The core challenge is straightforward: as businesses scale and adopt multi-cloud infrastructure and remote-work models, their attack surface expands faster than most security teams can manage. With 89% of enterprises now operating multi-cloud environments, every new cloud workload, remote endpoint, and third-party integration introduces unique threat vectors. Point-solution approaches—deploying separate tools for firewall protection, endpoint security, cloud monitoring, and web application defense—create critical gaps, generate overwhelming alert fatigue, and slow incident response precisely when speed matters most.
This article covers the key types of enterprise cybersecurity solutions, how modern AI and cloud capabilities are transforming the security landscape, and how to build a layered, future-proof security architecture that protects your organization without requiring an enterprise-sized IT department.
TLDR
- Enterprise breach costs averaged $4.88 million globally in 2024, with vulnerability exploitation up 180%
- Unified security platforms outperform fragmented tools — fewer blind spots, less alert fatigue, faster response
- AI-driven detection saves an average of $1.9 million per breach by catching threats signature-based tools miss
- 40% of breaches span multiple environments — unified visibility across AWS, Azure, and GCP closes that gap
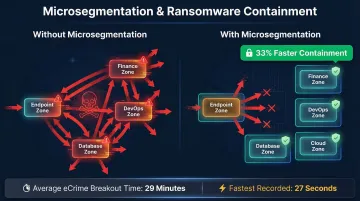
- Zero Trust and microsegmentation contain ransomware up to 33% faster by blocking lateral movement
What Are Cybersecurity Solutions for Enterprise Networks?
Enterprise cybersecurity solutions are the tools, technologies, and practices designed to detect, prevent, and respond to threats across an organization's networks, applications, data, and users. Unlike basic small-business setups that protect a single office network, enterprise-grade security must cover far more ground.
That means securing distributed environments: remote endpoints scattered across continents, multi-cloud workloads on AWS, Azure, and GCP, and third-party integrations connecting your systems to vendors, partners, and customers.
Each of these elements introduces distinct threat vectors:
- A misconfigured S3 bucket can expose customer data
- An unmanaged remote laptop can become a ransomware entry point
- An unsecured API can leak sensitive business logic to attackers
- A third-party integration with weak access controls can compromise your entire supply chain
Why Unified Beats Fragmented
The problem with deploying separate point solutions—one vendor for firewalls, another for endpoint protection, a third for cloud security—is that disparate tools create blind spots, generate alert fatigue, and pull your team away from actual defense work. Research shows that large enterprises use an average of 45 distinct cybersecurity tools, leaving 59% of SOC teams buried in alert overload and 46% spending more time managing vendor sprawl than stopping threats.

A unified, integrated approach consolidates visibility into a single dashboard, correlates security events across layers, and reduces the operational burden on stretched IT teams. When your web application firewall, cloud posture management, and endpoint protection all feed into one platform, cross-layer threats become visible early. You can catch an attacker moving from a compromised endpoint into your cloud infrastructure before the situation escalates.
Core Types of Enterprise Cybersecurity Solutions
Network Security (Firewalls and Intrusion Detection/Prevention)
Next-generation firewalls (NGFWs) represent the first line of perimeter defense for enterprise networks. Unlike traditional packet-filtering firewalls that simply check source and destination addresses, NGFWs inspect application-layer traffic, detect anomalies, and enforce granular policies based on user identity, application type, and threat intelligence.
Intrusion Detection and Prevention Systems (IDS/IPS) complement firewall protections by monitoring internal and external traffic for malicious patterns. When an IDS identifies suspicious behavior—such as unusual data exfiltration or lateral movement between network segments—it alerts security teams. An IPS goes further, actively blocking the threat before it can progress.
The NGFW market reflects enterprise demand for these capabilities, growing from $5.82 billion in 2024 to a projected $6.40 billion in 2025.
Endpoint Detection and Response (EDR)
EDR solutions continuously monitor endpoint devices—laptops, servers, mobile devices—for suspicious behavior, enabling rapid isolation and remediation of compromised machines. This capability is essential in environments with remote workers and BYOD policies, where traditional perimeter-based controls alone cannot provide sufficient protection.
The stakes are high: over 90% of successful ransomware attacks that reach the encryption stage originate from unmanaged devices. When employees connect personal devices or work from home networks without EDR coverage, attackers exploit these gaps to gain initial access and move laterally through your infrastructure.
Web Application Firewall (WAF) and API Security
WAFs protect web-facing applications by filtering malicious HTTP/S traffic before it reaches application logic. They block threats like SQL injection, cross-site scripting (XSS), and other OWASP Top 10 vulnerabilities that exploit weaknesses in web application code.
API security has become equally critical. 37% of organizations experienced an API security incident in the past year, with 66% managing more than 100 APIs. Traditional WAFs cannot parse complex API logic abuse, leaving "zombie" and "shadow" APIs—undocumented or forgotten endpoints—exposed to attack. Modern WAF solutions must include dedicated API security capabilities that discover all APIs, monitor for anomalous usage patterns, and enforce rate limiting and authentication controls.
