User & Group Management
Assign users to groups, apply least-privilege access policies, and streamline policy management with an intuitive toggle between individual users and user groups—reducing administrative overhead significantly.
Managing who has access to what—and ensuring that access is appropriate, auditable, and compliant—is a growing challenge for modern businesses. Osto's identity governance solutions deliver centralized user management, least-privilege access controls, detailed audit logs, and zero trust principles, giving your organization full visibility and control over every identity across your environment.
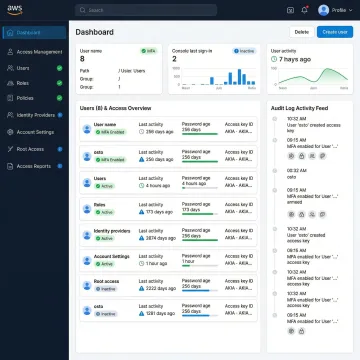
Comprehensive identity and access governance tools to enforce least-privilege, ensure auditability, and secure every user in your organization.
Assign users to groups, apply least-privilege access policies, and streamline policy management with an intuitive toggle between individual users and user groups—reducing administrative overhead significantly.
Empower Super Admins to onboard multiple Admins with tailored, role-specific permissions—enabling granular governance and ensuring no one holds more access than their responsibilities require.
Gain deep visibility into every administrative action and authentication event with enhanced tracking, richer detail, and compliance-ready reporting that keeps your security team fully informed.
Implement Zero Trust principles with secure authentication workflows and access controls that ensure no user or device is trusted by default—protecting your network from insider and external threats alike.
Enforce multi-factor authentication for all server connections, use unique per-user credentials, and monitor access logs to detect and investigate unauthorized or anomalous server access in real time.
Holistic identity security that governs access across your entire environment, ensuring every identity is authenticated, authorized, and continuously monitored for suspicious or non-compliant behavior.
Modern businesses face an expanding identity perimeter—remote teams, cloud environments, and third-party integrations all introduce access risk. Osto's identity governance platform centralizes user lifecycle management, enforces least-privilege across every role, and delivers compliance-ready audit trails without requiring a large IT department. Whether you're a fast-growing startup or a scaling enterprise, you get enterprise-grade identity control in a single, easy-to-use dashboard—giving your security team the clarity and confidence to act fast.

Osto delivers a unified, intelligent platform that makes identity governance accessible, auditable, and scalable for businesses of every size.
Every user and group is assigned only the minimum access needed, reducing the attack surface across your entire organization.
Manage all admins, users, and permissions from one intuitive dashboard—no complex tooling or large IT team required.
Comprehensive audit logs with enriched authentication tracking provide the transparency your compliance and security teams demand.
Built on Zero Trust principles with MFA enforcement and unique per-user credentials ensuring secure access to every resource.
A dedicated team building next-generation identity and cybersecurity solutions.
Osto was built with a clear mission: to simplify security for new age businesses without sacrificing enterprise-grade protection. As organizations scaled into multi-cloud environments and remote work became standard, the challenge of managing who has access to what grew exponentially. Osto's team recognized that growing startups and scaling enterprises needed powerful identity governance tools that didn't require a large IT department to operate. From launching core identity and access controls to continuously expanding into AI-powered threat detection and comprehensive audit capabilities, Osto has remained committed to delivering transparent, centralized, and compliance-ready security for every organization—regardless of size or technical maturity. Reach the team at connect@osto.one.
An identity governance tool is a software solution that helps organizations manage, monitor, and control who has access to systems, applications, and data. It enforces policies like least-privilege access, automates user lifecycle management (onboarding and offboarding), and generates audit trails to ensure accountability and compliance. Platforms like Osto combine these capabilities into a single, centralized dashboard.
Talk to our experts for a personalized walkthrough of Osto's identity governance capabilities.
Architected on verified Zero Trust security principles.
Full governance coverage across AWS, Azure, and GCP.
Machine learning certified for intelligent threat detection.
Fill out the form below and an Osto specialist will reach out to discuss your organization's access governance needs, walk you through the platform, and help you get started quickly.
You can also send us a quick email at connect@osto.one.
You can also send us a quick email at connect@osto.one.