Introduction
Cloud adoption is accelerating at breakneck speed, with worldwide public cloud spending projected to hit $723.4 billion in 2025—up from $595.7 billion in 2024. Yet this rapid expansion brings mounting security complexity. Traditional perimeter-based security simply doesn't hold up in cloud-native environments where infrastructure is ephemeral, constantly evolving, and distributed across multiple providers.
The stakes are high. Gartner estimates that through 2025, 99% of cloud security failures will be the customer's fault—not the provider's. Orca Security's 2024 report found that 81% of organizations have public-facing neglected assets with open ports. Akamai recorded over 150 billion API attacks between January 2023 and December 2024—each one targeting gaps that attackers already know how to find.
Addressing these threats doesn't require a massive security team—it requires the right framework. This guide covers what cloud-native security actually means, how the 4 C's and 3 R's frameworks work in practice, which threats carry the greatest risk, and which tools growing organizations can act on immediately.
TLDR:
- Cloud-native security integrates protection into every layer—from cloud infrastructure to application code—using dynamic, identity-centric controls instead of static network perimeters
- The 4 C's framework (Cloud, Cluster, Container, Code) provides a layered defense model where each layer's security depends on the outer layers
- Misconfigurations cause 99% of cloud security failures, with over-permissive IAM roles, open ports, and exposed storage buckets topping the list
- Zero Trust architecture, DevSecOps automation, and continuous CSPM monitoring dramatically reduce breach risk and remediation costs
- Unified CNAPP platforms deliver 264% ROI by consolidating tools and eliminating blind spots across multi-cloud environments
What Is Cloud-Native Security?
Cloud-native security is the practice of integrating security into every layer of cloud-based application development, deployment, and operations from the very beginning—not as an afterthought. This represents a fundamental shift from traditional on-premises security, which focused on protecting a fixed network perimeter with firewalls and intrusion detection systems positioned at the network edge.
Traditional security assumed a trusted internal network and an untrusted external one. Cloud-native environments shatter this model. Modern applications use microservices, containers, serverless functions, and APIs—all of which change and scale dynamically in response to demand.
Infrastructure spins up and down in minutes. Services communicate across networks you don't control. Hardware-centric security tools designed for fixed data centers can't keep pace with this constant flux, creating the urgent need for security built specifically for cloud architectures.
The shared responsibility model defines how security accountability is split between cloud providers and their customers. Cloud providers secure the underlying infrastructure—physical data centers, host hardware, network virtualization, and the hypervisor layer. Yet organizations remain responsible for everything that runs on top:
- Configurations — ensuring cloud resources aren't exposed through misconfigurations
- IAM policies — controlling who and what can access resources
- Data protection — encryption, backups, and access logging
- Application security — secure code, patching, and runtime controls
This division varies by service model (IaaS, PaaS, or SaaS), but customers always retain ultimate accountability for data security and identity management.
Most security incidents stem from failures on the customer's side of this model. Misconfigurations, over-permissioned IAM roles, and exposed storage buckets account for the vast majority of cloud breaches. Cloud-native security addresses this directly—embedding security controls into infrastructure-as-code, CI/CD pipelines, and runtime environments so protection keeps pace with the speed of cloud development.
The 4 C's of Cloud-Native Security
The 4 C's framework—Cloud, Cluster, Container, and Code—is an industry-standard layered security model referenced by Kubernetes documentation and the Cloud Native Computing Foundation (CNCF). Each layer depends on the security of the one outside it. Punch through any single layer, and you've compromised everything it was protecting.
