
Introduction
Businesses of all sizes are migrating to cloud environments for scalability, cost efficiency, and operational flexibility. The worldwide IaaS market grew 22.5% in 2024 to reach $171.8 billion, with 89% of enterprises now running multi-cloud architectures.
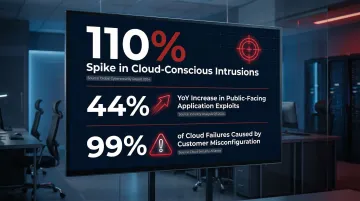
That growth has made cloud infrastructure a prime target. Cloud-conscious intrusions spiked 110%, with attackers actively exploiting APIs, identity systems, and misconfigured storage to gain footholds in environments that were never designed with security as the first priority.
This article covers the fundamentals of cloud infrastructure security, including its definition, key components, common risks, and actionable best practices. You'll also learn how the shared responsibility model divides security duties between cloud providers and customers—and why understanding that division shapes your actual security obligations.
TLDR
- Cloud infrastructure security protects virtual machines, networks, storage, and APIs from breaches and misconfigurations
- Core components include IAM, encryption, network controls, logging, and CSPM
- Top risks: misconfigurations, insecure APIs, weak access controls, and limited visibility
- Best practices: enforce MFA, apply least privilege, monitor continuously, and adopt Zero Trust
- The shared responsibility model splits security duties: providers own physical infrastructure, customers own configurations and data
What Is Cloud Infrastructure Security?
Cloud infrastructure security is the combination of technologies, policies, and controls that protect cloud-based systems from internal and external threats. It covers everything the underlying infrastructure depends on: physical hardware in data centers, virtual compute and storage resources, and the networking layers connecting them — not just the applications running on top.
How It Differs from General Cybersecurity
Traditional cybersecurity focuses on protecting on-premises networks, endpoints, and perimeter defenses. Cloud infrastructure security operates at a different layer — one defined by virtualization, dynamic provisioning, and API-driven access. That means protecting:
- Virtual networks and software-defined perimeters
- Identity and access management systems
- Cloud-native storage and databases
- Control planes that provision and manage resources
Why It Matters Now
Cloud adoption is accelerating, but so are cloud-targeted attacks. Nearly half of all enterprise workloads and data now reside in public clouds, creating an expanded attack surface. Attackers are no longer just targeting endpoints—they're exploiting cloud control planes, APIs, and misconfigurations. IBM X-Force reported a 44% year-over-year increase in exploitation of public-facing applications, demonstrating that cloud infrastructure has become a primary target for sophisticated threat actors.
For startups and scaling businesses, this matters directly. A single misconfigured S3 bucket or exposed API key can hand attackers the keys to your entire cloud environment. Protecting cloud infrastructure requires specialized approaches, continuous monitoring, and a clear understanding of where your responsibility begins and where your provider's ends.
Key Components of Cloud Infrastructure Security
Effective cloud security is built on multiple interconnected layers, each addressing a distinct aspect of infrastructure protection.
Identity and Access Management (IAM)
IAM forms the foundation of cloud access control, defining which users, roles, and services can interact with specific cloud resources and enforcing those permissions consistently across environments. Effective IAM ensures that only authorized identities can access sensitive infrastructure, reducing the risk of unauthorized access or privilege abuse.
IAM should always be paired with Multi-Factor Authentication (MFA) to verify user identity beyond passwords, especially for cloud management consoles and admin accounts. Microsoft research shows that MFA reduces the risk of compromise by 99.22% across all users — making it one of the most effective security controls available.
Yet 45% of AWS organizations have IAM users authenticating to the console without MFA, a critical gap that leaves cloud environments exposed to credential-based attacks.
Network and Device Security
Network security in the cloud involves deploying virtual firewalls, segmentation (VPCs/subnets), intrusion detection systems, and load balancers to filter malicious traffic and limit lateral movement between workloads. Unlike traditional perimeter-based defenses, cloud network security must account for dynamic resource provisioning, distributed architectures, and traffic that flows between cloud services, regions, and external systems.
Properly configured security groups and network access controls ensure that only legitimate traffic reaches your cloud resources, while network segmentation contains potential breaches by isolating sensitive workloads from less critical systems.
