
Introduction
Most modern applications run on APIs — and attackers know it. Akamai recorded more than 311 billion web application and API attacks in 2024, a 33% year-over-year increase. Monthly attack volumes surged from nearly 14 billion at the start of 2023 to over 29 billion by October 2024 — a 65% jump in under two years.
What makes automated threats especially dangerous is their speed. They bypass traditional security controls and can go undetected for months. Automated bots now account for 51% of all web traffic, with malicious bots representing 37% of internet activity.
APIs are the preferred target because they're built to be machine-readable — and often lack the session-based controls that protect traditional web applications from credential stuffing, scraping, and DDoS abuse.
This article covers what automated API threats look like, what a strong API security solution actually does, and how to choose the right one for your organization's size and growth stage.
TLDR
- Automated threats like bots, credential stuffing, and DDoS attacks account for 44% of advanced bot activity targeting APIs
- Traditional perimeter security tools miss business logic abuse, making behavioral analysis and real-time threat detection essential for APIs
- Essential capabilities include automated API discovery, bot management, rate limiting, and AI-driven behavioral profiling
- Strong API security requires authentication on every endpoint, granular rate limiting, and continuous anomaly monitoring
- Growing businesses should prioritize agentless, cloud-native solutions that deploy in minutes and scale automatically
What Are Automated API Threats (And Why They're More Dangerous Than You Think)
Automated API threats are attacks executed by scripts or bots at machine speed, targeting endpoints to extract data, disrupt services, or compromise accounts. Unlike manual attacks, automated threats can test thousands of attack vectors simultaneously — and they're extremely difficult to distinguish from legitimate traffic.
Most Common Automated Threat Types
Credential stuffing and account takeover: Attackers hammer authentication endpoints with thousands of stolen username/password combinations per second. APIs are especially exposed here — they typically lack the CAPTCHA challenges and behavioral checks that protect web login forms. Industry research puts account takeover at 12% of all API bot attacks, with attackers using residential proxies to evade IP-based blocking.
Scraping and data harvesting: Bots systematically call endpoints to extract pricing data, user records, or proprietary content — accounting for 31% of all API bot activity. Attackers stay just under rate limits, draining datasets over days or weeks without triggering volumetric alerts.
DDoS and resource exhaustion: Floods of automated requests overwhelm backend services or exploit unrestricted resource consumption (OWASP API4:2023), locking out legitimate users. One documented attack hit 15 million requests per second against a financial API.
Business logic abuse: Scripts exploit API workflows — coupon stacking, inventory hoarding, promotional manipulation. These are the hardest attacks to catch because the requests are technically valid: correct syntax, real credentials, documented API contracts all followed. Payment and coupon fraud alone accounts for 26% of API bot attacks.

Why APIs Are Uniquely Vulnerable
What makes the threat types above so effective is structural. Two specific API categories draw disproportionate attack volume: shadow APIs (endpoints deployed outside standard approval processes) and zombie APIs (outdated interfaces left active but unmonitored). Only 15% of organizations have strong confidence in their API inventory accuracy, and one-third of all malicious API transactions target these undocumented endpoints.
Research shows that 44% of advanced bot activity now targets APIs, compared to just 10% targeting traditional web applications. This shift reflects attackers' understanding that APIs often lack the behavioral monitoring and session controls that make web applications harder to exploit at scale.
How API Security Solutions Defend Against Automated Threats
An API security solution sits between clients and your backend, inspecting and enforcing rules on every API call: authentication, authorization, rate limiting, anomaly detection, and threat blocking. Traditional firewalls filter by IP address or known signatures. Modern API security platforms go further — they understand the full context of each request and can detect abuse even when traffic looks completely legitimate.
Automated API Discovery Closes Blind Spots
Modern solutions continuously scan environments to catalog all active endpoints—including shadow, zombie, and undocumented APIs—ensuring no endpoint remains unguarded. Discovery works by passively analyzing network traffic to build dynamic inventories — no manual registration or documentation required. For growing businesses deploying microservices rapidly, this matters: 54% of organizations report difficulty managing API sprawl.
Platforms like Osto automatically discover and analyze APIs during the initial setup process, identifying endpoints that need protection without manual enumeration. As your API footprint expands, the inventory stays current without additional effort.
Behavioral Analysis and Traffic Baselining
Advanced solutions establish a baseline of normal API usage patterns (request frequency, payload size, endpoint sequencing) then flag deviations in real time that indicate bot activity or business logic abuse. 95% of API attacks now originate from authenticated users — valid credentials no longer equal benign intent.