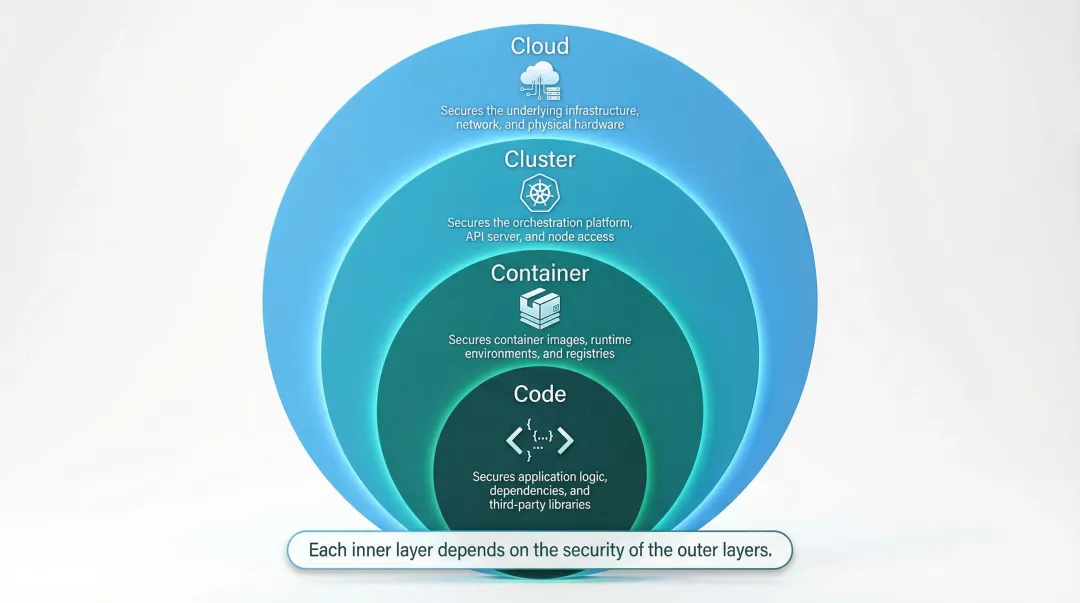
Cloud
The cloud layer is the outermost layer, covering the underlying infrastructure: networks, virtual machines, storage, identity services, and configurations managed with your cloud provider. Misconfigurations at this layer are the most common security failure. Orca Security found that 21% of organizations have at least one public-facing storage bucket with sensitive data that should never be publicly accessible.
Best practices for the cloud layer:
- Encrypt data at rest and in transit using provider-managed or customer-managed keys
- Enforce network segmentation with Virtual Private Clouds (VPCs), security groups, and network access control lists
- Apply provider security recommendations from AWS Security Hub, Azure Security Center, or GCP Security Command Center
- Audit configurations routinely using Infrastructure as Code (IaC) to minimize human error in provisioning
- Maintain compliance with GDPR, HIPAA, and PCI DSS through continuous automated monitoring
Overly permissive access controls, open ports, and misconfigured IAM policies are the most common breach entry points here. Continuous Cloud Security Posture Management (CSPM) catches these configuration drifts before they become incidents.
Cluster
The cluster layer refers to the orchestration environment—typically Kubernetes—that manages and deploys containerized applications. The Kubernetes API server is the most critical component to protect. It should be locked down with role-based access control (RBAC) rules and TLS authentication. Orca Security reports that 82% of organizations have a Kubernetes API server that is publicly accessible, up 12 points from 2022.
Key cluster security practices:
- Restrict API server access to trusted networks only—never expose it publicly
- Implement strict RBAC policies granting minimum necessary permissions per user or service account
- Encrypt inter-component communication using TLS for all control plane and node-to-node traffic
- Apply network policies to isolate workloads and limit lateral movement between namespaces
- Use policy enforcement tools like OPA Gatekeeper to enforce security policies consistently across the cluster
An exposed API server isn't just a configuration problem—it's a direct path to every workload running in your cluster.
Container
The container layer refers to the container images themselves, which can harbor vulnerabilities if not properly maintained. Using untrusted base images or running containers with privileged user accounts grants root-level access to the host, creating catastrophic risk. Sonatype's 2024 report found that 95% of vulnerable downloaded releases already had a fix available, highlighting a significant gap in consumption behavior.
Container security recommendations:
- Scan container images for known vulnerabilities before and during runtime using tools integrated into CI/CD pipelines
- Use only trusted registries like Docker Content Trust, or private registries with image signing enabled
- Update images regularly to eliminate known CVEs and outdated dependencies
- Avoid running containers as root—enforce non-root user policies through Kubernetes pod security standards
- Implement runtime protection to detect and block anomalous container behavior in production
Containers are immutable by design, which works in your favor. That advantage only holds, though, when you start with images that are clean and current.
Code
The code (application) layer is the innermost layer, covering the actual application logic and its dependencies. Common risks include insecure coding patterns like SQL injection, cross-site scripting (XSS), insufficient input validation, and hardcoded credentials. Orca Security's 2025 report revealed that 85% of organizations have plaintext secrets embedded in their source code repositories—a critical vulnerability attackers actively hunt for.