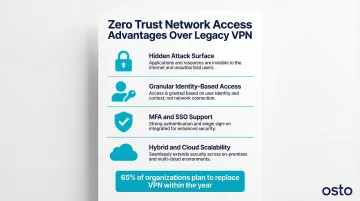
Zero Trust Network Access (ZTNA)
Zero Trust is a security model that eliminates implicit trust based on network location. Every user, device, and application must be continuously authenticated and authorized before accessing resources—even if they're already inside the network perimeter.
This model is replacing traditional VPNs for enterprises managing hybrid workforces and cloud-distributed applications. 65% of organizations plan to replace VPN services within the year, driven by an 82.5% surge in VPN vulnerabilities.
ZTNA delivers several advantages over legacy VPN architecture:
- Reduces the attack surface by hiding internal resources from the public internet
- Enforces granular, identity-based access controls per application
- Supports modern authentication methods like MFA and single sign-on (SSO)
- Scales cleanly across hybrid and cloud-distributed environments
Cloud Security and CSPM
Cloud Security Posture Management (CSPM) continuously scans cloud environments for misconfigurations, compliance violations, and risky resource exposures. Misconfiguration is now the #1 threat to cloud computing, according to the Cloud Security Alliance.
As organizations operate across AWS, Azure, and GCP simultaneously, centralized posture visibility becomes essential to prevent security drift between environments. When data from all three providers is consolidated into a single dashboard, teams can assess posture holistically rather than switching between platforms and missing cross-cloud risks.
Osto's Cloud Security module delivers unified posture analysis across Azure, AWS, and GCP, with automated discovery of 35+ resource types per provider, enriched metadata, and built-in security checks designed for teams without dedicated cloud security staff.
SIEM and Automated Threat Correlation
SIEM platforms aggregate and correlate log data from across the enterprise environment—network devices, endpoints, cloud infrastructure—to detect threats that individual tools would miss. By analyzing patterns across disparate data sources, SIEM identifies anomalies like a user logging in from two continents within minutes or unusual data transfers from a database server.
Modern SIEM feeds into Security Orchestration, Automation, and Response (SOAR) capabilities to reduce mean-time-to-detect and mean-time-to-respond. Organizations using extensive security AI and automation identified and contained breaches nearly 100 days faster than those without these technologies, translating to an average cost savings of $1.9 million per breach.
The Role of AI and Cloud in Modern Enterprise Security
From Signatures to Behavioral Analysis
Traditional security tools rely on signature-based detection—matching known malware patterns or attack signatures against observed activity. This approach fails against modern threats. 82% of detections are now malware-free, with attackers using fileless malware, living-off-the-land techniques, and zero-day exploits that bypass static rule sets.
AI models that learn normal behavior patterns can catch what traditional tools miss. Rather than looking for known-bad signatures, AI-driven systems establish baselines of normal user behavior, network traffic, and application activity, then flag deviations that indicate compromise.
Adaptive Web Protection
AI-powered web protection profiles normal traffic behavior adaptively, flagging anomalies in real time rather than relying on predefined rules. Osto's AI-driven web scanner delivers 2x faster scan execution with improved detection accuracy, using machine learning algorithms to categorize vulnerabilities by severity and generate detailed remediation guidance.
Fewer false positives also means less alert fatigue. When security teams can trust that flagged anomalies represent genuine threats, they respond faster and more effectively.
Automated Cloud Resource Discovery
As cloud infrastructure scales dynamically, automated periodic scanning discovers new resource types, enriches them with metadata, and flags misconfigurations. Without this, cloud sprawl takes hold: development teams spin up instances, storage buckets, and databases faster than security can track them.
Osto's CSPM module automatically discovers 35+ resource types across AWS, Azure, and GCP. Each resource is enriched with metadata covering:
- Configuration and networking details
- Identity and access assignments
- Encryption status and policy compliance
Near real-time posture evaluation surfaces misconfigurations immediately, with step-by-step remediation guidance that enables even lean teams to maintain strong cloud security posture.
Multi-Cloud Unified Visibility
When security data from AWS, Azure, and GCP is consolidated into a single inventory and dashboard, security teams can assess posture across all environments at once rather than switching between platforms and missing cross-cloud risks. That breadth matters: 40% of data breaches involve data distributed across public clouds, private clouds, and on-premises infrastructure simultaneously.
AI for Compliance Oversight
AI also supports compliance oversight. Automated audit logging, anomaly alerting, and posture scoring create the paper trail organizations need to demonstrate compliance to regulators and auditors on an ongoing basis. Compliance reports are available on demand — no scrambling at audit time.