Data Encryption
Network controls keep threats out — but encryption ensures that any data intercepted or accessed without authorization cannot be read or misused. Industry standards mandate specific cryptographic algorithms:
- Data at rest: AES-256 encryption protects stored data in cloud databases, storage buckets, and virtual machine disks
- Data in transit: TLS 1.2 and TLS 1.3 secure data moving between services, users, and cloud regions
NIST SP 800-57 recommends AES for symmetric data-at-rest confidentiality, while NIST SP 800-52r2 mandates TLS 1.2 and 1.3 support for data in transit. Organizations must ensure their cloud configurations explicitly enforce these standards and disable deprecated protocols.
Logging, Telemetry, and Analytics
Cloud logging captures access events, configuration changes, and data movement to create an audit trail that supports both security monitoring and compliance. Without it, the average time to identify a breach stretches well beyond what most organizations can afford — IBM's 2023 Cost of a Data Breach report puts the global mean at 204 days.
Analytics tools like SIEM (Security Information and Event Management) systems process log data to identify anomalies, detect threats, and trigger alerts. This enables security teams to catch suspicious patterns — unusual API calls, unauthorized access attempts, or configuration drift — before they escalate into breaches.
Cloud Security Posture Management (CSPM)
CSPM provides continuous assessment of cloud configurations to detect misconfigurations, compliance gaps, and security drift across resources. As cloud environments grow more complex and dynamic, manual audits become insufficient. CSPM tools automate the process of identifying security weaknesses and providing remediation guidance.
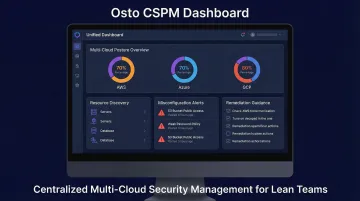
For teams managing multi-cloud environments, Osto centralizes this process with unified posture visibility and automated resource discovery across Azure, AWS, and GCP — without requiring a large security team. Osto's CSPM automatically discovers 35+ resource types per cloud provider and surfaces misconfigurations with step-by-step remediation guidance. That makes it practical for growing businesses to maintain strong security posture across distributed infrastructure without dedicated cloud security staff.
Common Risks and Threats to Cloud Infrastructure
Cloud environments face a distinct set of threats — many of them self-inflicted. Knowing where breaches originate is the first step toward closing the gaps that attackers consistently exploit.
Misconfigurations
Cloud misconfigurations—such as open S3 buckets, overly permissive security groups, or exposed databases—are the leading cause of cloud breaches. Gartner predicts that 99% of cloud security failures through 2025 will be the customer's fault, with misconfiguration being the primary culprit.
Real-world examples underscore the severity:
- Capital One (2019): A misconfigured web application firewall enabled unauthorized access to personal information of roughly 100 million individuals
- Indian Banking Data Leak (2025): UpGuard researchers discovered a publicly accessible S3 bucket containing over 273,000 documents exposing unredacted account numbers and personal information
In both cases, no sophisticated exploit was needed — an unreviewed setting was enough.
Insecure APIs
APIs are the entry points connecting cloud services and third-party tools. Poorly authenticated or unencrypted APIs create exploitable vulnerabilities for attackers looking to access cloud data at scale.
The OWASP API Security Top 10 highlights risks like broken object-level authorization and broken authentication — flaws that let attackers assume other users' identities. Akamai reported a 94% growth in Layer 7 DDoS attacks targeting web applications and APIs from Q1 2023 through Q4 2024, confirming that APIs have become a primary attack vector.
Poor IAM and Privilege Abuse
Weak access controls—excessive permissions, shared credentials, or missing MFA—let both external attackers and malicious insiders move freely across cloud environments once they gain a foothold. Stolen or compromised credentials drove 16% of all data breaches in 2024, making them the most common initial attack vector.
When users or service accounts have more privileges than necessary, a single compromised credential can grant attackers access to vast amounts of sensitive data and critical infrastructure controls.
When users or service accounts have more privileges than necessary, a single compromised credential can grant attackers access to vast amounts of sensitive data and critical infrastructure controls.