Code layer security best practices:
- Integrate static code analysis tools directly into CI/CD pipelines to catch vulnerabilities on every commit
- Use dependency-checking tools like OWASP Dependency-Check or Snyk to identify vulnerable open-source libraries before they reach production
- Never hard-code secrets—use secrets management tools like HashiCorp Vault or AWS Secrets Manager instead
- Validate all user input to prevent injection attacks and logic bypasses
- Conduct regular code reviews with security-focused checklists to catch logic flaws early
Every other layer exists to buy time and reduce exposure. When application code is the final line of defense, it needs to hold.
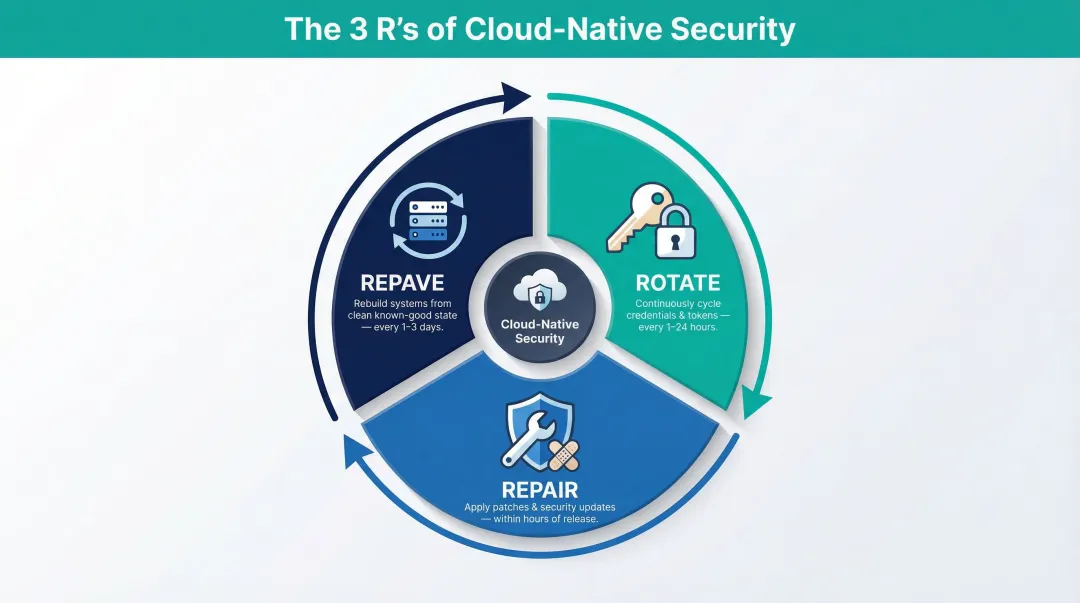
The 3 R's of Cloud-Native Security: Rotate, Repair, Repave
The 3 R's—Rotate, Repair, and Repave—represent a proactive security philosophy for cloud-native environments. The principle is simple: credentials, software, and infrastructure should be treated as temporary and continuously refreshed, minimizing the window attackers have to exploit any single asset.
Rotate
"Rotate" means frequently changing credentials, encryption keys, API tokens, and access certificates—sometimes as often as hourly. Cloud-native applications manage many such secrets across distributed services. Frequent rotation dramatically limits the damage if credentials are compromised. If an attacker steals a token that expires in one hour, their window of opportunity is narrow.
Rotation best practices:
- Automate credential rotation using secrets management tools like HashiCorp Vault, AWS Secrets Manager, or Azure Key Vault
- Rotate encryption keys regularly and maintain key version history for audit purposes
- Use short-lived tokens for service-to-service authentication instead of long-lived static credentials
- Monitor for stale credentials—Orca Security found that 89% of organizations have IAM credentials unused for 90+ days, creating dormant backdoor risks
Rotation is most effective when fully automated — manual processes introduce delay and human error that defeat the purpose.
Repair and Repave
"Repair" means applying security patches and updates as soon as they are released to eliminate known vulnerabilities. "Repave" means periodically rebuilding servers, containers, and services from a known-good secure state — ensuring accumulated drift or hidden compromises don't persist.
