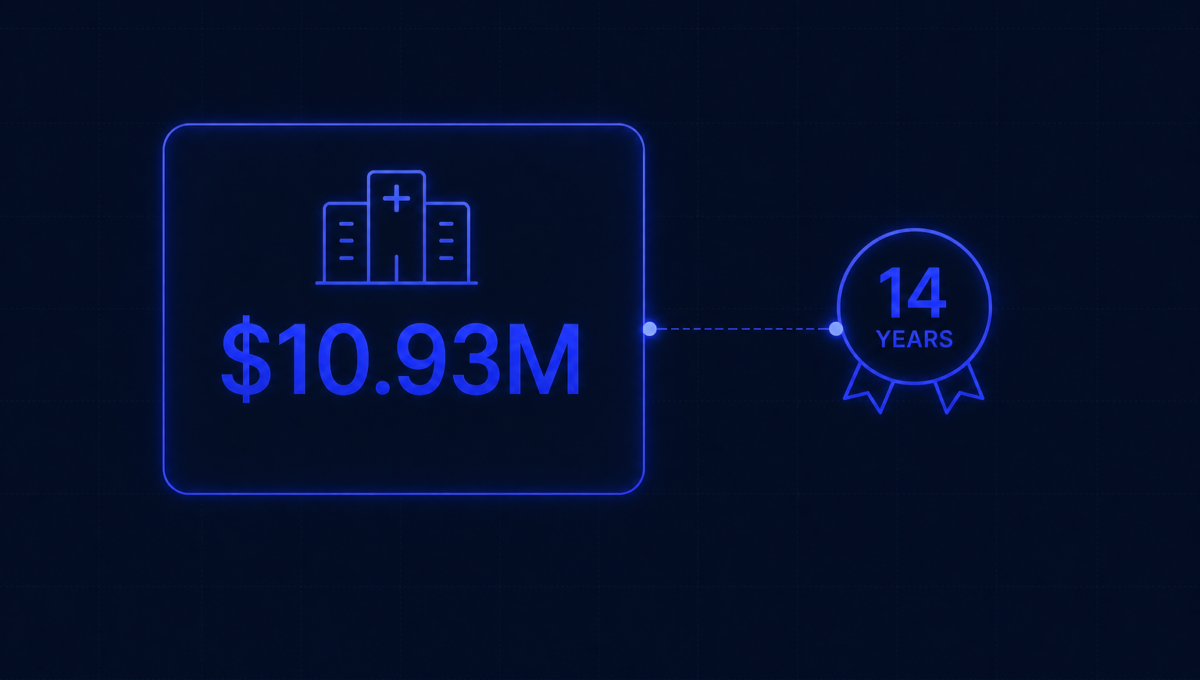
IBM’s 2025 Cost of a Data Breach Report found that the average healthcare breach costs $7.42 million, more than any other industry. This is the 14th consecutive year healthcare has held that position. The number has fluctuated — it peaked at $10.93 million in 2023 — but healthcare has never left the top spot since IBM started tracking this in 2011.
The reason isn’t simply that medical records are valuable, though they are. A stolen medical record sells for $260 to $310 on dark web markets, roughly ten times the value of a stolen credit card. The reason healthcare breaches cost so much is structural: detection takes longer, containment is harder, the regulatory consequences are more severe, and the operational impact extends further.
Healthcare takes five weeks longer than average, and in that five extra weeks, data is being accessed, exfiltrated, and in some cases sold.
What this means if you’re building a healthtech company
You’re building in the most expensive sector for security failures. That context shapes everything about how you should approach security infrastructure and compliance.
It also creates a practical reality in enterprise sales: every hospital, health plan, and large medical group has a procurement security review process that reflects this exposure. They’ve been breached, or they’ve watched their peers get breached, or they’ve read the IBM report. When your clinical AI tool or health data platform enters their vendor assessment process, the rigor they apply reflects $7.42 million in average losses, not excessive caution.
Understanding this makes the healthcare sales process make more sense. The IT security review that takes six weeks, the lawyer who needs to review the Business Associate Agreement in detail, the compliance team that wants evidence of a penetration test. These aren’t obstacles. They’re a rational response to a real industry risk profile.
The three attack patterns hitting healthtech companies hardest
16% of breaches
The most common initial access vector in healthcare. A KnowBe4 study found 41.9% of healthcare organisations susceptible to phishing simulations, versus 39.2% for insurance and 36.5% for retail. It’s a combination of high workforce turnover, constant urgency, and frequent external communications that creates the conditions phishing exploits.
17% of attacks
The average demand from a healthcare ransomware attacker is $7 million, matching almost exactly the average breach cost. Healthcare organisations are targeted because they’re considered more likely to pay: downtime affects patient care, and the pressure to restore systems is immediate in a way it isn’t for other sectors.
Fastest growing
The Change Healthcare attack, which affected 192.7 million people and cost billions, started with a compromised credential on a vendor’s remote access portal. A single missing MFA setting at a vendor became the largest healthcare data breach in US history.
The HIPAA Security Rule update that changes your obligations
In early 2025, HHS proposed the first major overhaul of the HIPAA Security Rule since 2003. The proposed changes, if finalised, would eliminate the distinction between ‘required’ and ‘addressable’ implementation specifications. Currently, certain HIPAA controls, including encryption and multi-factor authentication, are ‘addressable,’ meaning organisations can document why they chose not to implement them. Under the proposed rules, they become mandatory with very limited exceptions.
This is a direct regulatory response to breach root causes. Most large healthcare breaches involve a failure of controls that were ‘addressable’ under the current framework. HHS is closing that gap.
If you’re building a healthtech product and your security architecture was designed to the current HIPAA framework, the proposed changes are worth reviewing now, not when the final rule is published.
The practical security baseline for healthtech companies
Given the industry context — $7.42 million average breach cost and 14 years at the top — what does a responsible security baseline look like for a 20-50 person healthtech company?
-
✓
Application protection beyond HTTPS. A WAF in front of your patient portal or clinical interface, blocking known attack patterns. Your application code is one layer. The WAF is the layer in front of it. -
✓
Endpoint detection and response on every device that can access patient data. Not antivirus. EDR that monitors behavioural anomalies — unusual access patterns, lateral movement, credential harvesting. -
✓
Audit logs for every PHI access event. Who accessed which patient record, when, from what device, and what they did. HIPAA requires this. Breach investigation requires it. -
✓
A penetration test annually, scoped to your patient-data-handling infrastructure. The test report is evidence for the hospital’s vendor security review. The findings, fixed and documented, are evidence that you manage risk actively.
Healthcare has the most expensive breaches because it has the most valuable data and the most pressure to keep systems running. Healthtech companies inherit both of those characteristics the moment they handle patient data.
Building security infrastructure that reflects this reality isn’t just about compliance. It’s about building something that can survive the inevitable security event without it becoming the defining chapter in your company’s story.
The baseline described above — WAF, EDR, audit logging, annual pen test — is what Osto deploys for healthtech teams, so your security posture is ready before the hospital’s vendor questionnaire arrives.