What is USB device control?
USB device control is a security practice that governs which USB devices — such as flash drives, external hard drives, or peripherals — are allowed to connect to organizational endpoints. It enforces policies that block unauthorized devices, monitor data transfers, and prevent data leakage, protecting sensitive business information from insider threats and accidental exposure.
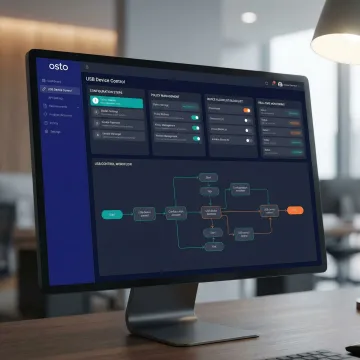
How to change USB controlled by this device?
With Osto, USB device control settings are managed directly from the centralized dashboard. Admins can update Device Control policies per user, group, or device type at any time. Navigate to the Device & Application Control module, select the relevant policy, and modify access rules — changes take effect on the endpoint once the Osto Agent syncs the updated configuration.
What types of USB devices can Osto control?
Osto's Device Control module supports governance over a wide range of USB-connected devices including storage devices, portable media, and peripherals. Policies can be configured to allow, block, or monitor specific device categories — giving administrators precise control over what can connect to organizational endpoints without disrupting legitimate business workflows.
Does Osto's USB device control work on macOS?
Yes. The Osto Agent supports macOS versions 14 and 15, enabling USB device control policies on Apple endpoints. Admins can verify which users have installed the Agent App and send bulk notifications to users who haven't yet deployed it — ensuring comprehensive endpoint coverage across both macOS and other supported operating systems.
How does Osto detect USB-related security incidents?
Osto's enhanced endpoint incident detection provides user-level visibility into USB activity, enabling admins to identify, investigate, and respond to suspicious events with precision. When an unauthorized device is connected or a policy is violated, the system flags the incident with detailed context — including the user, device, timestamp, and action taken — for rapid investigation.
Can I assign different USB access policies to different teams or users?
Absolutely. Osto's User & Group Management module allows admins to assign users to groups and apply tailored USB device access policies following the principle of least privilege. A user policy toggle enables quick switching between individual and group-level policies, making it easy to grant the right level of USB access for each role without excessive permissions.
Are USB device activities logged for compliance purposes?
Yes. Osto's Audit Logs module captures enhanced tracking of all USB device interactions, policy changes, and administrative actions with richer detail and better visibility. This provides the transparency and compliance oversight organizations need for internal audits, regulatory requirements, and ongoing security reviews — with authentication logs included for comprehensive monitoring.
How quickly can USB device control be deployed across an organization?
Deployment is designed to be fast and frictionless. After configuring policies in the Osto dashboard, the Agent App is distributed to endpoints with pre-built installation message templates that can be shared via official communication channels. Admins can track deployment progress, identify users missing the Agent, and send bulk reminders — enabling organization-wide rollout within hours.