Repair and repave strategies:
- Patch operating systems and application stacks within hours of patch availability
- Rebuild containers from base images regularly rather than patching running containers
- Repave virtual machines and servers every few hours in high-security environments to reduce attacker dwell time
- Use immutable infrastructure where servers are replaced rather than updated in place
Repaving is most practical in containerized environments where rebuilds are fast and automated. The 2023 CircleCI breach shows why this matters: malware bypassed 2FA through session cookie theft, establishing persistence that perimeter defenses never caught. Regularly rebuilding infrastructure from clean states invalidates compromised sessions and forces attackers to re-exploit from scratch.
Key Threats and Challenges in Cloud-Native Environments
Cloud-native architectures introduce distinct threats that differ fundamentally from traditional on-premises risks. Understanding these threats is the first step toward effective defense.
Misconfigurations dominate the threat landscape. Incorrectly set IAM permissions, open storage buckets, and exposed ports account for the majority of cloud breaches. These aren't sophisticated zero-day exploits—they're basic configuration errors that automated scanning can detect. Yet 81% of organizations have public-facing neglected assets with commonly exploited open ports, according to Orca Security's 2024 findings.
Insecure APIs are the next major risk. Microservices architectures rely on APIs for service-to-service communication, creating vastly more endpoints than traditional monolithic applications. Akamai documented 150 billion API attacks from January 2023 through December 2024, with API request constraint violations surging 24% year-over-year. APIs that lack proper authentication, input validation, or rate limiting become prime targets for data exfiltration and abuse.
The 2023 Microsoft Storm-0558 incident shows how deep these vulnerabilities run. A China-based threat actor forged authentication tokens using an acquired Microsoft signing key, compromising email accounts at approximately 25 government agencies. The root cause traced back to a 2021 crash dump that incorrectly contained the signing key—plus a validation error that allowed a consumer key to be trusted for enterprise tokens.
Beyond individual vulnerabilities, two structural challenges compound the risk:
- Expanded attack surface: Every microservice, endpoint, and inter-service communication is a potential entry point. Ephemeral resources spin up and disappear within minutes—faster than traditional security tools can track.
- Continuous compliance pressure: Dynamic environments make it hard to know where regulated data lives, who accesses it, and whether configurations stay compliant with GDPR, HIPAA, or SOC 2 at any given moment. Compliance must be automated and ongoing, not a periodic audit.
Best Practices for Implementing Cloud-Native Security
Adopt Zero Trust Architecture
Zero Trust operates on the principle "never trust, always verify." Every request is authenticated regardless of origin. Users and services receive only the minimum permissions necessary (principle of least privilege), and critical systems are segmented from the broader environment. This limits lateral movement if a breach occurs.
NIST SP 800-207 defines Zero Trust as an evolving set of paradigms that move defenses from static, network-based perimeters to focus on users, assets, and resources. Adoption is accelerating—Okta's 2023 report found that 61% of organizations now have a defined Zero Trust initiative, up from just 24% in 2021.
Zero Trust implementation steps:
- Verify every access request with multi-factor authentication (MFA) and continuous session monitoring
- Segment critical systems using network policies and micro-segmentation to contain breaches
- Apply continuous authorization — re-verify sessions dynamically rather than trusting established connections
- Monitor for anomalous behavior and terminate suspicious sessions in real time

Implementing Zero Trust means rethinking access from the ground up: identity-centric policies, device trust verification, and continuous authorization replace the old "inside = trusted" assumption.
Shift Security Left with DevSecOps
Shift-left security means integrating security checks into the earliest stages of the software development lifecycle rather than treating security as a final-phase gate. This includes adding IaC scanning tools like Checkov or tfsec, secret detection in pull requests, and training developers on secure coding fundamentals.
IBM's 2024 Cost of a Data Breach Report reveals that extensive use of security AI and automation in prevention workflows saves organizations an average of $2.2 million per breach. Catching vulnerabilities during development is far less costly than post-deployment remediation — which often means emergency patches, incident response, and regulatory fines.
DevSecOps best practices:
- Integrate SAST and DAST tools into CI/CD pipelines to catch vulnerabilities on every commit
- Scan IaC templates for misconfigurations before infrastructure is provisioned
- Detect secrets in repositories using tools like GitGuardian or TruffleHog
- Train developers on secure coding principles and common vulnerability patterns
- Automate dependency scanning to flag vulnerable open-source libraries before deployment
Teams that embed security into the development workflow consistently report shorter remediation windows and fewer critical vulnerabilities reaching production.