Data Exposure and Lack of Visibility
Improper storage configurations and excessive permissions expose sensitive data — often before anyone notices. This risk is compounded when organizations lack real-time insight into who is accessing what across distributed cloud resources. Without comprehensive visibility, security teams cannot detect unauthorized access, unusual data transfers, or configuration changes that introduce new vulnerabilities.
Growing multi-cloud environments make this challenge even more complex, as security teams must monitor assets across Azure, AWS, GCP, and other platforms simultaneously.
DDoS Attacks and Account Compromise
Distributed Denial-of-Service (DDoS) attacks aim to overwhelm cloud systems and disrupt service availability. Cloudflare reported that DDoS attacks surged 121% in 2025, culminating in a record-breaking 31.4 Tbps attack launched by the Aisuru-Kimwolf botnet.
Meanwhile, credential stuffing and phishing attacks target user accounts to gain direct access to cloud infrastructure. These attacks exploit weak passwords, lack of MFA, and social engineering to compromise legitimate accounts, bypassing many traditional security controls.
Cloud Infrastructure Security Best Practices
Proactive cloud defense requires enforcing strict access controls, automating patch management, training staff, and rigorously testing incident response plans.
Implement Least Privilege Access and MFA
The principle of least privilege ensures every user, service, and application has access only to the resources required for their specific function. NIST SP 800-207 (Zero Trust Architecture) mandates that access rules be made as granular as possible to enforce least privileges needed to perform the action in the request.
Combine least privilege with mandatory MFA on all cloud accounts, especially privileged ones, to reduce the blast radius of any compromise. This dual approach dramatically limits what an attacker can access even if they successfully compromise a single credential.
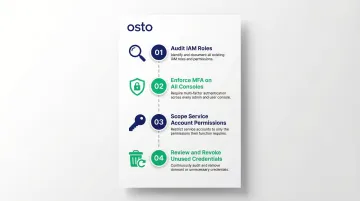
Implementation steps:
- Review and audit all IAM roles, removing excessive permissions
- Enforce MFA for all users accessing cloud management consoles
- Use service accounts with minimal, scoped permissions for automated processes
- Regularly review and revoke unused credentials and access keys
Encrypt Data at Rest and in Transit
Apply encryption consistently across all cloud layers using strong algorithms for stored data and secure protocols for data in transit. This ensures that even if attackers bypass other controls, they cannot read or misuse intercepted data.
Encryption requirements:
- At rest: Use AES-256 for databases, storage buckets, and virtual machine disks
- In transit: Enforce TLS 1.2 or TLS 1.3 for all API communications and data transfers
- Disable deprecated algorithms like 3DES or early TLS versions
- Implement automated certificate management to prevent expiration-related outages
Verify that encryption is explicitly enabled across all cloud environments and regions—default settings don't always apply the strongest protections, and gaps are easy to miss at scale.
Continuously Monitor and Audit Cloud Activity
Real-time monitoring using cloud-native or third-party tools alerts on unusual activity, unauthorized access, or configuration changes. Without continuous monitoring, security teams operate blind, discovering breaches only after significant damage has occurred.
Osto's centralized dashboard and threat detection give growing businesses continuous visibility across multi-cloud environments without requiring dedicated security operations staff. The platform auto-discovers 35+ resource types across Azure, AWS, and GCP, surfaces misconfigurations in near real-time, and gives lean teams clear remediation steps.
Monitoring priorities:
- Track all API calls and administrative actions
- Alert on configuration changes to critical resources
- Monitor for unusual data access patterns or transfers
- Review authentication logs for failed login attempts and credential abuse
Regularly Patch and Update
Unpatched VMs, containers, and infrastructure components are prime targets for exploitation. The Verizon DBIR noted that exploitation of vulnerabilities as a critical path action almost tripled in a single year, while Ponemon Institute research reveals that 60% of breach victims were breached due to an unpatched known vulnerability.
Automated patch management—integrated into CI/CD pipelines or DevOps workflows—keeps systems current and reduces vulnerability windows. Organizations should establish clear patching schedules, prioritize critical vulnerabilities, and test patches in non-production environments before deployment.