AI-driven behavioral profiling (like Osto's AI-Driven Adaptive Web Protection Profiling) automatically detects, monitors, and intelligently profiles API traffic using machine learning. Anomalies that would escape manual review get flagged automatically — particularly valuable for teams without 24/7 monitoring capacity.
Bot Management and Rate Limiting
Smart rate limiting and blunt throttling aren't the same thing. Per-endpoint granularity lets organizations set different limits for different contexts:
- Authentication endpoints get strict limits to block credential-stuffing attempts
- Data retrieval endpoints can allow higher thresholds for legitimate integrations
- Context-aware controls track session identifiers and token usage, not just IP addresses
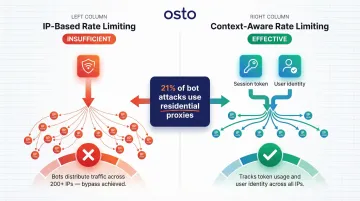
The reason this granularity matters: 21% of bot attacks use residential proxies, routing malicious traffic through real user devices to bypass IP reputation checks. One documented attack used more than 200 different IP addresses alongside a single authentication token — IP-based rate limits caught nothing.
WAF Integration and API-Specific Controls
Web Application Firewalls (WAFs) catch known attack signatures — SQL injection, cross-site scripting, and similar exploits. What they can't catch is business logic abuse. WAFs rely on pattern matching, so a malicious API call using perfectly valid syntax passes through undetected.
The most effective approach layers both:
- WAF: blocks known vulnerability signatures and common exploit patterns
- API security platform: baselines normal behavior, understands API schemas, and detects logical deviations that have no matching signature
Together, they cover the full attack surface — WAFs handle what's known; API-specific controls catch what isn't.
Key Features to Look For in an API Security Solution
Automated API Inventory and Shadow API Detection
Any solution that only protects APIs you manually register leaves critical gaps. When your team deploys microservices rapidly, automated discovery is essential. The platform should passively analyze network traffic to identify all active endpoints — including those deployed outside standard approval processes.
Centralized dashboards that surface shadow APIs let you identify and secure unknown endpoints before attackers find them first.
Real-Time Threat Detection with AI/ML Behavioral Profiling
Solutions that learn your API's normal traffic patterns and flag anomalies automatically outperform those relying purely on static rule sets that attackers can probe and evade. AI-driven adaptive protection is especially useful for teams lacking dedicated security operations centers or 24/7 monitoring capabilities.
Machine learning-based systems continuously analyze traffic without human intervention, detecting patterns and anomalies that would escape manual review — especially during off-hours when monitoring staff is unavailable.
Strong Authentication Enforcement and Access Control
Every endpoint must require verified identity. NIST SP 800-204 mandates that client-to-API gateway and service-to-service communication should use mutual TLS (mTLS) for authentication and encryption. The OWASP OAuth 2.0 Cheat Sheet recommends using Proof of Possession (PoP) tokens rather than standard Bearer tokens, as PoP tokens are cryptographically bound to specific clients, preventing token replay attacks.
When using JSON Web Tokens (JWT), keep expiry times as short as possible and strictly validate both authenticity and expiration — this directly prevents OWASP API2:2023 (Broken Authentication) exploits.
Rate Limiting, Quota Management, and Bot Mitigation Controls
These controls should be configurable per endpoint, user role, or API key — not one-size-fits-all. Granular configuration lets you distinguish high-frequency legitimate integrations from abusive automated traffic. For example:
- Authentication endpoints warrant strict per-minute limits
- Data retrieval endpoints serving mobile apps typically need higher thresholds
- API keys tied to known integrations can carry elevated quotas with audit trails
Adaptive rate limiting adjusts dynamically to traffic spikes, preventing false positives that block legitimate users during peak usage while still catching distributed attacks that stay just under static thresholds.
Audit Logging, Monitoring Dashboards, and Compliance Reporting
Continuous visibility is foundational — both for detecting active threats and satisfying compliance requirements. PCI DSS v4.0.1 Requirement 6.2.4 explicitly mandates protection against "attacks on business logic, including attempts to abuse or bypass application features and functionalities through the manipulation of APIs."
Prioritize solutions that deliver:
- Centralized audit logs covering all administrative changes and API security events
- Real-time dashboards that surface threats and overall security posture at a glance
- Enhanced authentication logging to support GDPR Article 32 and HIPAA transmission security requirements

Best Practices to Strengthen API Security Against Automated Threats
Adopt a Zero-Trust Posture for All API Endpoints
Never assume internal or partner-facing APIs are safe from automated abuse. 95% of API attacks originate from authenticated sources, meaning attackers already have valid credentials. Enforce authentication, validate input, and apply least-privilege access on every call—not just externally exposed endpoints. Continuous verification of every request—regardless of origin—limits lateral movement after initial compromise and reduces damage when credentials are stolen.