Enforce Robust IAM Practices
Identity is the new perimeter. Over-provisioned IAM roles are one of the leading causes of privilege escalation attacks in cloud environments. Microsoft reports that MFA can block over 99.9% of account compromise attacks, yet 89% of organizations leave IAM credentials active but unused for 90+ days, according to Orca Security's 2025 findings.
IAM best practices:
- Implement MFA across all cloud accounts — preferably phishing-resistant options like FIDO2 or WebAuthn
- Review and revoke unnecessary access regularly through automated entitlement reviews
- Use time-limited credentials rather than permanent access keys
- Scope permissions tightly to each role — no standing access beyond what a task requires
- Monitor for anomalous access patterns and investigate dormant accounts immediately
A compromised identity with minimal permissions causes a fraction of the damage of an over-provisioned one — IAM hygiene is one of the highest-leverage controls available.
Automate Security Monitoring and Posture Management
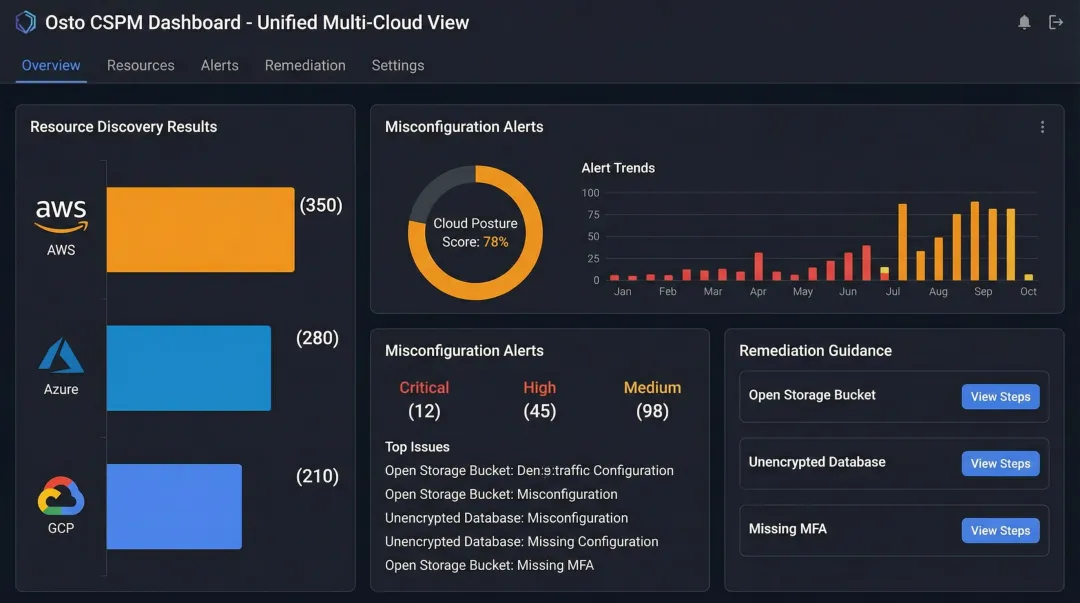
Cloud Security Posture Management (CSPM) tools continuously scan multi-cloud environments for misconfigurations, compliance violations, and security drift. Orca Security data shows that organizations take an average of 27 days to fix a neglected asset alert—a window attackers readily exploit.
CSPM tools automate this detection, providing real-time visibility into misconfigurations before they are exploited. For organizations running workloads across AWS, Azure, and GCP, consolidated multi-cloud CSPM is particularly important. Fragmented views across providers create blind spots.
Platforms like Osto address this directly — automated resource discovery and enriched metadata across AWS, Azure, and GCP in a single dashboard give scaling businesses unified posture visibility without needing a large IT team to manage each provider separately.
Encrypt Everything and Manage Secrets Carefully
Encryption protects data both at rest (in databases, object storage, disks) and in transit (via HTTPS/TLS protocols). Yet encryption is only as strong as your key management. Centralizing secrets management avoids hard-coded credentials in code repositories and ensures keys are rotated regularly.