Develop and Test an Incident Response Plan
When a cloud breach occurs, an ad-hoc response sharply extends downtime and financial loss. IBM reports that organizations with high levels of incident response planning and testing saved $1.49 million compared to those with low levels.
Structure your incident response plan based on the NIST SP 800-61 Rev. 2 framework:
- Preparation: Establish your response capability and harden cloud systems before an incident occurs
- Detection and Analysis: Use CSPM and cloud-native SIEM tools to catch anomalous API calls or unauthorized access early
- Containment, Eradication, and Recovery: Isolate compromised instances and restore services from secure backups. Speed here directly determines your recovery cost.
- Post-Incident Activity: Run a lessons-learned review to close gaps and refine the process for next time

Test your plan regularly through tabletop exercises and simulations to ensure teams can respond effectively under pressure.
Educate Employees on Cloud Security
Human error and social engineering attacks—phishing, credential theft—remain leading causes of cloud breaches. The Verizon DBIR reports that the human element is involved in around 60% of breaches, while IBM X-Force research reveals that threat actors have shifted to using cloud hosting services to facilitate mass phishing campaigns.
Regular security training, phishing simulations, and clear security policies build a security-aware culture. Employees should understand how to identify suspicious emails, handle credentials securely, and report potential security incidents immediately.
The Shared Responsibility Model Explained
The shared responsibility model defines how security duties are split between cloud providers and customers. The cloud provider secures the underlying physical infrastructure—hardware, data centers, networking fabric—while the customer is responsible for securing everything they configure and deploy on top of it: data, access controls, application configurations, and identity management.
How Responsibility Shifts by Service Model
The division of security tasks varies significantly depending on the cloud service model:
| Responsibility Area | IaaS | PaaS | SaaS |
|---|---|---|---|
| Customer Data & Identities | Customer | Customer | Customer |
| Applications & Code | Customer | Shared | Provider/Shared |
| Network Controls & Firewalls | Customer | Shared | Provider |
| Operating System | Customer | Provider | Provider |
| Physical Infrastructure | Provider | Provider | Provider |
- IaaS: Customers manage the most — VMs, operating systems, and network configurations. The provider secures physical hardware and the hypervisor layer.
- PaaS: The provider handles OS patching and runtime environments. Customers focus on application code and data security.
- SaaS: The provider covers nearly all infrastructure security. Customers manage user access and data classification.
Across all three models — and across AWS, Microsoft Azure, and Google Cloud — the customer always retains full responsibility for their data, endpoint protection, and access management.
The Most Common Misconception
Many businesses assume the cloud provider handles all security. This is dangerous. Gartner estimates that 99% of cloud security failures will be the customer's fault through at least 2025. The Cloud Security Alliance corroborates this: traditional concerns like provider system vulnerabilities have plummeted. Customer-controlled risks now dominate — misconfiguration, inadequate change control, and insufficient identity management.
Misconfiguration by customers—not provider failures—accounts for the majority of cloud security incidents.
Frequently Asked Questions
What is cloud infrastructure security?
Cloud infrastructure security refers to the technologies, policies, and controls that protect cloud-based systems—including virtual networks, compute, storage, and APIs—from unauthorized access, misconfigurations, and cyberattacks. It focuses on securing the foundational infrastructure layer that all cloud workloads depend on.
How secure is cloud infrastructure?
Cloud infrastructure can be highly secure when properly configured, but security depends on both the cloud provider's physical protections and the customer's own controls. Misconfiguration and poor access management are the most common sources of cloud security incidents, not provider failures.
What are the four types of cloud security?
The four general types are infrastructure security, data security, identity security, and application security. Each addresses a distinct layer of the cloud stack—from protecting underlying resources and encrypting data to managing access controls and securing cloud-hosted APIs.
What is the shared responsibility model in cloud security?
The shared responsibility model splits security duties between the cloud provider and the customer. Providers secure the physical infrastructure; customers own configurations, data, and identity management. The exact split varies by service model: IaaS, PaaS, or SaaS.
What are the most common threats to cloud infrastructure?
The most frequent threats are misconfigurations, insecure APIs, weak IAM controls, DDoS attacks, insider threats, and phishing-based account compromises. Most are preventable with continuous monitoring, strict access policies, and automated cloud posture management.
