Endpoint Detection & Response
Continuous monitoring of all endpoints to detect suspicious behaviors, malware, and advanced threats in real time, enabling rapid investigation and automated containment before damage spreads across your network.
Cyber threats evolve fast—your endpoint security needs to keep pace. Osto's Managed EDR Services deliver continuous monitoring, real-time threat detection, and rapid response across all your devices. From lateral movement detection to automated containment, we give your business enterprise-grade endpoint protection without the complexity of managing it in-house. Stop breaches before they spread.

Comprehensive endpoint protection solutions covering detection, response, control, and compliance for your entire device fleet.
Continuous monitoring of all endpoints to detect suspicious behaviors, malware, and advanced threats in real time, enabling rapid investigation and automated containment before damage spreads across your network.
Centralized control over which devices and applications are permitted across your environment, with user-level visibility for precise incident detection and enforcement of security policies through an intuitive dashboard.
Expert-led threat hunting and investigation services that analyze endpoint incidents, trace attack paths, and deliver swift containment and remediation to minimize dwell time and business disruption.
Comprehensive audit logging that tracks all endpoint activity, administrative changes, and authentication events—providing the transparency and compliance oversight needed for regulatory requirements and security governance.
Enforce least-privilege access policies and manage user and group permissions to ensure only authorized identities interact with critical endpoints, reducing the attack surface from insider threats and credential abuse.
Extend endpoint security with Zero Trust principles, ensuring every device and user is verified before accessing resources—securing remote workforces with strong authentication workflows and granular access controls.
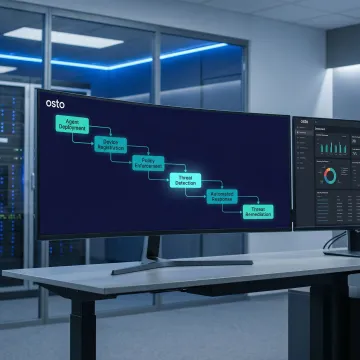
We deploy the Osto Agent across your endpoints—Windows, macOS, and beyond—with streamlined onboarding. Admins receive instant visibility into which devices have the agent installed, and users are notified automatically via built-in messaging tools for a frictionless rollout.
Osto combines AI-powered detection, expert oversight, and a unified platform to deliver endpoint security that scales with your business.
Manage endpoints, cloud security, and access controls from one centralized dashboard—no siloed tools required.
Machine learning algorithms continuously analyze endpoint behavior, catching threats that signature-based tools routinely miss.
Automated containment and expert-led remediation minimize dwell time, stopping threats before they escalate into full incidents.
Designed for startups and growing enterprises that need enterprise-grade endpoint protection without a large in-house IT security team.
Dedicated cybersecurity experts committed to protecting your endpoints and business.
Osto was built with a singular mission: to make enterprise-grade cybersecurity accessible to new age businesses, startups, and scaling enterprises. Recognizing that most growing organizations lack the resources to staff a full security operations center, Osto developed a comprehensive, managed platform that does the heavy lifting for them. Since its inception, the platform has grown rapidly—launching cloud security posture management for Azure, AWS, and GCP, AI-powered web protection, Zero Trust Network Access, and full endpoint detection and response capabilities within a remarkably short timeframe. Each milestone reflects Osto's commitment to staying ahead of the threat landscape while keeping security simple, transparent, and actionable. Today, Osto serves as a trusted cybersecurity partner for organizations that demand agility and resilience.
Managed EDR (Endpoint Detection and Response) is a fully outsourced security service where a team of experts monitors, detects, investigates, and responds to endpoint threats on your behalf. Unlike installing software and managing it yourself, managed EDR combines advanced detection technology with human expertise—providing 24/7 threat monitoring, alert triage, incident investigation, and guided remediation without requiring an in-house security operations team.
Talk to an Osto security expert for a free consultation tailored to your business.
Recognized for machine learning-driven threat detection and response
Full posture management certified across Azure, AWS, and GCP
Verified Zero Trust Network Access implementation for secure remote work
Fill out the form below and an Osto security specialist will reach out to assess your endpoint environment and recommend the right managed EDR plan for your business.
You can also send us a quick email at connect@osto.one.
You can also send us a quick email at connect@osto.one.