Implement Layered Defenses
No single tool covers the full threat surface. The most resilient approach stacks complementary controls:
- Edge layer: DDoS mitigation and volumetric attack protection
- Gateway layer: Authentication enforcement, rate limiting, and bot management
- Application layer: Business logic validation and behavioral monitoring
- Visibility layer: API discovery and inventory tracking for shadow and deprecated endpoints

WAFs handle known attack signatures, API gateways enforce access policies and rate limits, and behavioral monitoring detects logic abuse that passes protocol-level checks undetected.
Continuously Test and Audit Your API Inventory
Regularly scan for shadow and deprecated APIs, review authentication configurations, and run security assessments against your endpoints to catch misconfigurations before attackers do. The OWASP API Security Top 10 provides the baseline checklist every team should validate against.
Key OWASP categories to prioritize include:
- API1:2023 - Broken Object Level Authorization
- API2:2023 - Broken Authentication
- API4:2023 - Unrestricted Resource Consumption
- API6:2023 - Unrestricted Access to Sensitive Business Flows
- API9:2023 - Improper Inventory Management
Quarterly reviews catch configuration drift that point-in-time assessments miss—especially as new endpoints get added during product releases.
How to Choose the Right API Security Solution for Your Organization
Match the Solution to Your Growth Stage and Team Size
Enterprise tools with complex deployment models are often overkill for startups or scaling businesses. Solutions requiring weeks of setup, deep architectural knowledge, and dedicated SOC personnel create operational overhead that smaller teams cannot sustain.
Look for cloud-native, agentless architectures that connect to your infrastructure via APIs to provide full-stack visibility in minutes. Platforms emphasizing self-service onboarding allow teams to go from zero to full API visibility without requiring traffic rerouting or heavy agent-based deployments.
Evaluate Based on Your Specific Threat Exposure
57% of organizations experienced at least one data breach caused by API exploitation in the past two years. The right protection depends on where your exposure actually sits:
- High-risk data APIs (payments, logins, PII): prioritize bot management, credential stuffing protection, and behavioral analysis
- Sprawling microservices environments: prioritize automated discovery and inventory management that keeps pace with rapid deployment cycles
Check for Integration Compatibility and Deployment Flexibility
The best solution fits into your existing CI/CD pipeline, cloud environment, and developer workflows without requiring a large security team to operate. Look for solutions offering:
- Centralized dashboards with unified visibility across Azure, AWS, and GCP
- Automated alerting with prioritized risk queues
- Support for major cloud providers with minimal configuration
- API-based integrations that don't require infrastructure changes
Osto covers all four of these requirements — its automated periodic discovery identifies cloud resources across Azure, AWS, and GCP, surfacing enriched metadata in a single consolidated inventory without agent-based deployment or manual configuration.
Frequently Asked Questions
What's the best API security solution for preventing automated threats?
The best solution depends on your architecture and threat exposure. Prioritize platforms that combine real-time behavioral analysis, bot management, and automated API discovery — with low operational overhead. Agentless, cloud-native solutions that deploy quickly are the right fit for most growing businesses.
What are the best security practices for API?
Core practices include:
- Enforce authentication on every endpoint using OAuth2, JWT with short expiry times, or mTLS
- Apply granular rate limiting per endpoint and user role — not just IP-based throttling
- Monitor all API traffic continuously for behavioral anomalies
- Audit your full API inventory, including shadow APIs, against the OWASP API Security Top 10
What types of automated threats target APIs most frequently?
The most common categories are:
- Scraping and data harvesting (31% of attacks)
- Business logic abuse via automated scripts (26% — payment and coupon fraud)
- Credential stuffing and account takeover (12%)
- DDoS and resource exhaustion attacks
These threats operate at machine speed and often use valid credentials, making them difficult to detect without behavioral analysis.
What is the difference between a WAF and an API security solution?
A WAF filters based on known attack signatures and HTTP patterns, catching vulnerabilities like SQL injection. Purpose-built API security solutions add behavioral analysis, API-specific threat detection, and automated discovery — capabilities WAFs aren't designed to handle, and which are essential for catching business logic abuse where malicious calls use perfectly valid syntax.
Does rate limiting alone protect against automated API threats?
Rate limiting is a necessary first layer but insufficient on its own. Sophisticated bots distribute requests across hundreds of IP addresses and time intervals to stay under rate limits, requiring behavioral monitoring and bot management for complete protection. Context-aware controls that track session identifiers and token usage outperform simple IP-based throttling.