Building a Layered Security Architecture for Enterprise Networks
Defense in Depth
No single solution provides complete protection. Enterprise security must layer multiple controls—perimeter, network, application, identity, data, and endpoint—so that when one layer fails, others compensate. This defense-in-depth principle acknowledges that breaches are inevitable and focuses on limiting their impact.
Microsegmentation Limits Lateral Movement
Once an attacker breaches the perimeter, segmenting internal network zones ensures they cannot freely navigate to high-value assets. Microsegmentation reduces ransomware containment time by up to 33%, effectively limiting the blast radius of an attack.
This is especially important given that the average eCrime breakout time has dropped to just 29 minutes, with the fastest recorded at 27 seconds. When attackers move this quickly, microsegmentation provides critical time for detection and response teams to contain the threat before it spreads.
Identity and Access Management (IAM) and MFA
Breached credentials remain the most common attack entry point, appearing in 31% of all breaches over the past 10 years. Strong identity controls are non-negotiable, no matter what other tools you deploy. That means putting in place:
- Multi-factor authentication (MFA) on all user accounts, especially privileged ones
- Role-based access controls (RBAC) to enforce who can access what
- Least-privilege principles so compromised accounts can only reach a narrow slice of resources
Audit Logs and Compliance Monitoring
Audit logs and compliance monitoring aren't just for regulatory reporting — they're an active detection layer. They surface unauthorized access patterns and configuration changes in real time, enabling security teams to investigate incidents and demonstrate compliance continuously.
The Consolidation Advantage
Organizations that move from separate point tools to a unified security platform gain centralized visibility, reduced operational overhead, and faster cross-layer correlation. For scaling enterprises that can't staff a large SOC team, this matters enormously.
When web application protection, cloud posture management, endpoint security, and Zero Trust access all feed into a single dashboard, lean teams can monitor threats holistically — and respond faster than teams juggling 45 different tools.
How to Choose the Right Cybersecurity Solution for Your Business
Start with Assessment
Before evaluating vendors, define your organization's risk profile. Identify the most critical assets—customer databases, intellectual property, financial systems—and map your attack surface. Where are your endpoints? Which cloud workloads handle sensitive data? What web applications are public-facing? Conduct a vulnerability assessment or security audit to evaluate your current security gaps objectively.
Key Evaluation Criteria for Growing Enterprises
Three factors consistently separate the right platform from the rest:
- Scales with your infrastructure as you add cloud environments, remote users, and web applications — without requiring a platform rebuild
- Designed for lean teams, with centralized dashboards, AI-curated policies, and automated discovery that reduce reliance on specialist expertise
- Connects with AWS, Azure, GCP, Active Directory, and SSO providers to cut deployment friction and accelerate time-to-protection

Osto is built around exactly these criteria — a unified platform covering ZTNA, WAF, and multi-cloud CSPM with one-click recommended policies and automated asset discovery, so growing teams get enterprise-grade protection without needing an enterprise-sized IT department.
Compliance Fit
Beyond core capabilities, regulated industries need to verify compliance fit before committing to a platform. 81% of organizations report current or planned ISO 27001 certification in 2025, making it a dominant framework alongside SOC 2, GDPR, and HIPAA. Platforms with automated audit logging, posture scoring, and compliance dashboards remove the manual effort from regulatory reporting — which matters most when audits arrive unannounced.
Frequently Asked Questions
What are the main types of cybersecurity solutions?
The primary categories include network security (firewalls, IDS/IPS), endpoint protection (EDR), cloud security (CSPM), web application security (WAF), identity management (ZTNA, MFA, IAM), and SIEM/SOAR platforms. Most enterprise environments require a combination of these to achieve comprehensive protection.
What is enterprise network protection?
Enterprise network protection is the combination of technologies and policies that secure an organization's network traffic, connected devices, and data from unauthorized access and malicious activity. It spans perimeter defenses, internal segmentation, and continuous monitoring.
What is Zero Trust and why does it matter for enterprise security?
Zero Trust eliminates implicit trust inside the network, requiring continuous verification of every user and device. It's essential for distributed, cloud-native, and remote-work environments — traditional perimeter-based security simply cannot protect resources that live outside the corporate network.
How do I know if my business needs a dedicated cybersecurity solution?
Any organization handling customer data, running cloud infrastructure, enabling remote work, or subject to compliance requirements needs a dedicated cybersecurity solution. Threats scale with your business, and breach costs consistently outpace the cost of prevention.
What is the difference between network security and cloud security?
Network security protects data flow and access within an organization's on-premises or hybrid networks. Cloud security addresses the shared-responsibility challenges of securing data, workloads, and configurations inside environments like AWS, Azure, or GCP.
How does AI improve cybersecurity for enterprise networks?
AI enables behavioral-based threat detection, adaptive protection profiling, and automated response. Security systems can identify novel threats that bypass signature-based tools, reduce false positives, and accelerate incident response without requiring constant manual tuning, saving organizations an average of $1.9 million per breach.