Encryption and secrets management best practices:
- Encrypt all data at rest using provider-managed or customer-managed encryption keys
- Enforce TLS 1.2 or higher for all data in transit
- Use secrets management tools like HashiCorp Vault, AWS Secrets Manager, or Azure Key Vault
- Never commit secrets to version control — use pre-commit hooks to detect and block them at the source
- Rotate encryption keys regularly and maintain key version history for audit purposes
Exposed credentials in public repositories remain one of the fastest paths to a breach — secrets management closes that gap before attackers find it first.
Essential Tools for Cloud-Native Security
CSPM and Multi-Cloud Posture Tools
CSPM tools continuously assess cloud environments for misconfigurations, compliance gaps, and vulnerabilities. For organizations running workloads across AWS, Azure, and GCP, consolidated multi-cloud CSPM is essential — without it, fragmented views across providers create blind spots that attackers can quietly exploit.
Platforms like Osto offer automated resource discovery and enriched metadata across all three major cloud providers. Osto's CSPM discovers 35+ resource types per cloud provider, including VMs, storage accounts, databases, networking components, and identity services. The platform provides built-in security checks to detect misconfigurations and delivers actionable remediation guidance, giving scaling businesses complete visibility without requiring a large IT team.
WAF, WAAP, and Application Security Tools
Web Application Firewalls (WAF) and Web Application and API Protection (WAAP) solutions are essential for cloud-native environments where applications expose many API endpoints. These tools block injection attacks, DDoS attempts, and malicious bot traffic at the application layer.
Traditional WAFs and modern WAAP platforms handle threats very differently:
- Traditional WAFs rely on signature-based rules and regular expressions — effective for known attack patterns, but brittle against sophisticated, authenticated API abuse
- Modern WAAP platforms use behavioral analysis, machine learning, and anomaly detection to distinguish legitimate traffic from threats without generating excessive false positives
Built on an Nginx-based reverse-proxy architecture, Osto's WAAP uses AI-driven adaptive profiling to automatically detect, monitor, and classify website and API traffic. Threats including DDoS attacks, malicious bots, and OWASP Top 10 vulnerabilities are blocked inline before reaching your origin servers — with low latency and no throughput degradation.

CNAPP Platforms
Tool sprawl is a growing problem for security teams managing complex cloud environments. Cloud-Native Application Protection Platforms (CNAPP) address this by unifying CSPM, Cloud Workload Protection (CWPP), container security, and IaC scanning under one platform. The result: fewer context-switching gaps, unified alerting, and a single shared view across the full cloud attack surface.
A Forrester Total Economic Impact study found that deploying Prisma Cloud delivered a 264% ROI over three years, providing a 48% SecOps team efficiency lift and a 60% time reduction in DevOps efforts fixing vulnerabilities and misconfigurations. Similarly, Microsoft Defender for Cloud delivered a 99% ROI with accelerated threat investigation and remediation.
Frequently Asked Questions
What is cloud-native security?
Cloud-native security is the integration of security practices and tools into every layer of cloud-based application development and operations, specifically designed for the dynamic, scalable nature of cloud environments—unlike traditional on-premises security focused on fixed network perimeters.
What are the best practices for cloud-native security?
Key best practices include adopting zero-trust architecture, shifting security left via DevSecOps, and enforcing least-privilege IAM. Automated CSPM for continuous posture monitoring and encrypting data at rest and in transit round out a solid baseline.
What are the 4 C's of cloud-native security?
The 4 C's—Cloud, Cluster, Container, and Code—represent the four security layers of a cloud-native architecture, where each inner layer depends on the security of the layers surrounding it. Weaknesses in any single layer can compromise the entire stack.
How does cloud-native security differ from traditional security?
Traditional security defended a fixed network perimeter. Cloud-native security is built for environments where infrastructure is ephemeral and constantly changing, requiring identity-centric, workload-level controls rather than boundary-based ones.
What is the shared responsibility model in cloud security?
In the shared responsibility model, the cloud provider secures the underlying infrastructure (hardware, networking, physical data centers), while the customer is responsible for securing their configurations, IAM policies, applications, and data.
What tools are commonly used for cloud-native security?
Common categories include CSPM tools for misconfiguration detection, CNAPP platforms for unified protection, and WAF/WAAP solutions for application and API security. Secrets management and container/IaC scanning tools are typically integrated directly into CI/CD pipelines.
