourced is where most compliance failures originate.
Managing Multiple Frameworks at Once
A scaling business may simultaneously need to address GDPR for EU customers, SOC 2 for enterprise sales, and PCI DSS for payment processing. 58% of organizations conduct four or more audits annually, creating real audit fatigue. Managing overlapping controls manually is time-consuming and error-prone.
Unified platforms that map controls across multiple frameworks eliminate redundant work through a "build once, comply many" approach — one control implementation satisfies requirements across several standards simultaneously.
Doing More With Lean Teams
Maintaining compliance requires continuous monitoring, documentation, and remediation — activities that typically demand full-time staff. Most growing businesses don't have that bandwidth. The practical answer is tooling that handles the heavy lifting automatically.
Osto's platform addresses both challenges directly. It provides unified cloud security posture management across AWS, Azure, and GCP, with automated periodic discovery of 35+ resource types. Key capabilities include:
- Real-time threat detection with built-in audit logs
- Automated misconfiguration checks across cloud resources
- Audit-ready documentation maintained continuously
- Step-by-step remediation guidance for closing compliance gaps

Organizations can monitor their full security posture from a single dashboard — no large IT department required.
Frequently Asked Questions
What are the 5 steps to compliance?
Compliance follows five core steps:
- Identify applicable regulations and frameworks based on your industry and data types
- Conduct a risk assessment and gap analysis to surface current vulnerabilities
- Implement required controls and document security policies
- Maintain comprehensive documentation and audit trails
- Monitor your environment continuously and run regular compliance reviews
What are top 3 skills for a compliance analyst?
Three skills stand out:
- Regulatory knowledge: Deep familiarity with frameworks like GDPR, HIPAA, NIST, and SOC 2
- Risk assessment: Analytical thinking to identify vulnerabilities and prioritize remediation
- Documentation and communication: Translating controls into audit-ready evidence and clear stakeholder reporting
What is the difference between cybersecurity compliance and cybersecurity?
Cybersecurity is the broader discipline of protecting systems, networks, and data from threats through technical and administrative controls. Cybersecurity compliance specifically refers to meeting externally mandated standards and regulations. A business can be technically secure without being formally compliant (lacking documentation or certifications), and vice versa (meeting minimum requirements but remaining vulnerable to advanced threats).
What happens if a company fails to meet cybersecurity compliance requirements?
Penalties range from steep fines — up to €20 million or 4% of global revenue under GDPR, $2.19 million per violation under HIPAA — to legal liability, lost customer trust, and restricted ability to operate in certain markets. Reputational damage can persist well after the incident itself.
Which cybersecurity compliance framework should a small business start with?
It depends on your industry: healthcare businesses start with HIPAA, payment processors with PCI DSS, and those seeking enterprise credibility typically pursue SOC 2 or ISO 27001. For organizations without a sector-specific mandate, the NIST CSF is a flexible, scalable starting point that works across industries.
How often should a cybersecurity compliance program be reviewed and updated?
Annual reviews are the baseline. Trigger additional reviews for events like regulatory updates, new products or services, infrastructure changes, vendor transitions, or security incidents. Healthcare and finance businesses should aim for quarterly reviews to stay ahead of compliance gaps.